Prevent email-delivered malware & ransomware
Malware and ransomware attacks can cause significant data loss and business impact. Sublime's AI-powered, adaptive email security detects and prevents these attacks before the payload can be delivered.

Malware/ransomware in a nutshell
Malware attacks quietly install malicious software that can steal data, encrypt files, or open the door for more serious threats.
Ransomware attacks install software that locks systems or data until a ransom is paid to unlock them.
Some attackers also steal data and threaten to leak it if the ransom isn't paid, a tactic known as double extortion. The impact can be severe, including downtime, lost data, financial loss, and reputational damage.
Our previous solution delivered a well-crafted phishing email to our technology team, but Sublime identified it as malicious immediately. That was our first 'oh yeah, Sublime is way better' moment.
What makes malware/ransomware attacks so effective
Malware and ransomware attacks are delivered in a variety of ways, with novel techniques constantly being developed.

Wide-ranging delivery
Attacks can be delivered via links with automatic downloads, hidden within another installation process, command copy/paste, and more.

Silent installation
Malware and ransomware installations often run silently in the background, so a target doesn't know it's installed until it's too late.

Masked in legitimacy
Increasingly, attackers will use legitimate IT tools (ScreenConnect, AutoIT, etc.) for malicious purposes, bypassing traditional security.
Tools for keeping malware/ransomware out of inboxes
Malware and ransomware can shut a business down. Sublime uses a layered combination of AI, machine learning, and org-specific detections to catch these attacks.
Sublime's uses a browser emulation sandbox and machine learning to follow links through redirects and download files for analysis, including payloads delivered via HTML smuggling.
Sublime analyzes files for suspicious indicators. This includes recursive analysis of archives, scanning all the files within regardless of depth.
Attacks can be delivered through a wide variety of file types (PDF, HTML, EML, DOCX, XLSX, ZIP, RAR, ICS, and more), so Sublime analyzes every file looking for malicious indicators.

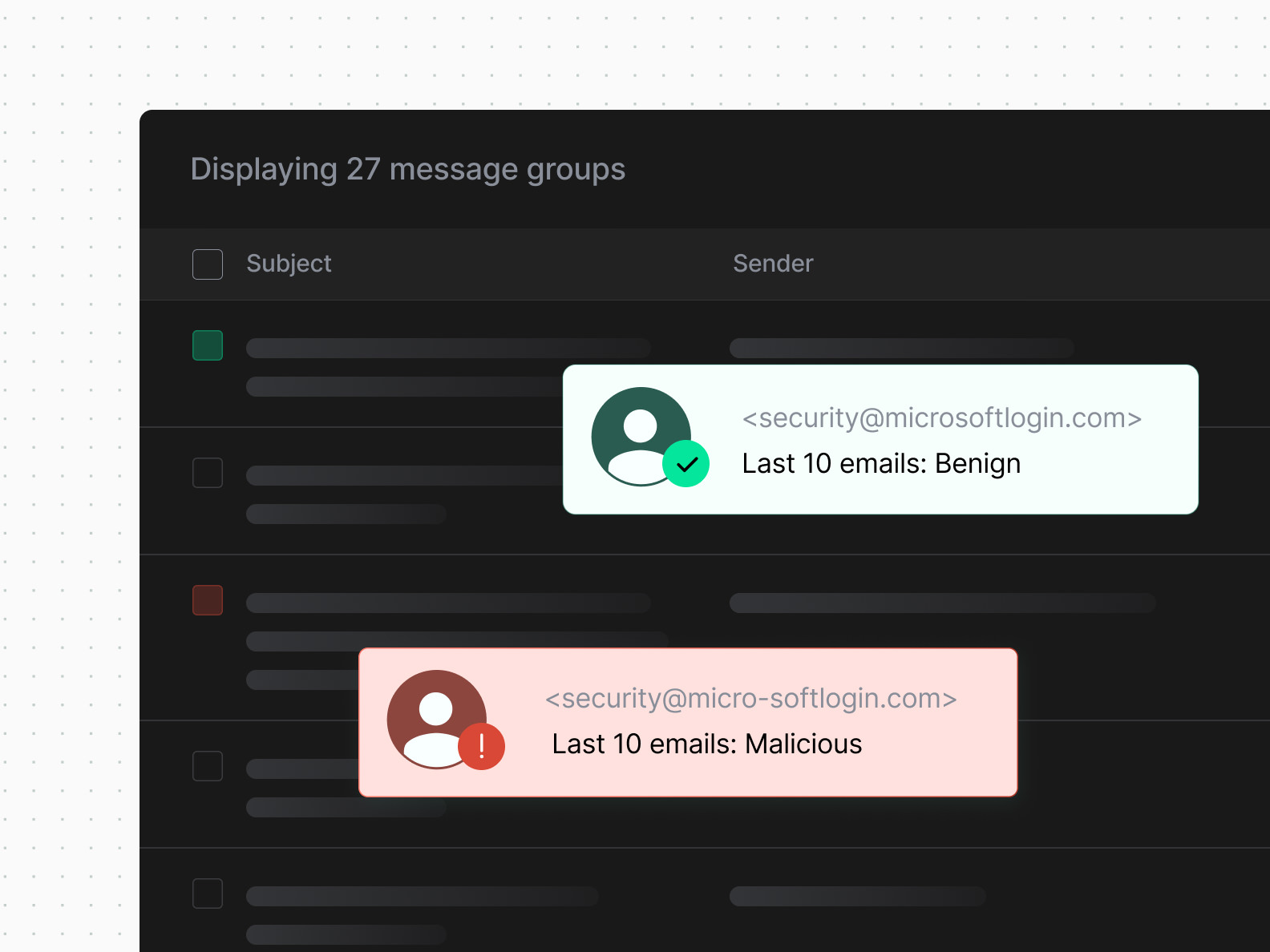
Sublime uses sender behavioral history, organization context, WHOIS registration data, and more to determine the trustworthiness of a sender.
Advanced ransomware and malware email protection
See how Sublime's comprehensive ransomware email protection can safeguard your business from malware and ransomware attacks.
Latest on malware/ransomware attacks
The latest news, research, and attack spotlights about malware/ransomware attacks.
Now is the time
See how Sublime delivers autonomous protection by default, with control on demand.
.avif)





