In the age of GenAI, bad actors can deliver attacks at a speed, sophistication, and scale like never before. They can task agents with scraping social media to create highly personalized attacks. They can generate hundreds of message variants in order to probe security systems for weakness. They can continuously evaluate successes and failures and use attack analytics to iterate autonomously.
With all of this AI tooling that enables them to create near-perfect attacks with minimal effort (and skill), they can also still create some of the worst scam attempts we’ve ever seen. So without further ado, we present this year’s batch of LOL-worthy scams caught by Sublime.
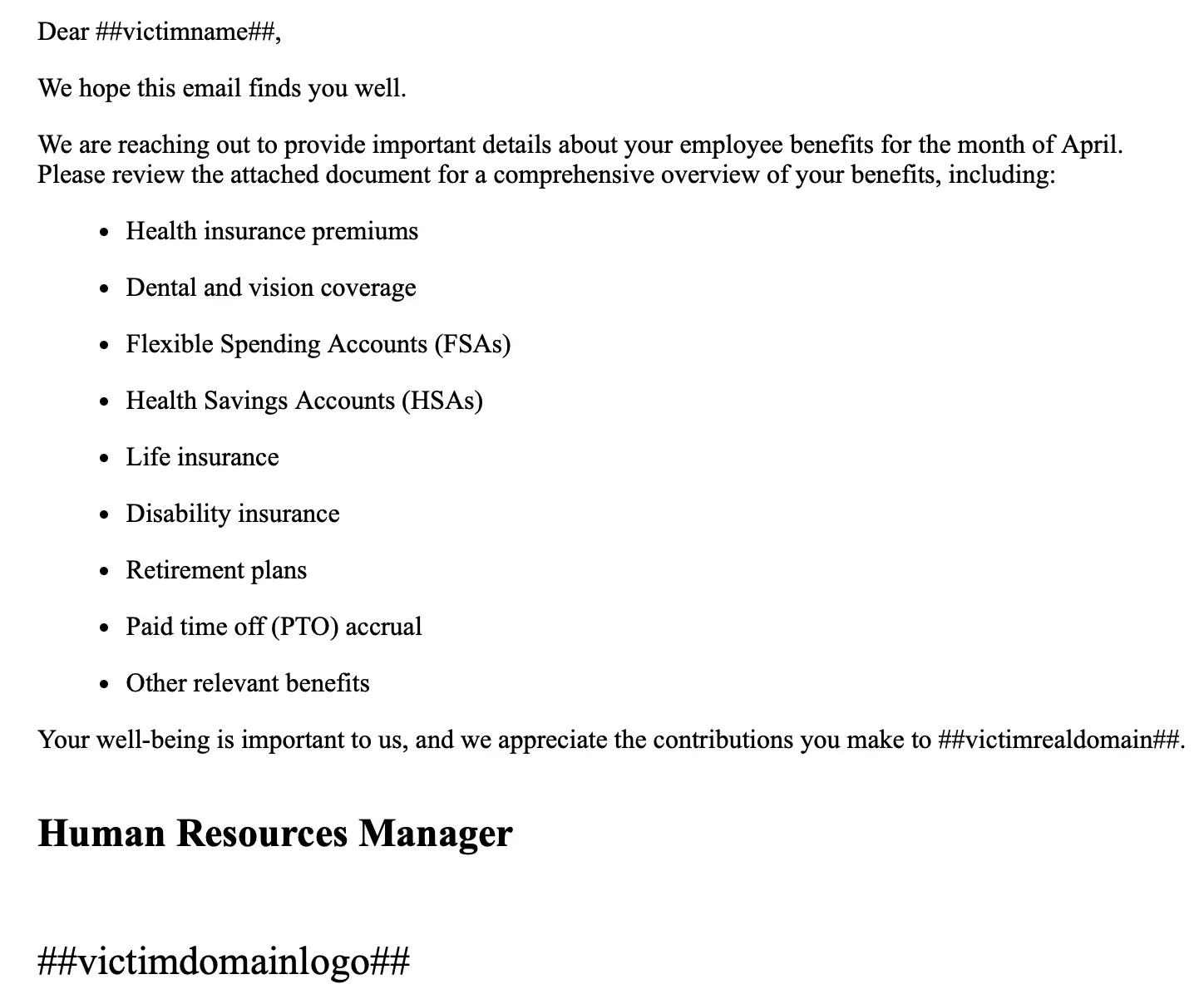
THIS ATTACK ONLY WORKS ON WINDOWS!
Most malware attacks are Windows-specific. Knowing this, some adversaries will do their homework to determine if a target is running a Windows machine before attacking. Others will use a “spray and pray” approach knowing that there’s a good chance their target is on Windows. And then, there are those that will specifically tell you (five times) to use a PC to open their attack and that you should definitely not open it on another operating system.
The fact that this attacker sent their fake Evite attack from a Yahoo address was a little surprising, though. An admin must’ve shut down their AOL account.
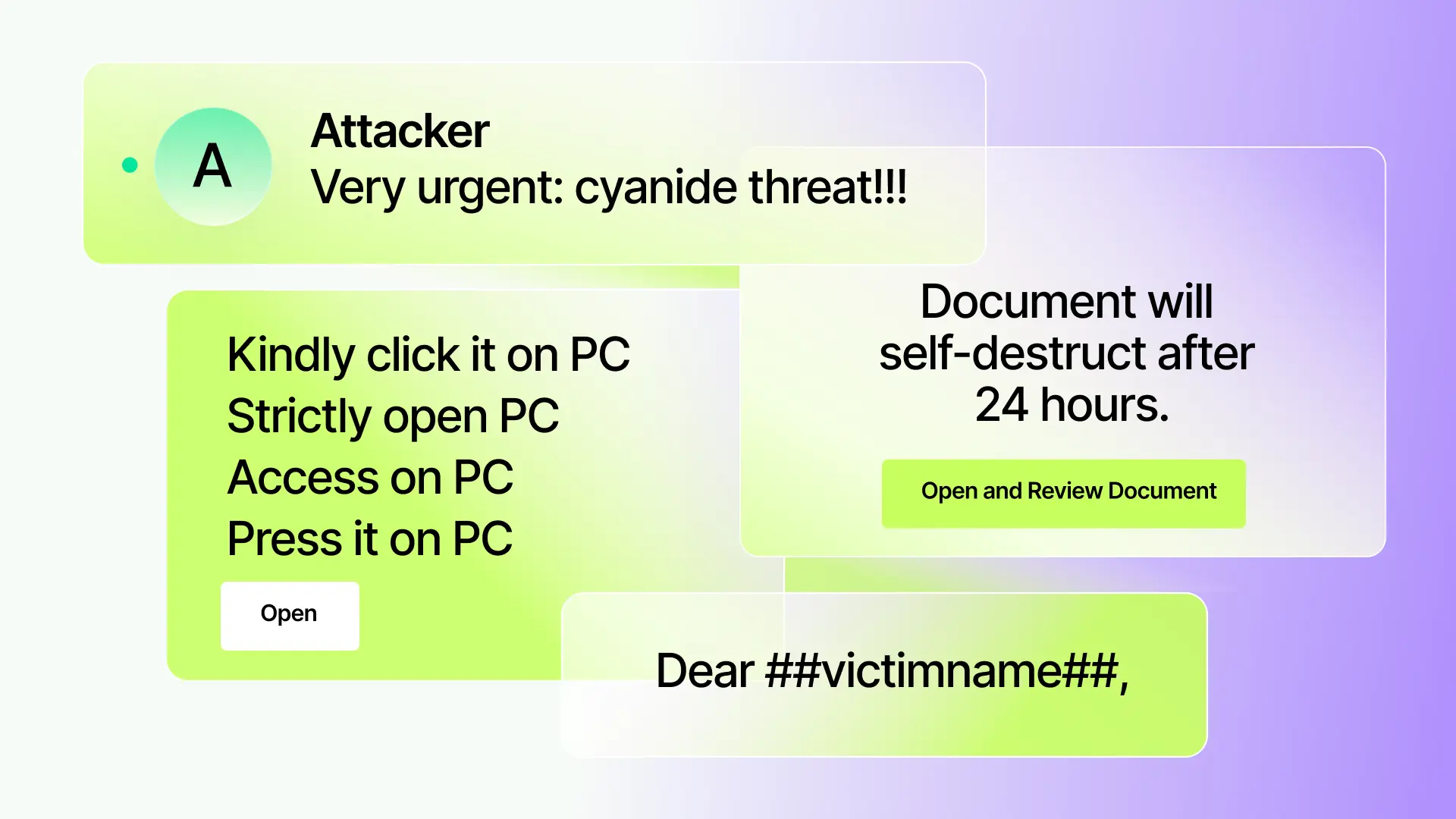
Mission: Impossible – Rogue Document Sharing Protocol
Urgency is a common manipulation tactic for attackers (and why we use ML to detect it). Adversaries use a ticking clock to get their targets to click links quickly, before they can pause and ponder the legitimacy of the message. This greatly increases the chances of attack success, which is very important when an attack includes the line “Document will self-destruct after 24 hours,” which itself drops its chances of success down to around 0%.
Maybe one person shouldn’t be in charge of all food
If the threat of a self-destructing document doesn’t work, then it’s time to go big. How big? “Poison the entire country” big. And show you’re a super serious, unified team of terrorists by signing it as a pluralized pirate. Yarrrs!
I’ll have… one of everything
Not every attacker has the time to task a fleet of AI agents with doing their work for them. For the busy adversary on the go, we present the “full menu” approach. Start by poorly impersonating a well-known sender. Then create a fake thread from the intended target (fake threads are so hot right now). In that thread, make sure you include: 1) current events, 2) entertainment, 3) polite inquiry, and 4) crime report. Finally, include a fake response to the fake thread so the target knows that they in fact started this conversation, not the attacker.
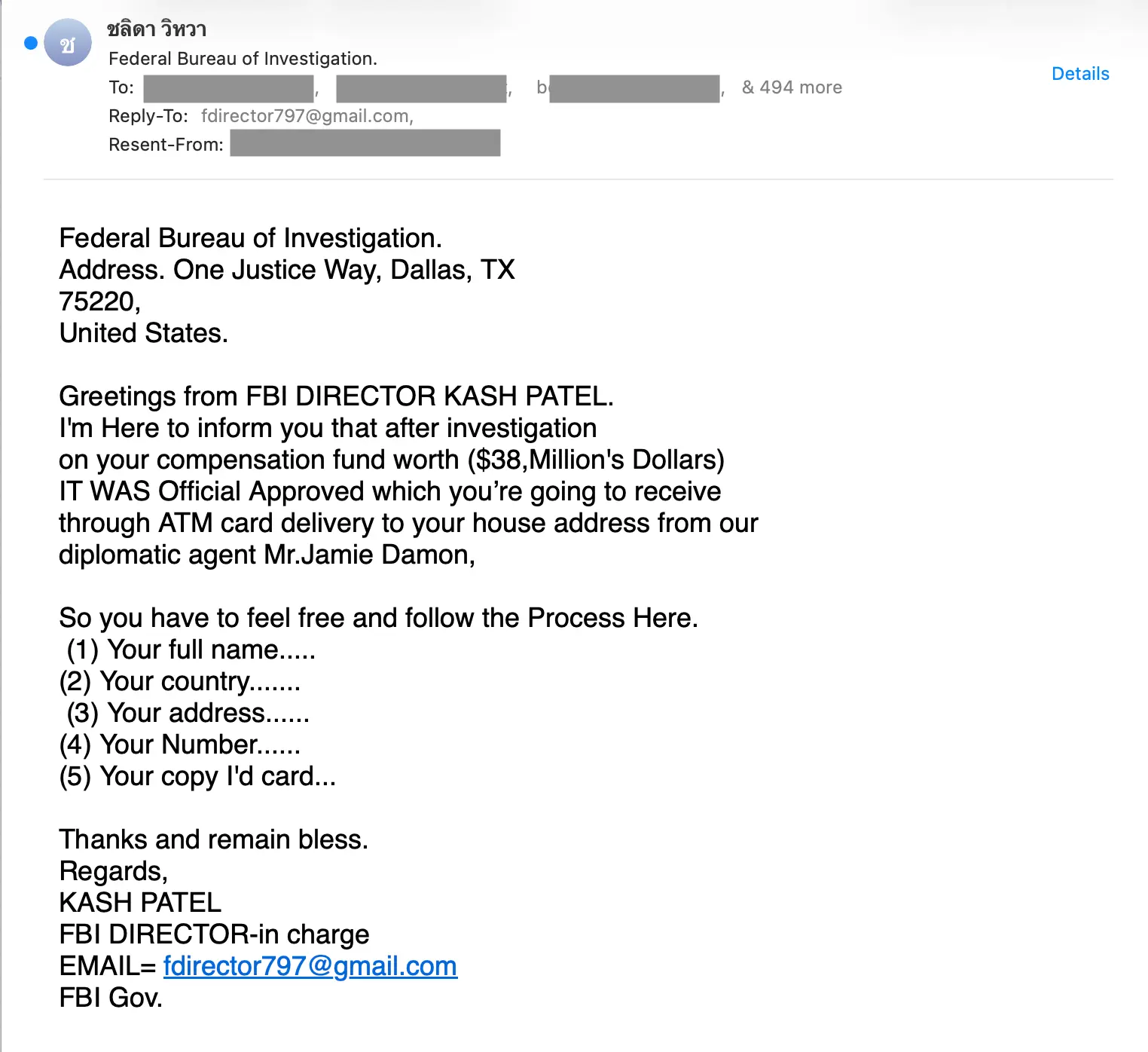
Cash from Kash
While it’s well-known that the FBI never randomly hands out $38,000,000 to somebody, what makes this attack so convincing is that the FBI is randomly handing out $38,000,000 to 497 somebodies – all of whom are CC’d (not BCC’d) since that sort of life-changing windfall should not be delivered anonymously. Now, we’re not economists, but if the government is trying to balance the budget, they probably shouldn’t be handing out nearly $19,000,000,000 in ATM cards. Just a thought.
No escaping a name
Occupational surnames have existed for nearly a millennium in the western world. If your last name is Carpenter, chances are someone in your family was pretty good with a hammer. Baker? You better believe your family was friends with some Millers. Unfortunately, for some, this means being cursed to a predetermined life of cybercrime.
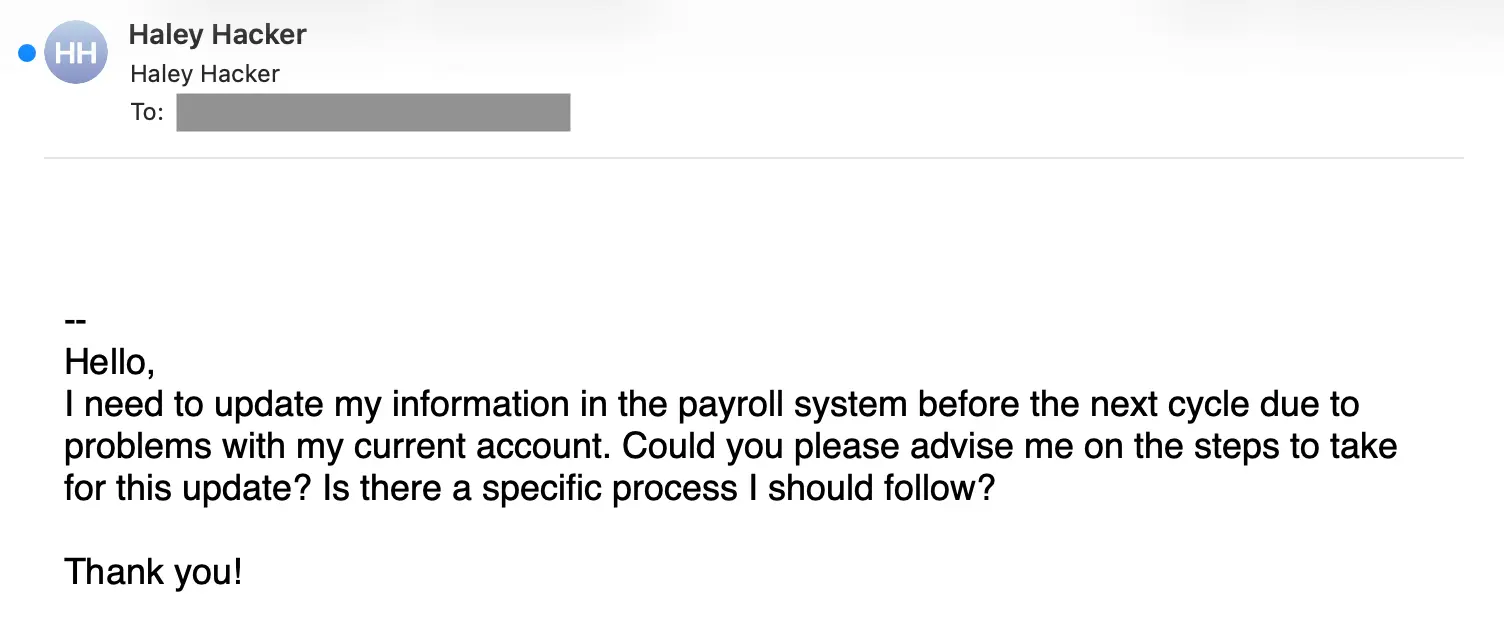
We don’t think Haley Hacker is a truly bad person, we just think they were born to a bad name. Just like Philomena Phisher, Scotty Scamson, and Barbara BEC.
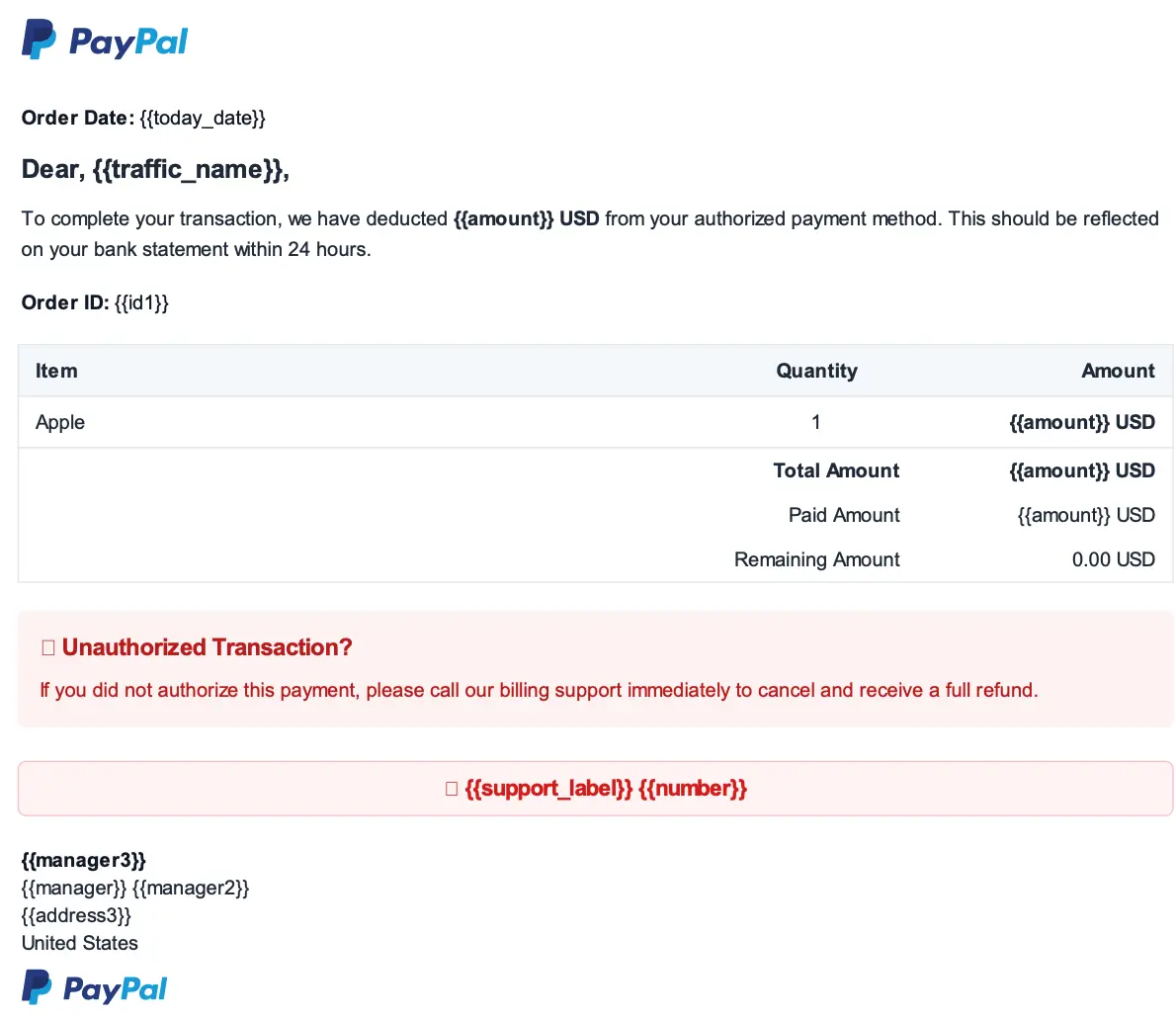
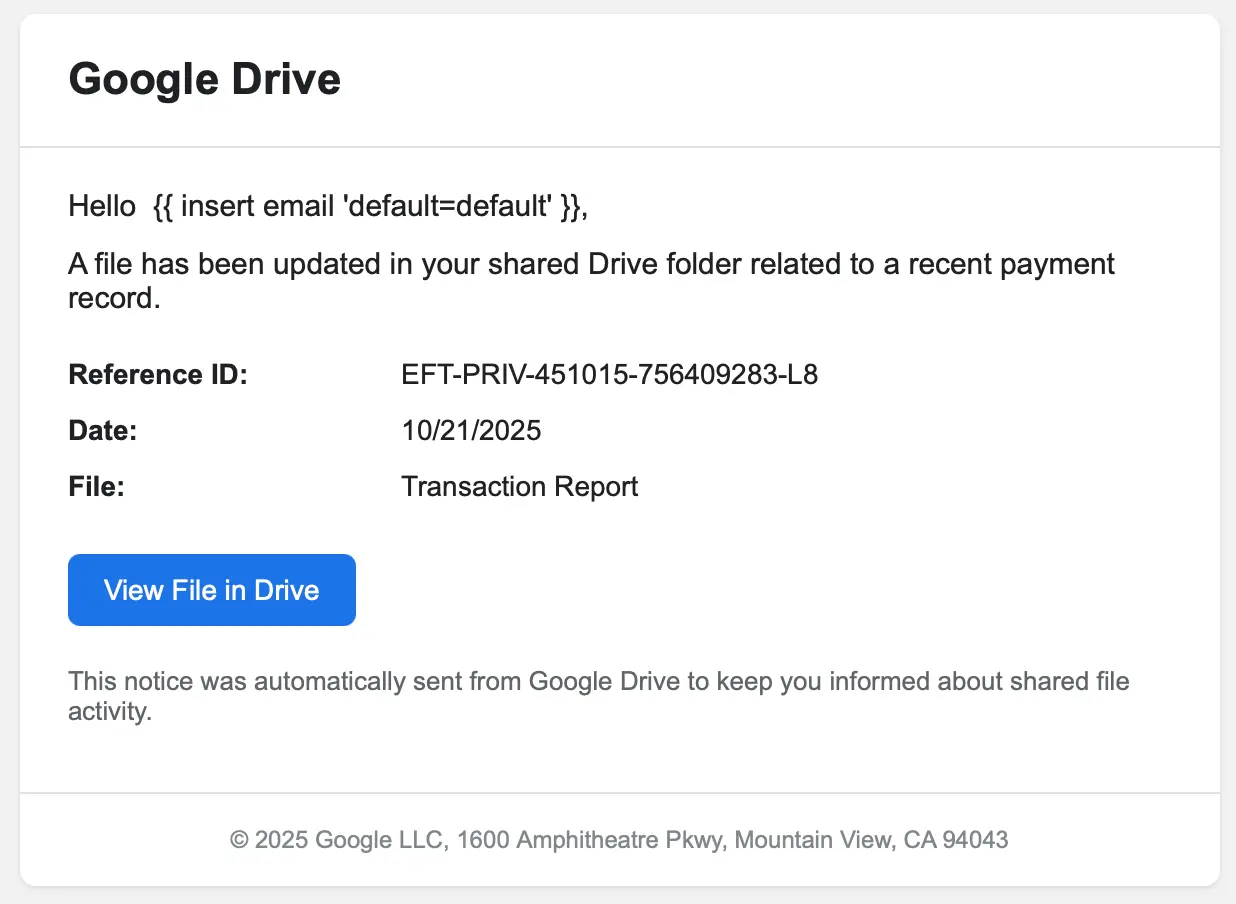
{{descriptive_h2}}
Finally, we’ll wrap our {{year}} April Fool’s blog post with {{quantity}} examples of attackers too lazy to populate the form fill fields on their attack templates. We’ve all seen whoopsies like this in marketing blasts, but for some reason it’s so much {{comparative_adjective}} when {{adversaries_synonym}} do it.
Make 2026 a year of “tee hee” not “oh no”
We hope you enjoyed this year’s batch of funny fails. While it’s nice to have a laugh at botched attacks and scams, it’s even nicer to never see them at all. That's why Sublime's AI agents – ASA (Autonomous Security Analyst) and ADÉ (Autonomous Detection Engineer) – detect and close coverage gaps created by novel attacks, autonomously. As fast as attackers can iterate, Sublime can defend.
If you want more chuckles, read our 2025 post. Otherwise, if you enjoyed these examples, check out our regular Attack Spotlights. Here are some recent posts:
Get the latest
Sublime releases, detections, blogs, events, and more directly to your inbox.


.avif)
