
Behavioral threat hunting in email
Hunt threats in your organization’s inboxes and turn the tables on bad actors with the most advanced threat hunting platform.
Your email threat hunting platform
Sublime gives you the tools you need to find the threat patterns hidden across your inboxes with our comprehensive threat hunting platform.

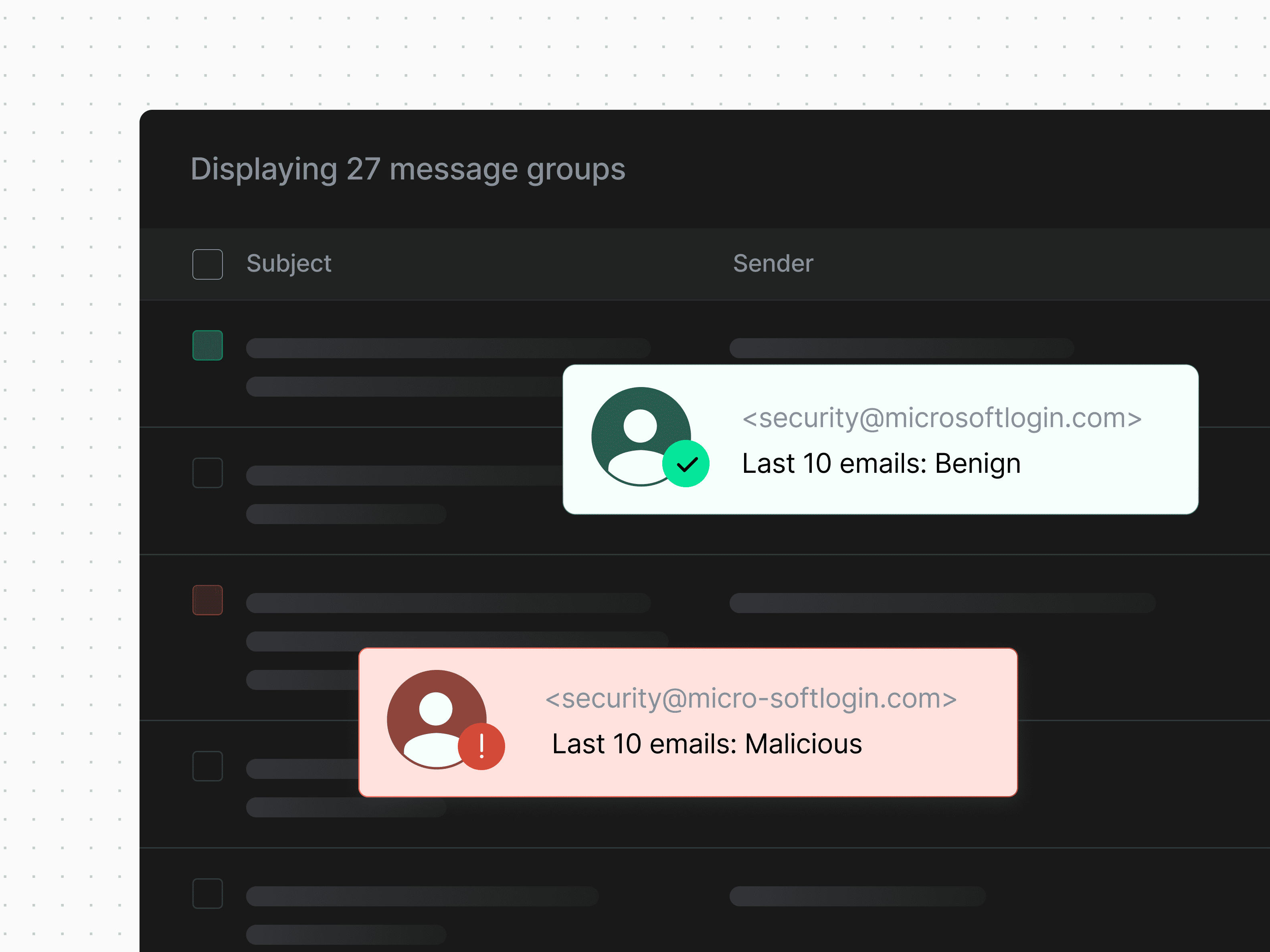
Historical sender context
Sublime tracks historical sender data to make decisions about future messages from that sender’s organization.

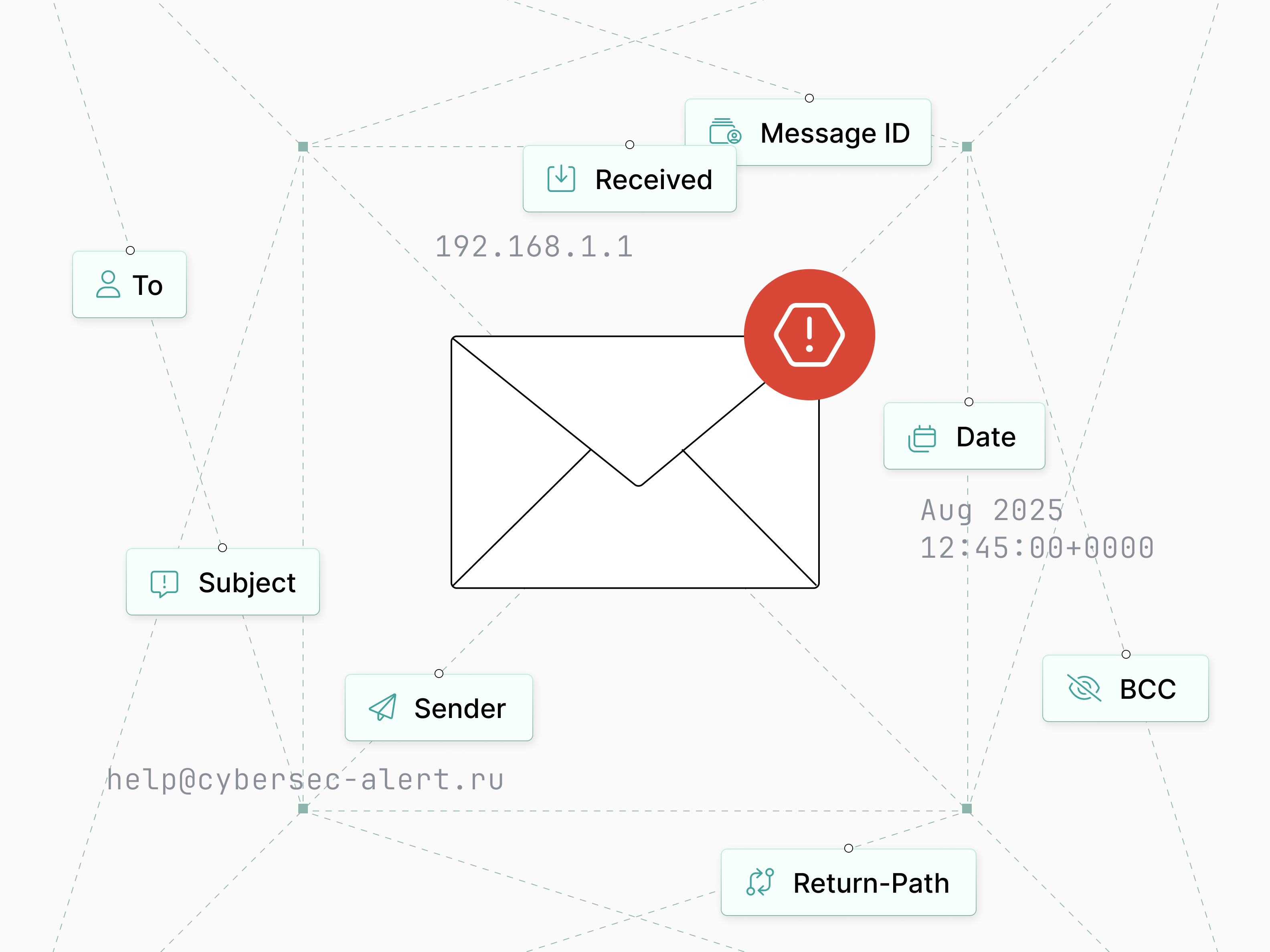
Signals within infrastructure
Threats can be surfaced through infrastructure clues, like unusual hop patterns, SPF/DMARC failures, and suspicious sending hosts.
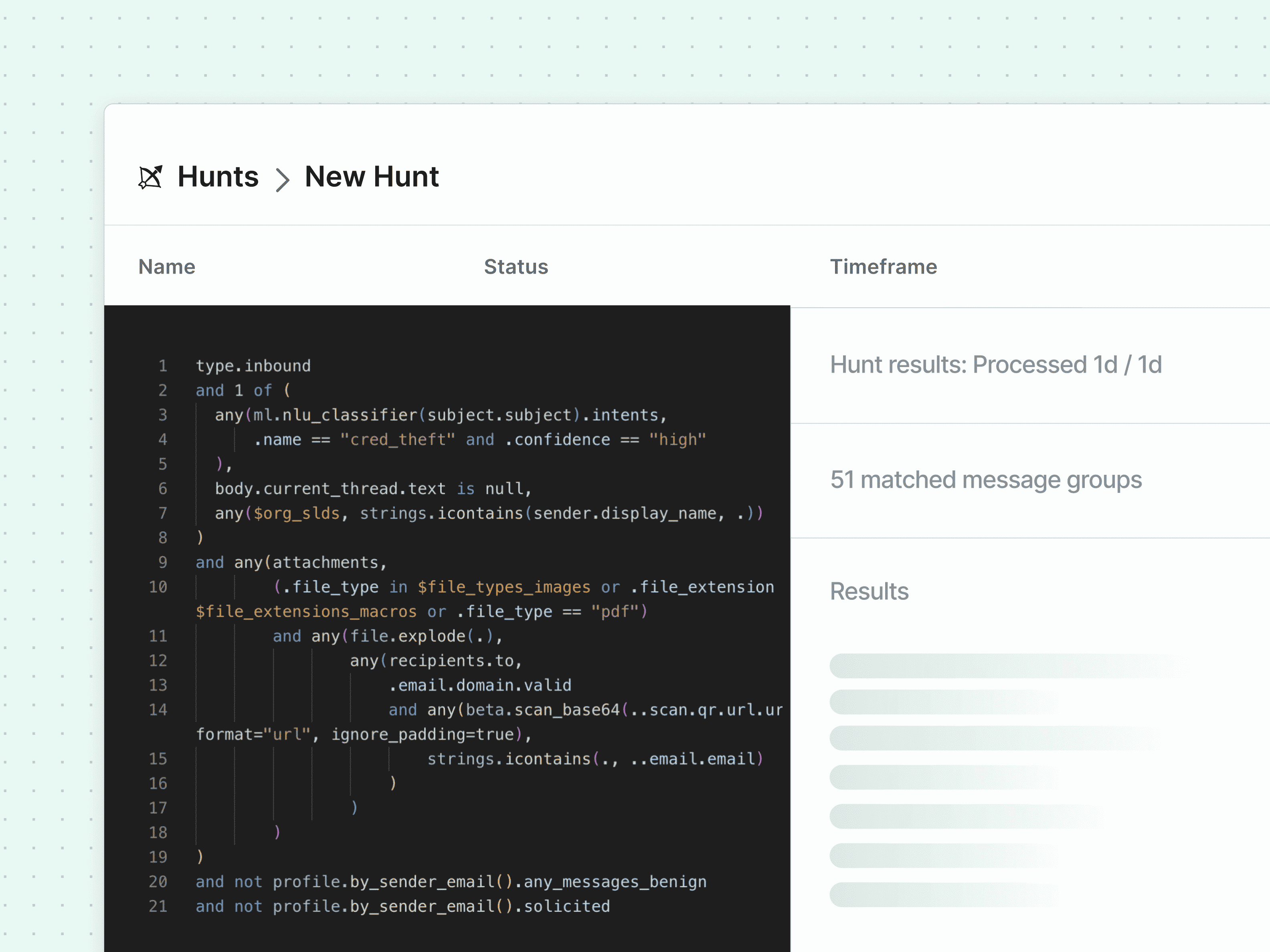
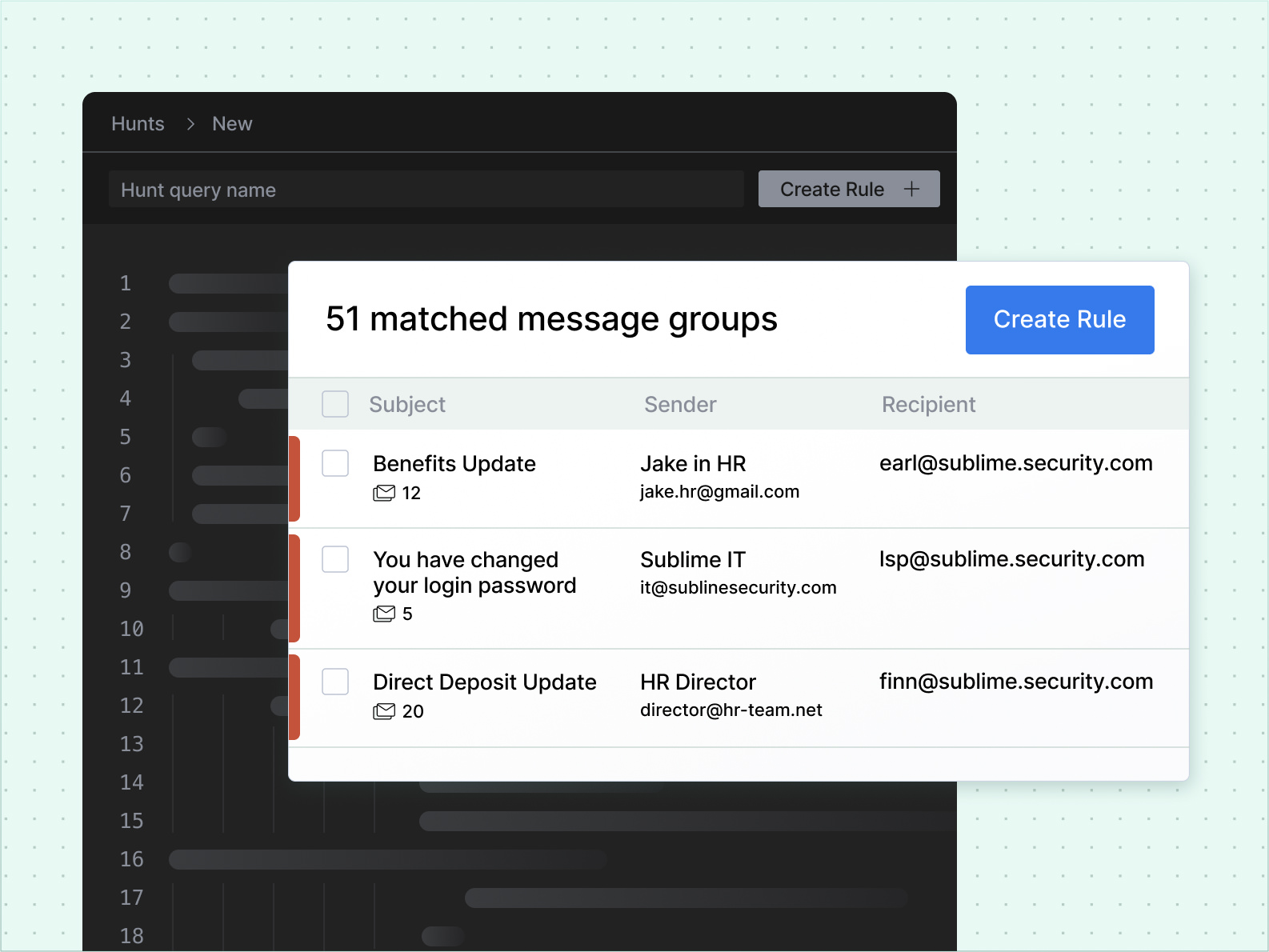
Hunts <-> Rules
With Message Query Language (MQL), analysts can turn a Hunt into a Detection Rule and vice versa in a few clicks.
From a threat intelligence perspective, Sublime is offering us a whole new paradigm in detection opportunities and controls. Leveraging Sublime's API, we can push our collections of indicators to include domains, IPs, hashes, etc. to Sublime and have immediate enforcement and blocking in real time.
Hunt and remediate from one screen
Hunt for threats in inboxes and then remediate malicious emails right from the results.

Hunt across every signal
Attackers leave behind breadcrumbs in language, visual cues, infrastructure, sender behavior, and more. Sublime's threat hunting platform can help you find them all.
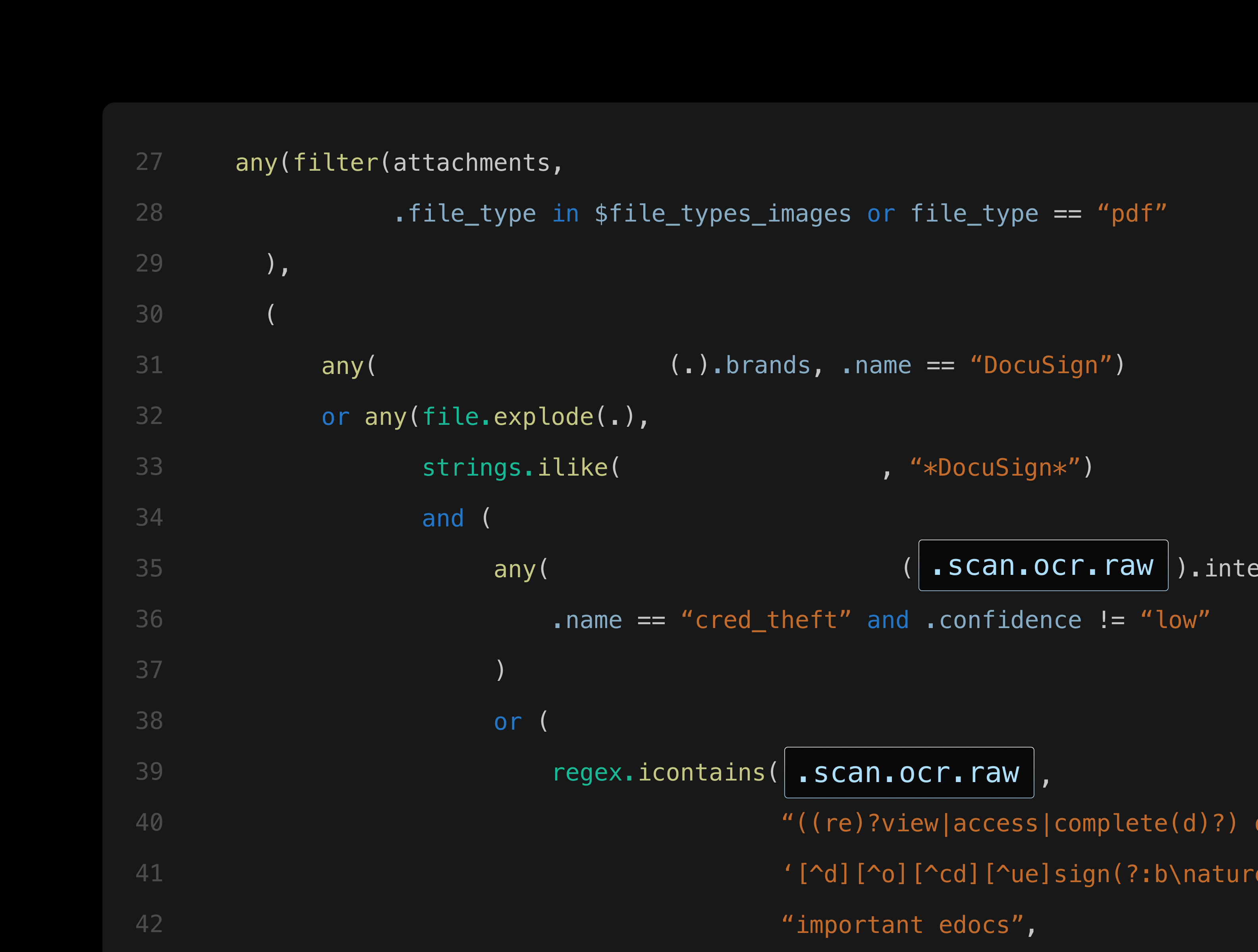
Sublime lets you hunt threats using deep, flexible primitives, AI-powered functions, and external enrichments like link analysis, WHOIS, domain age, logo detect, string patterns and behavioral context all in one unified threat hunting platform built for real investigation.
Put the latest threat intelligence to use by hunting down novel attacks using their known behaviors and TTPs.
Sublime uses historical data - like previous verdicts, time known, whether contact was solicited, and more - to inform sender reputation.
Infrastructure metadata free file hosts, free email providers, known-malicious domains, failed authentication, and more will expose even the most well-crafted attack campaign.
Hunts and Detection Rules are both written in MQL, so a successful Hunt can be turned into a powerful Detection Rule that prevents future attacks.
Complete threat hunting platform capabilities
Advanced features designed for modern security teams who need comprehensive email threat hunting.

Write complex queries to hunt threats with precision and flexibility.

Hunt over historical email data using custom YARA signatures.

Group similar attacks automatically to accelerate investigation workflows.

Leverage threat intelligence feeds and enrichment sources for deeper context.

Safely isolate suspicious messages automatically or with a single click.

Transform successful hunts into automated detection rules instantly.

Analyze sending patterns, authentication failures, and hosting providers.

Identify suspicious sender behaviors and communication patterns.
What our customers are saying
Latest from Sublime
Ready to transform your email security?
Experience the power of Sublime's threat hunting platform and see how behavioral threat hunting can protect your organization.
Frequently asked questions
What makes Sublime's threat hunting platform different from traditional email security?
Unlike one-size-fits-all solutions, Sublime provides full transparency and explainability. For advanced teams, our platform is fully extensible, allowing you to hunt for novel and organization-specific threats using MQL.
Can I convert threat hunts into automated detection rules?
Yes, Sublime's threat hunting platform uses MQL for both hunting and detection coverage. Any successful hunt can be converted into an automated detection with a few clicks, enabling proactive protection against similar future threats.
What types of infrastructure signals does the threat hunting platform analyze?
Sublime examines SPF/DMARC failures, unusual hop patterns, suspicious sending hosts, free email providers, domain age, hosting reputation, and authentication changes to identify potential threats through infrastructure analysis.
How does historical sender context improve threat hunting accuracy?
The threat hunting platform maintains detailed sender profiles including previous verdicts, relationship history, communication frequency, and trust levels. This context helps distinguish between legitimate senders and potential threats with higher precision.
Now is the time
See how Sublime delivers autonomous protection by default, with control on demand.
.avif)


.png)
.svg)











