Hang up on callback phishing with Sublime
A single successful callback phishing attack opens the door for financial scams, ransomware, and more. Sublime's AI-powered callback phishing detection keeps callback phish out of inboxes and safely in quarantine.

Callback phishing in a nutshell
Callback phishing, or telephone-oriented attack delivery (TOAD), is an attack that usually begins with a fake invoice or receipt.
These attacks often appear to be a charge from a well-known company, and the goal is to get a target to call a number for assistance. Once on the phone, the attacker often poses as a customer service representative, asking for personal information, offers to help "cancel the charge," or convinces the target to install remote support software.
From there, they can access the device, steal sensitive data, or walk a target through a fake refund process that results in real financial loss.
Our previous solution delivered a well-crafted phishing email to our technology team, but Sublime identified it as malicious immediately. That was our first 'oh yeah, Sublime is way better' moment.
What makes callback phishing so slippery
Callback phishing attacks can be difficult to catch when security tools are looking for some of the traditional indicators of attacks.

Linkless legitimacy
Callback phishing attacks don't have a traditional malicious URL or payload, requiring specialized scanning to detect.

Embedded callbacks
To further evade security tools, adversaries will often put the callback information in embedded images, so as not to be picked up by body text analysis.

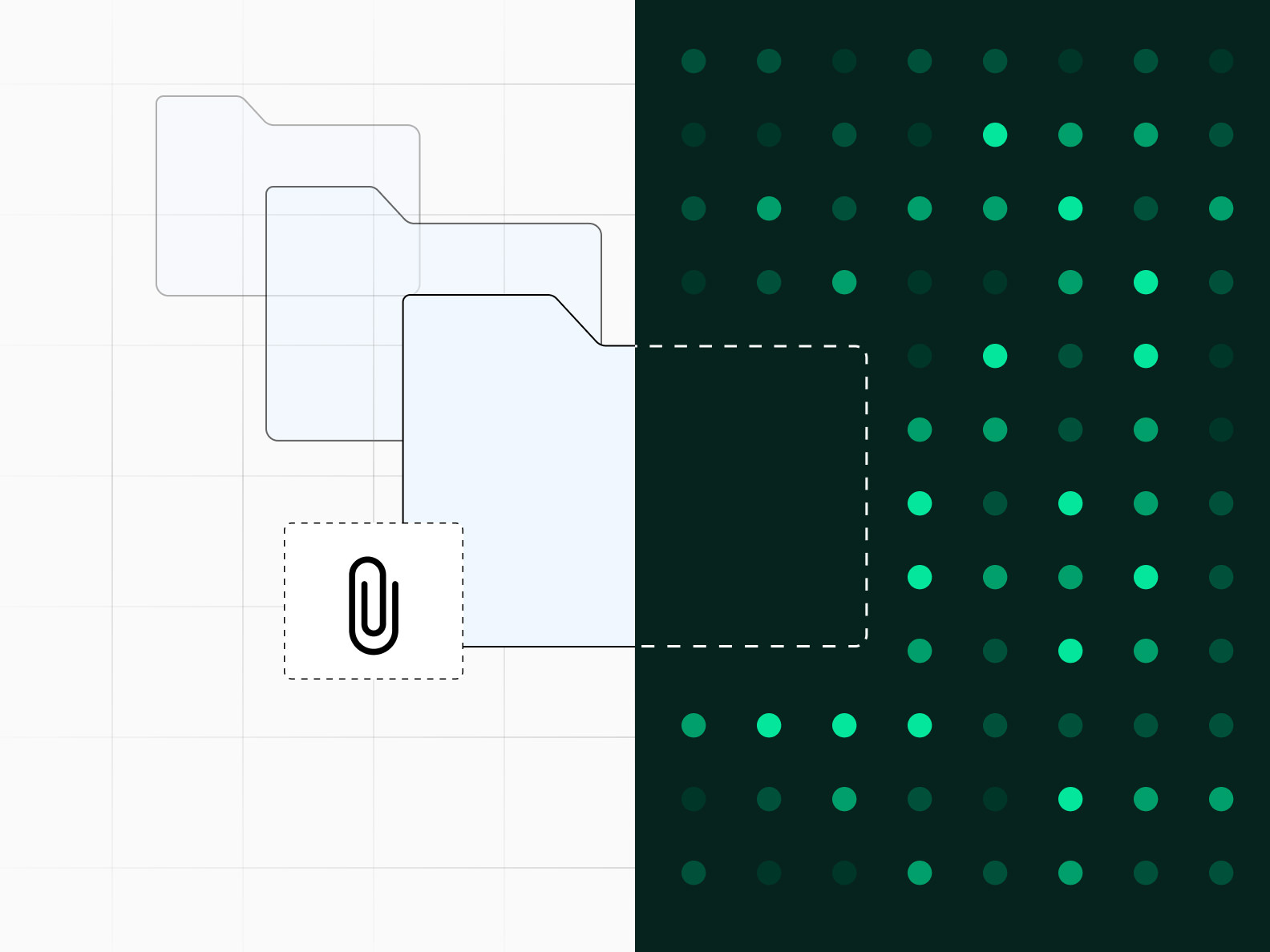
Attacks in attachments
Attackers will put callback information within attachments, sometimes nested within archives, to make it easy for humans to find but difficult to detect.
Tools for catching callback phishing
Callback phishing can be difficult for most security platforms, but Sublime uses a layered combination of AI, machine learning, and org-specific detections to catch the phish.
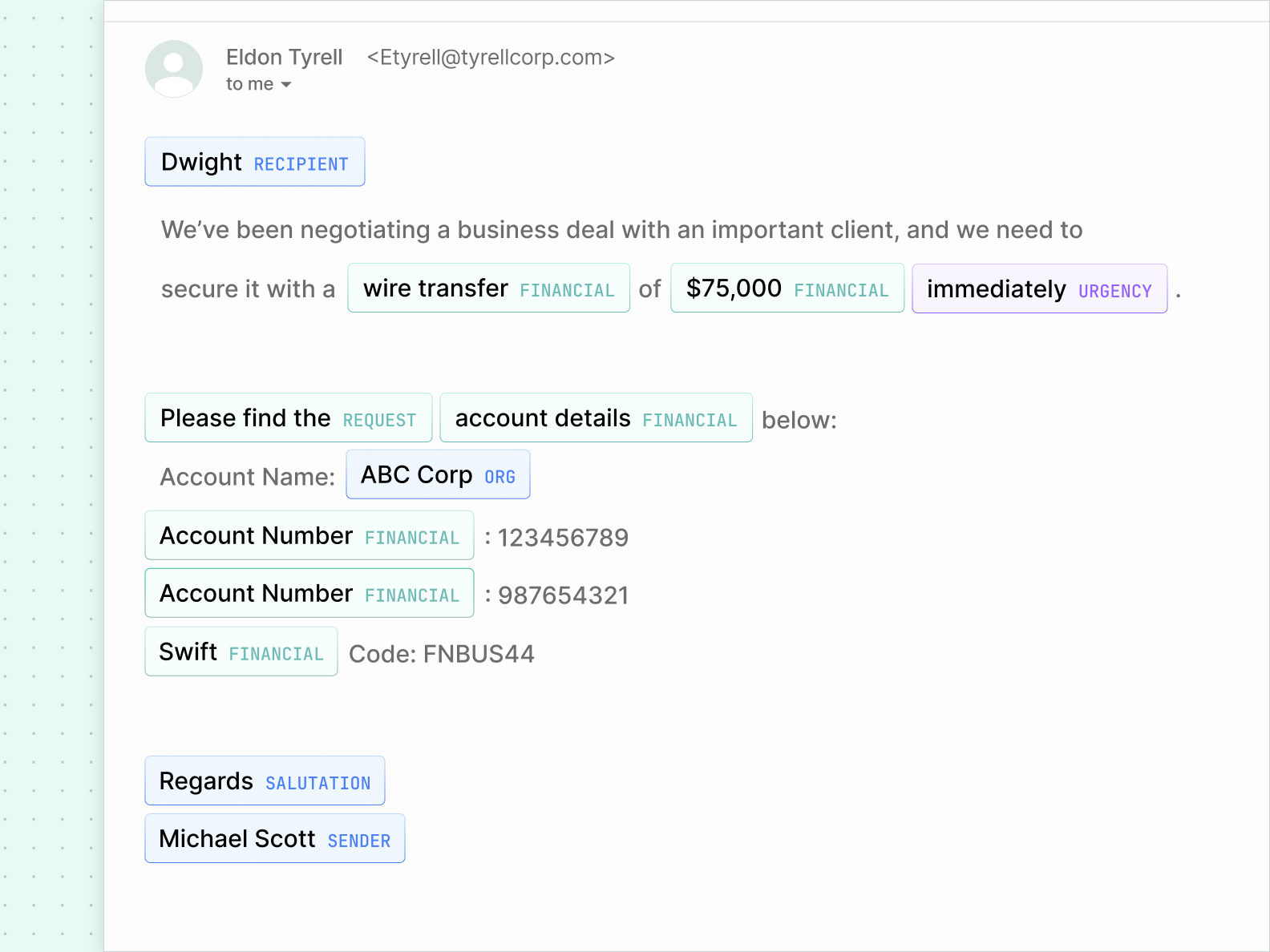
Sublime uses Natural Language Understanding (NLU) to understand the intent of a message. By comparing the intent with the data and metadata of an email, callback phish quickly come into focus.
Sublime takes a screenshot of messages and attachments and looks for brand logos, QR codes, and runs it through Optical Character Recognition (OCR). These analyses let us catch brand impersonations and text embedded as images to avoid body scanning – common evasions for attackers.

Sublime analyzes attachments and images with OCR and intent analysis the same way it analyzes the email body. This includes recursive analysis of archives, scanning all files within regardless of depth.
Advanced callback phishing detection for your organization
See how Sublime's comprehensive callback phishing platform can safeguard your business from callback phishing attacks.
Latest on callback phishing
The latest news, research, and attack spotlights about callback phishing.
Frequently asked questions
What is callback phishing?
Callback phishing is an email scam that pushes the victim to call a “support,” “billing,” or “fraud” phone number. These attacks often use fake invoices, renewal notices, receipts, or account alerts to create urgency. Attackers use callback phishing because the social engineering happens over the phone, outside most email security controls. Many campaigns use brand impersonation and invoice-themed PDFs centered around a callback number.
Why is callback phishing difficult for traditional email security tools to detect?
Many traditional tools are optimized to score URLs, detonate attachments, and block known-bad infrastructure. Callback phishing often contains no malicious link and no malware attachment to analyze. The ‘payload’ is a phone conversation. These emails also frequently arrive through legitimate services or compromised accounts, allowing SPF, DKIM, and DMARC checks to pass even when the content is fraudulent. Attackers also reuse realistic invoice templates and light obfuscation techniques that can evade brittle keyword filters.
How does Sublime Security detect callback phishing attacks?
Sublime Security detects callback phishing attacks by analyzing email content, sender behavior, embedded phone numbers, and infrastructure patterns associated with TOAD campaigns. Using behavioral analysis and customizable detection rules, Sublime identifies both known and emerging callback phishing attacks that often evade traditional secure email gateways.
What are common signs of a callback phishing email?
Common signs of callback phishing include urgent requests to call a support or billing number, unexpected invoices or renewal notices, and impersonation themes involving brands like Microsoft, PayPal, Zoom, or Geek Squad. Many campaigns also use suspicious sender details, invoice PDFs, repeated phone numbers, or light obfuscation techniques designed to bypass filters.
Can callback phishing emails come from legitimate services?
Yes. Attackers often abuse legitimate services and compromised accounts to make callback phishing emails appear more trustworthy. Many campaigns use realistic invoice or receipt PDFs designed to push recipients into calling a fraudulent support number. Even when email authentication passes, it only validates the sending infrastructure, not the legitimacy of the message content or brand claims.
What happens if someone calls a callback phishing number?
Once the victim calls, the attack shifts to real-time social engineering. Attackers may try to steal money, capture account credentials or MFA codes, or convince the victim to install remote access software. The primary risk is that the interaction moves into a live phone conversation where technical defenses have limited visibility and social engineering pressure escalates quickly.
How can organizations prevent callback phishing attacks?
Organizations can reduce callback phishing risk through layered detection, user education, and response workflows. Security teams should detect and quarantine suspicious invoice-themed emails, including malicious PDFs and embedded callback numbers. Users should avoid calling phone numbers listed in unexpected invoices or fraud alerts and instead navigate directly to trusted vendor websites or support channels. Organizations should also encourage rapid user reporting and treat urgent “call now” requests tied to payments or impersonation themes as high risk.
Now is the time
See how Sublime delivers autonomous protection by default, with control on demand.
.avif)





