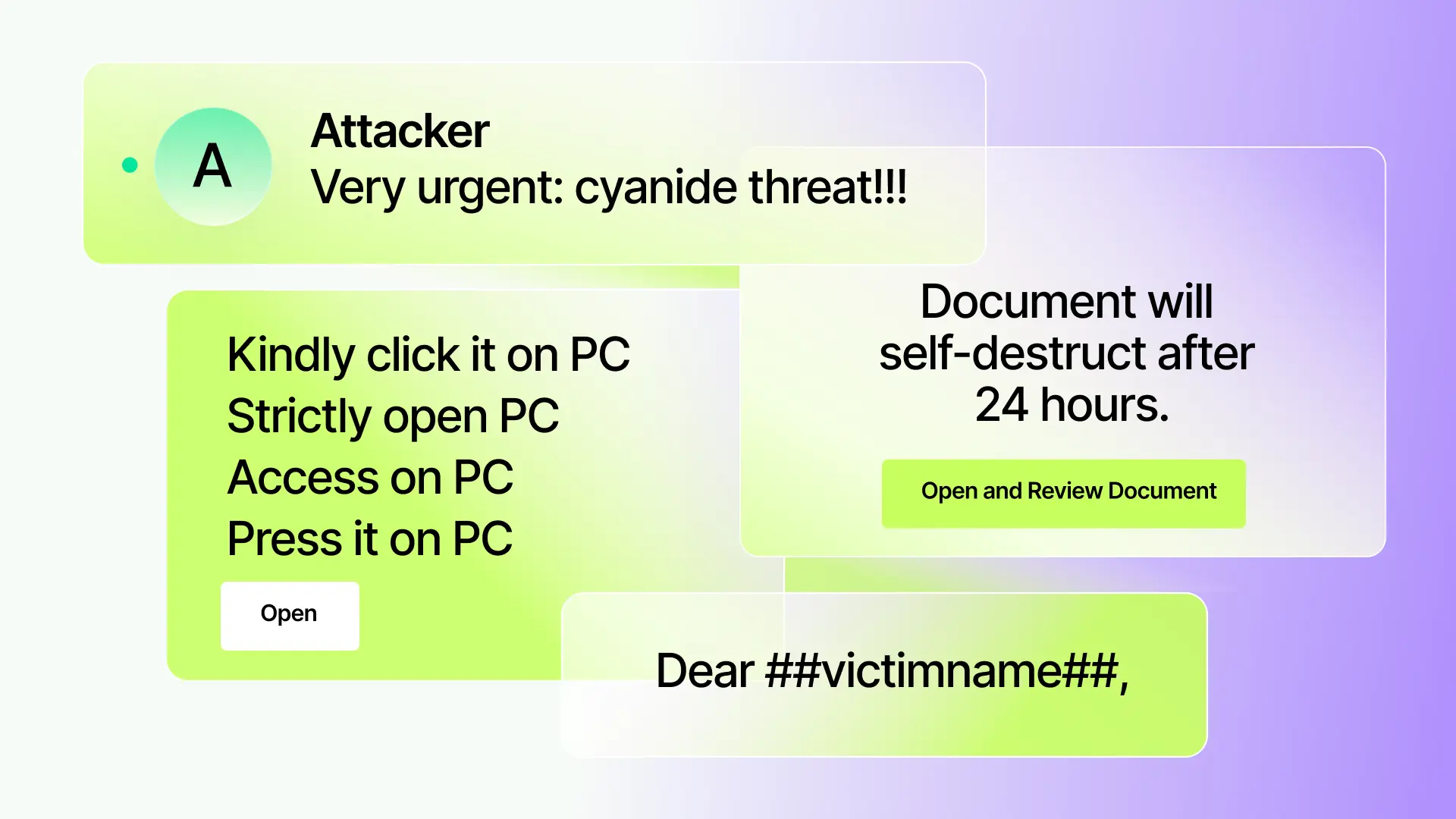
Modern email attacks are highly sophisticated, often featuring carefully crafted language with no obvious malicious markers. Attacks like business email compromise (BEC) often feature incremental phases that build context and trust, and lack the patterns that would make a purely signature-based or rule-based defense sufficient.
Effective detection hinges on understanding email content like a human would. At Sublime, we’ve long used Natural Language Understanding (NLU) as part of our Message Query Language (MQL) to analyze email tone, intent, and context to detect subtle malicious cues that traditional filters often miss. This NLU-driven approach helps us flag nuanced attacks that lack typical indicators like suspicious links or attachments.
Making the use of NLU all the more important is GenAI. Attackers can use LLMs to produce countless textual variations of every attack, continuously rephrasing messages to try and get one or two to slip through defenses, all at minimal cost. For all these reasons, we’re excited to announce our release of NLU 3.0, a major model upgrade built for speed and accuracy in the face of rapidly evolving attacks and edge cases.
This upgrade has already been deployed and is automatically available to all users – no manual updates necessary.
Benefits of NLU 3.0
We’ll release a technical deep dive in the next few days, but the biggest updates in NLU 3.0 are:
- Synthetic data augmentation with GenAI: Our in-house training models create realistic variations of novel attacks. Our models even use anonymized attack data to create brand new attacks, beating bad actors to the punch.
- Unified multi-head architecture: NLU 3.0 uses different “heads” to handle different tasks (intent classification, topic modeling, etc.). These heads then return their results to BERT, creating shared context across processes for better decision making.
- Modular heads for rapid expansion: We can easily add new heads to NLU 3.0 without retraining the whole model, meaning we can add features and functionality more rapidly than ever to proactively catch new attack patterns.
The immediate benefits of these updates are clear for all users – more threats caught, fewer false positives, and richer insights driving both automated detection and human analysis. Importantly, these gains come without sacrificing performance, thanks to careful engineering and the inherent efficiency of a unified model approach.
NLU 3.0 empowers security teams to defend their organizations more effectively. Our NLU shines a light on who an email is talking about, what it’s asking, and why it might be dangerous, all in understandable terms. This transparency and depth make it easier to trust and act on the system’s findings. Let’s look at what these updates mean for day-to-day email security operations.
Enhanced detection and coverage with NLU 3.0
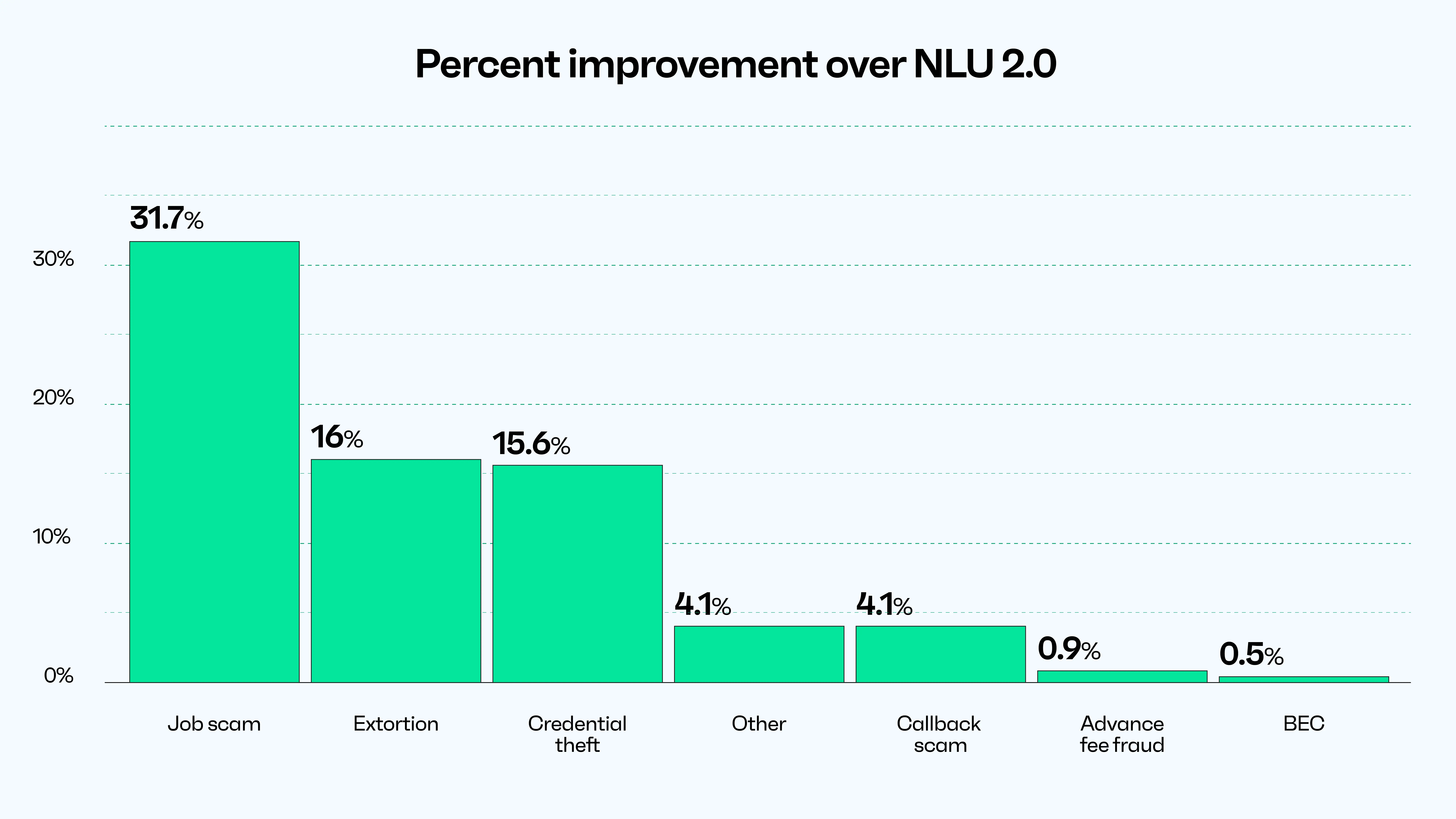
By enriching NLU 3.0 with diverse, realistic synthetic training data, we immediately boosted our catch rate on tricky attacks. In internal A/B tests, we saw significant reductions in missed threats – including polymorphic phishing emails that varied greatly in wording. The upgraded NLU model is adept at recognizing the malicious intent behind differently phrased emails – often AI-generated – that previously might evade detection.
The improved context understanding also helps reduce false verdicts. The model can discern normal business communications from truly fishy ones more accurately. For instance, distinguishing a legitimate vendor invoice inquiry from a fraud attempt by considering nuances like the sender’s role, writing style, and content specifics. This means security teams can trust the alerts they get, focusing on real incidents instead of chasing down false positives.
All these NLU insights (intents, entities, topics, etc.) are exposed as functions in MQL, meaning detection engineers can readily incorporate them into rules. The upgraded NLU model therefore not only provides better signals, it also simplifies rule creation. This simplified architecture has also allowed us to simplify what writing MQL with NLU capabilities looks like. Below is a sample MQL snippet that uses NLU to detect credential theft language within an EML attachment, a known evasion technique:
Looking toward the future of NLU
The upgrade to Sublime’s NLU engine marks a significant milestone in our mission to outpace email adversaries. By combining GenAI-augmented training data and a multi-head multi-task architecture, we’ve dramatically improved our system’s language intelligence and made Sublime more resilient to GenAI attacks and variants.
This NLU framework is a living platform for innovation. With NLU 3.0, the days of morphing keywords to evade filters are over. As attackers change tactics or entirely new threat types emerge, our NLU can adapt rapidly. Whether it’s adding a new head for a detection capability nobody has thought of yet, or fine-tuning on a new wave of social engineering lures, we’re poised to respond faster than ever.
We’re excited about the road ahead. In upcoming releases, expect to see even more NLU-driven features roll out. We will also share our insights and successes – for example, how these NLU improvements feed into our new Attack Score or how they enable our Autonomous Security Analyst (ASA) to make smarter decisions. Stay tuned for those deep-dives or get a live demo of Sublime to see NLU 3.0 in action.
Get the latest
Sublime releases, detections, blogs, events, and more directly to your inbox.


.avif)
