
Operationalize your email threat intelligence
Leverage your threat intelligence to block left of boom or hunt for targeted campaigns over historical data.
Flexible threat intel integration for enhanced protection and attribution
Supplement Sublime’s integrated threat intelligence with your own sources.

Real-time prevention
Create Detection Rules to block inbound threats.

Threat hunting
Hunt retroactively over historical data to determine if you were targeted by a known campaign.
IOC or behavioral
Sublime’s flexible Message Query Language enables both detection and hunting using IOCs or complex attacker behavior.
From a threat intelligence perspective, Sublime is offering us a whole new paradigm in detection opportunities and controls. Leveraging Sublime's API, we can push our collections of indicators to include domains, IPs, hashes, etc. to Sublime and have immediate enforcement and blocking in real time.
Manage your threat intelligence
Add feeds and manage org-specific detections right from the platform.

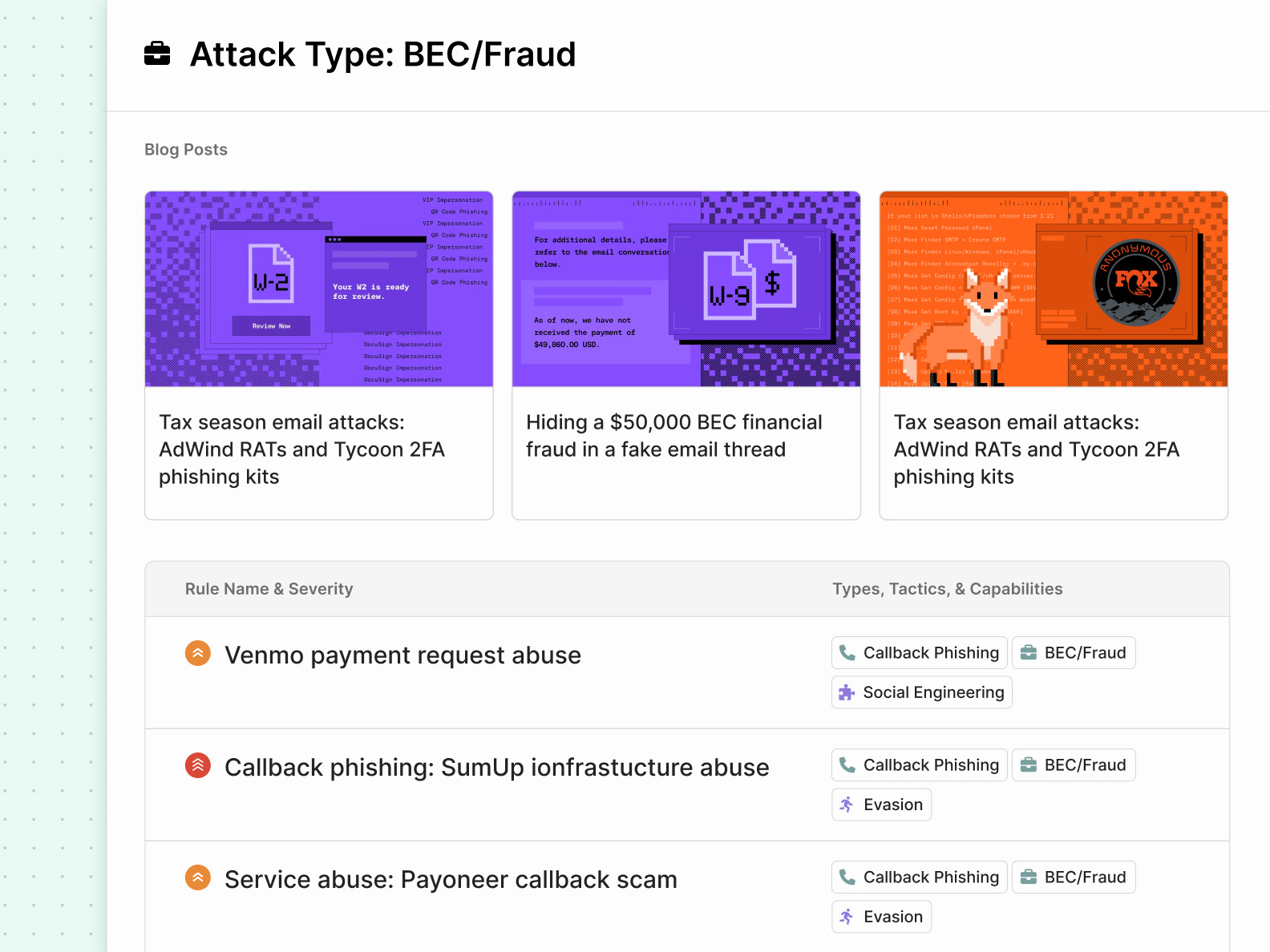
Leverage our Email Threat Framework
Email Threat Framework makes it easy to explore Sublime’s detection coverage, as well as learn about different attack TTPs, and detection methods.
More threat detection features
Sublime offers a wide range of features for threat detection and email attack prevention.

Connect unlimited threat intelligence feeds through our comprehensive threat detection tool.

Automatically sync new intelligence across all detection rules and systems.

Build tailored detection logic using MQL and your proprietary intelligence.
Deploy both public and private YARA rules for advanced malware detection.

Seamless integration with third-party intelligence providers and internal systems.

Centralized control over all intelligence sources from a single platform.

Enhance email analysis with contextual threat intelligence in real-time.

Combine multiple detection signals for improved accuracy and reduced false positives.
What our customers are saying
Latest from Sublime
Ready to operationalize your threat intelligence?
See how Sublime's threat detection software can integrate all your intelligence sources for comprehensive email security protection.
Frequently asked questions
What makes Sublime's threat detection software different from other solutions?
Sublime's threat detection tool integrates unlimited intelligence sources, provides transparent detection logic, and allows custom rule creation using MQL, unlike black-box alternatives that limit intelligence operationalization.
How does advanced threat detection software improve email security?
Advanced threat detection software correlates multiple intelligence feeds in real-time, identifies sophisticated attacks through behavioral analysis, and automatically updates detection rules based on emerging threats for comprehensive protection.
Can cyber threat detection tools integrate with existing security infrastructure?
Yes, Sublime's cyber threat detection software offers robust APIs for SIEM integration, supports custom webhooks, and connects with existing threat intelligence platforms without disrupting current workflows.
What types of threat intelligence feeds work with your threat detection automation software?
Our threat detection automation software supports YARA rules, IOC feeds, private intelligence services, OSINT sources, custom GitHub repositories, and proprietary detection rules for comprehensive coverage.
How quickly can threat detection and response software deploy new intelligence?
Sublime's threat detection and response software updates intelligence feeds in real-time, with new rules and IOCs becoming active within minutes of ingestion for immediate threat protection.
Now is the time
See how Sublime delivers autonomous protection by default, with control on demand.
.avif)


.png)
.svg)











