Introduction
Business Email Compromise (BEC) attacks are a prevalent and insidious form of cybercrime that targets organizations of all sizes and industries. These attacks often involve carefully crafted email messages designed to impersonate trusted individuals or entities, such as C-suite executives, HR personnel, or vendor/supplier accounting departments.
Cybercriminals can inflict considerable financial and reputational harm on targeted organizations by tricking unsuspecting employees into carrying out unauthorized transactions or revealing confidential information.

BEC attacks are highly sophisticated. Unlike other email attacks, they often contain carefully crafted text without obvious red flags. Attackers often conduct extensive research on their targets and tailor their approach to appear legitimate.
This level of customization, combined with the absence of typical payloads such as malicious attachments or links, makes it increasingly difficult for traditional security measures to detect BEC.
Attack Story
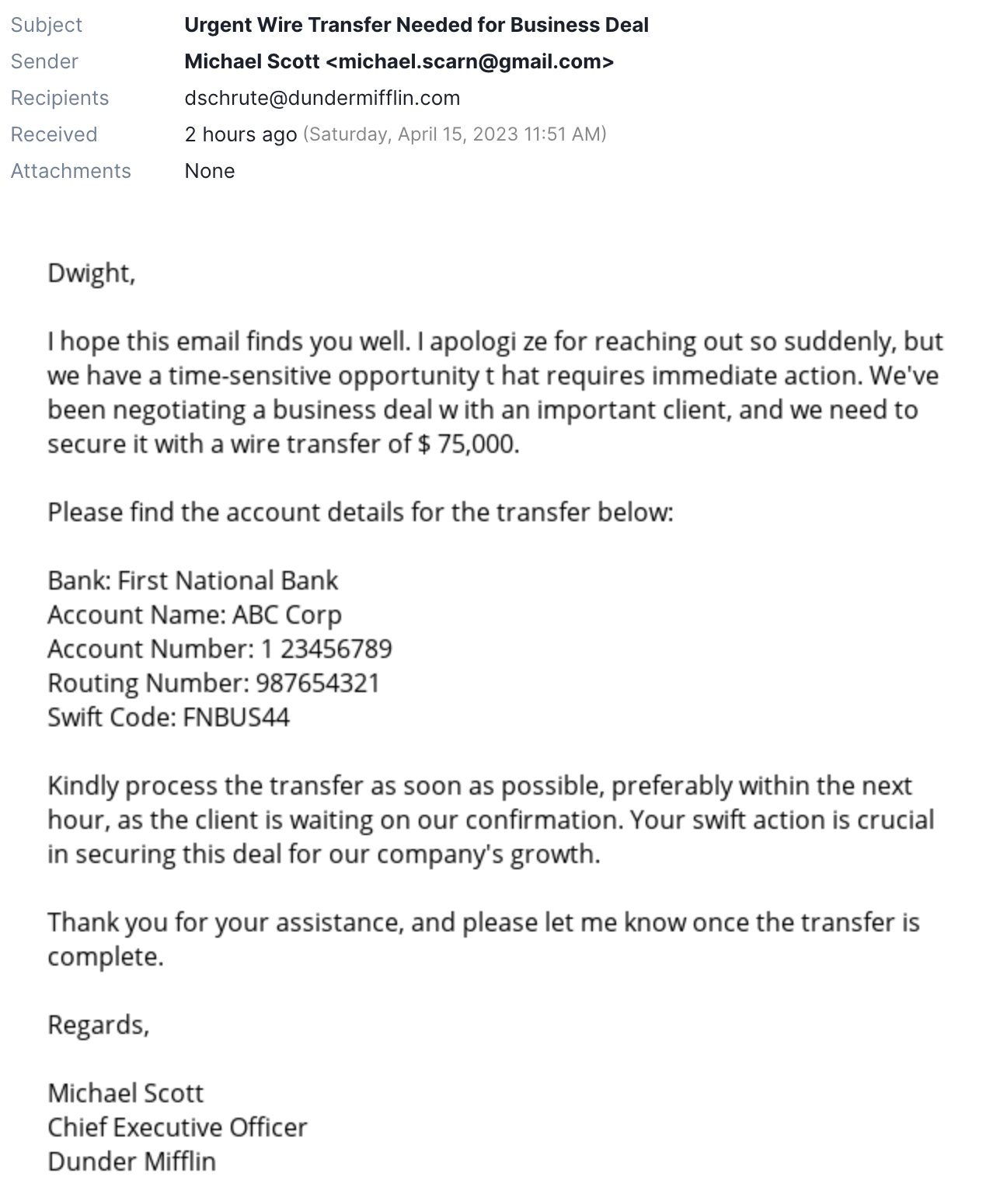
Imagine an employee, Dwight, working in the sales department of a medium-sized company. He receives an email that appears to be from the company's CEO, Michael Scott, requesting an urgent wire transfer to secure a time-sensitive business deal. The email contains the CEO's typical language and signature and even references a recent company event. Trusting the seemingly genuine request, Dwight proceeds with the transfer, discovering later that the email was a cleverly disguised BEC attack. The attackers tricked Dwight, stole the company's money, and caused financial and reputation harm to the organization.
Given the BEC attack story described above, one might wonder how organizations can detect and prevent such skillfully crafted and deceptive emails. Preventing BEC attacks like the one above can be challenging for organizations. Attackers have become increasingly sophisticated, often blending social engineering tactics with techniques to bypass traditional security measures.
The Limitations of Traditional Security Measures in Identifying Targeted BEC Attacks
Traditional email security measures often rely on analyzing links and attachments and often struggle to identify and prevent targeted BEC attacks. These sophisticated threats can slip past conventional defenses due to their tailored nature and the attackers' deep understanding of their targets. In such cases, organizations need a more dynamic and intelligent approach to safeguard their digital assets and reputation.
Natural Language Understanding (NLU) for Enhanced Email Security
Natural Language Understanding (NLU) is an advanced AI-driven technology that offers organizations a powerful tool to combat BEC threats. NLU can help differentiate between genuine and potentially malicious content by analyzing and interpreting the language used in the body and attachments of email communications. The ability to discern deceptive language patterns empowers organizations to take swift action against BEC attacks and protect their sensitive information.
In the following sections of this blog post, we will explore how our NLU engine aids defenders in detecting BEC attacks through two critical tasks: Intent Classification and Named Entity Recognition.
Combining the NLU engine with the powerful Message Query Language (MQL) provides comprehensive insights into email content, explainability, and adaptability. This integrated approach empowers organizations to respond swiftly and effectively, bolstering their digital environment's security against sophisticated threats like BEC attacks.
ELI5: Natural Language Understanding
Imagine having a conversation with a friend. You understand their words effortlessly, pick up on the context, and respond accordingly. Natural Language Understanding (NLU) is a subfield of artificial intelligence that aims to teach computers to do the same thing – understand and interpret human language. By processing text or speech, NLU algorithms can grasp the meaning and context of the words, enabling them to respond or take action based on the information provided.
Intent Classification Explained
Think of a time when you asked a question, and someone knew exactly what you were looking for without requiring further explanation. Intent classification is similar – it's the process of identifying the primary purpose or goal behind a piece of text. In the context of email security, intent classification helps determine the underlying objective of an email, such as whether it's a genuine request for information or a phishing attempt to steal sensitive data.
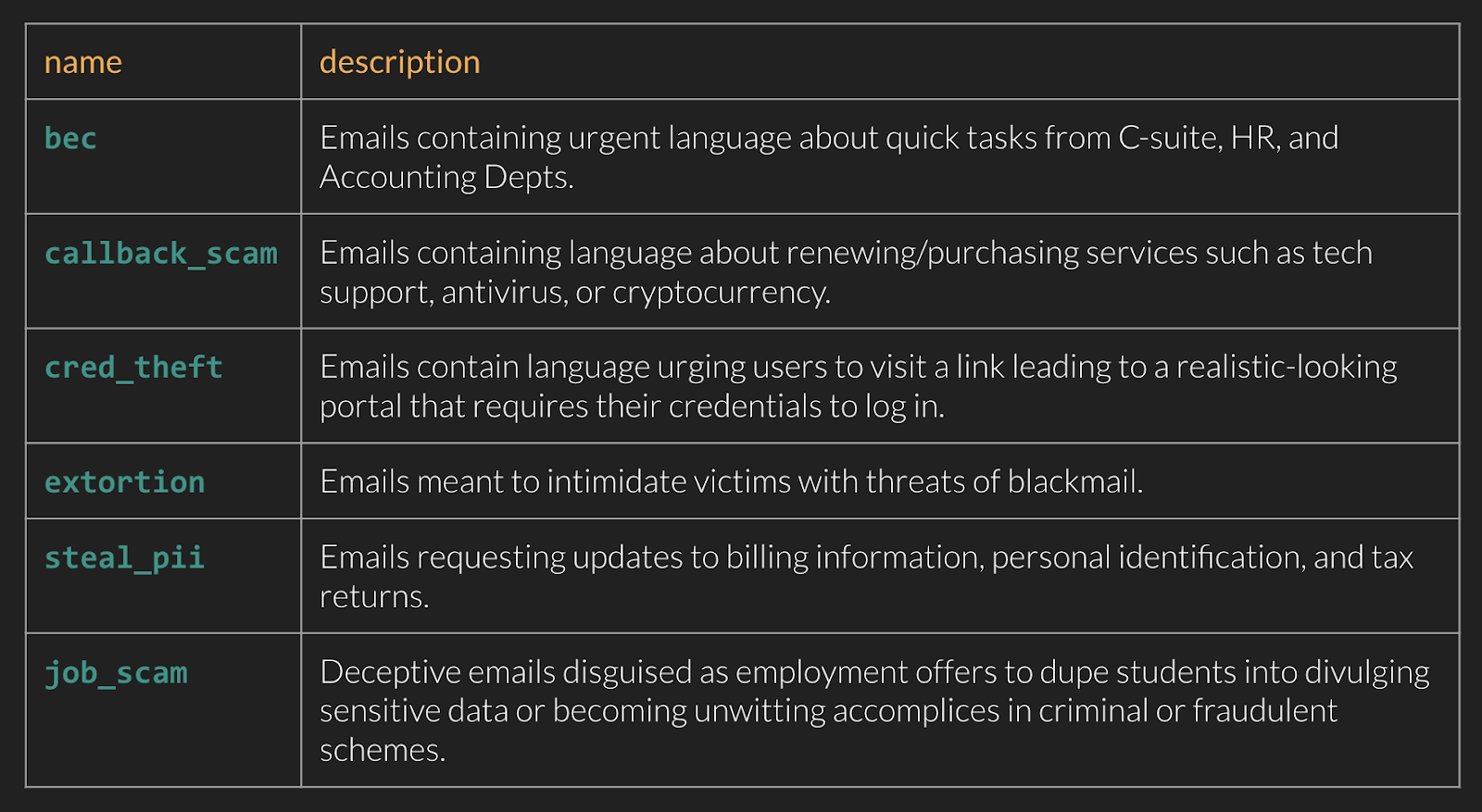
Named Entity Recognition Simplified
When you read a text or listen to someone speak, you naturally recognize important pieces of information like names, dates, or places. Named Entity Recognition (NER) is a technique used in NLU that allows computers to do the same. NER identifies and extracts important keywords or phrases, called "entities," from a body of text. These entities can include people's names, organizations, locations, and more. In email security, NER can help determine if an email contains language commonly associated with urgency, requests, or financial matters, assisting organizations in detecting and preventing potential cyber threats.
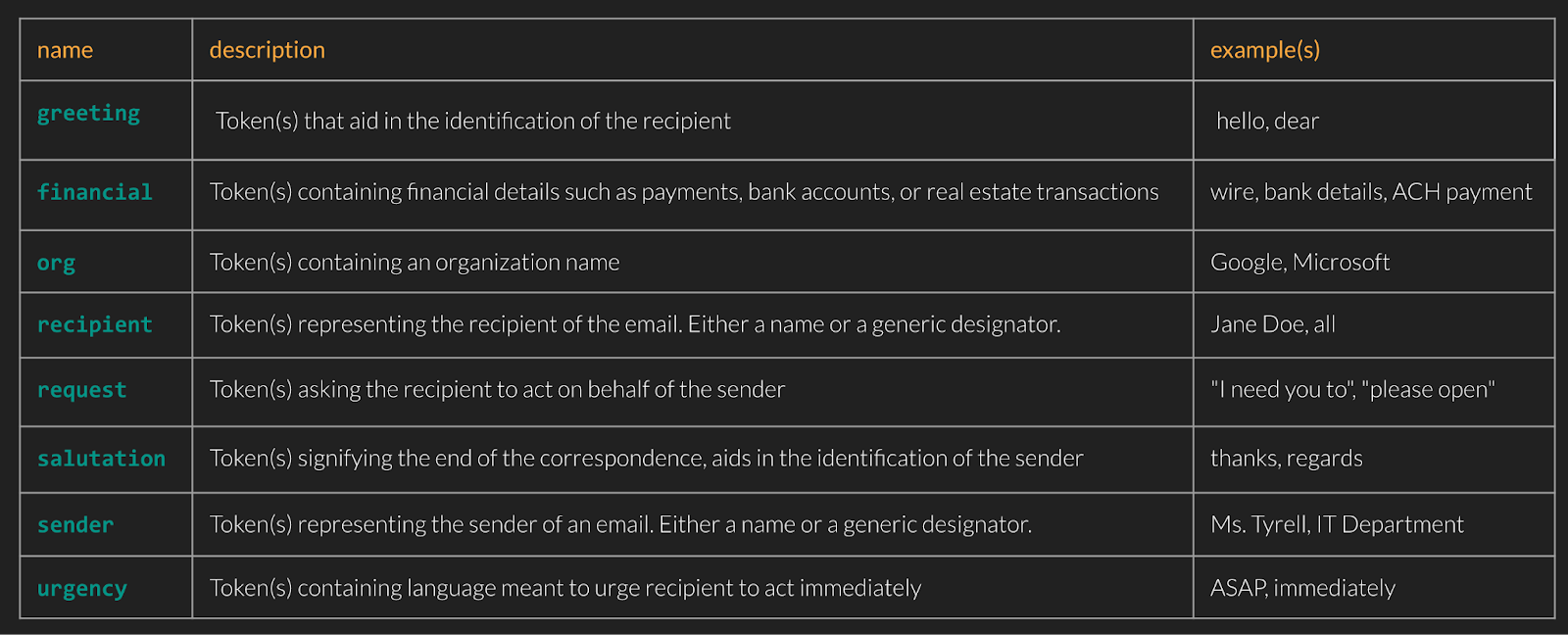
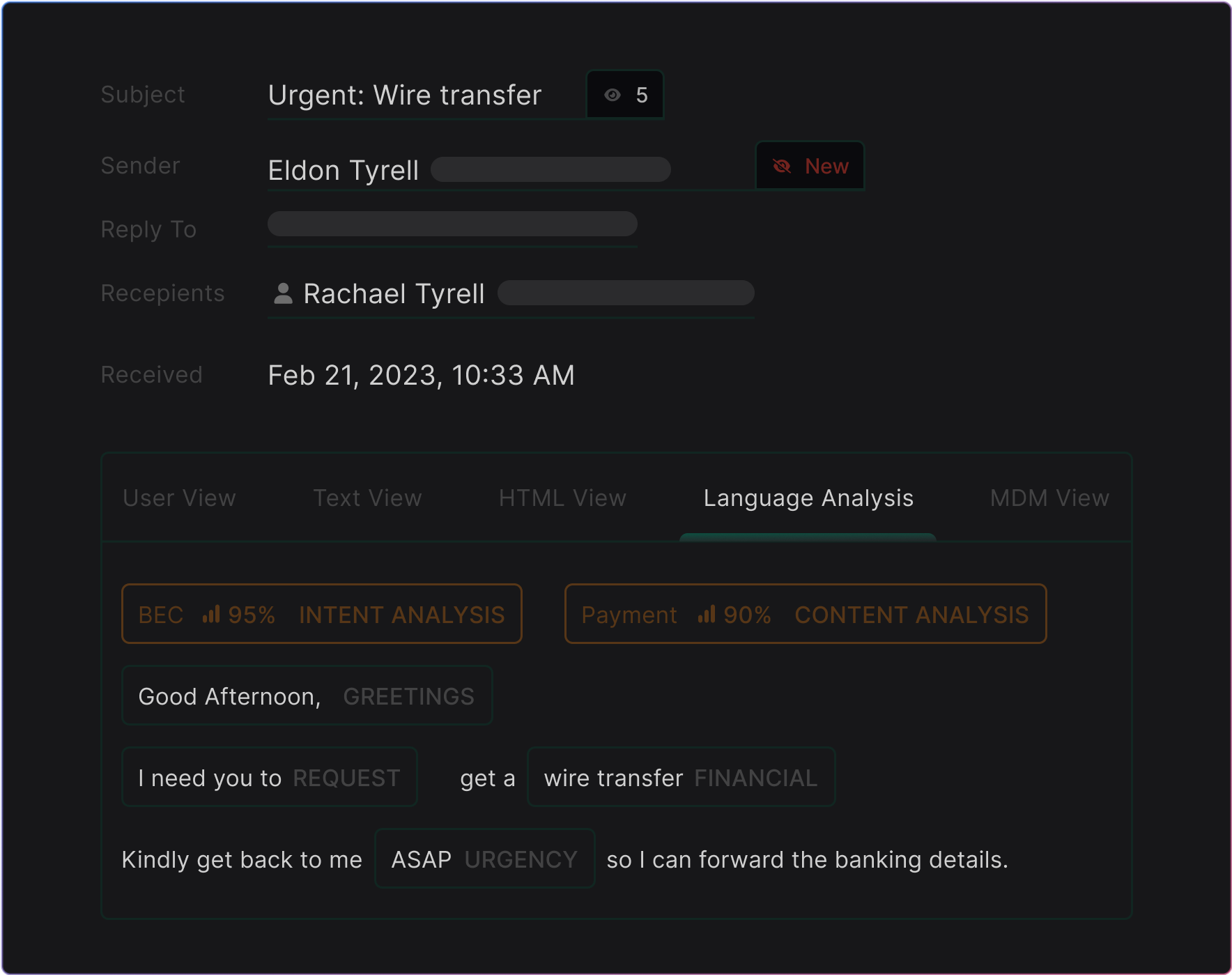
Putting It All Together: Detecting Business Email Compromise in MQL
Now, let's see the NLU engine in action with MQL! To detect a BEC-themed language, we combine NLU's intent classification and entity extraction with other suspicious signals, such as a display name impersonation of a VIP in the organization:
Step-by-step explanation:
any($org_vips, .display_name == sender.display_name)– checks if the sender display name exists in the $org_vips list.any([body.plain.raw, body.html.inner_text], any(ml.nlu_classifier(.).intents,– use the email body as input to the NLU enrichment function and return any intents..name == "bec" and .confidence == "high"– check if any intent has the .name == BEC and .confidence == “high.”any(ml.nlu_classifier(.).entities, .name == "urgency")– check if any entities are present convey urgency.any(ml.nlu_classifier(.).entities, .name == "request")– check if any entities are present that make a request.

In one detection rule for Business Email Compromise, we combine the MQL above with our First-Time Sender logic to effectively defend against many of the the most commonly observed BEC techniques.
Wrapping up
In conclusion, combining Natural Language Understanding (NLU) and signals in Message Query Language (MQL) provides a robust defense against even the most sophisticated Business Email Compromise (BEC) attacks. Although a common downside of NLU approaches is the time required to adapt and iterate, pairing NLU with MQL allows for rapid changes, such as negations, additions, or supporting logic, without updating the model.
By utilizing intent classification to identify email objectives and Named Entity Recognition (NER) to extract crucial keywords, we can deeply analyze and interpret email content, enhancing our ability to detect and prevent deceptive communication.
Integrating these NLU tasks with custom MQL logic creates a highly effective and adaptable email defense, ensuring your organization stays one step ahead of cybercriminals. This comprehensive approach safeguards your digital assets, sensitive information, and reputation from the ever-evolving landscape of cyber threats.
Get the latest
Sublime releases, detections, blogs, events, and more directly to your inbox.



.avif)
