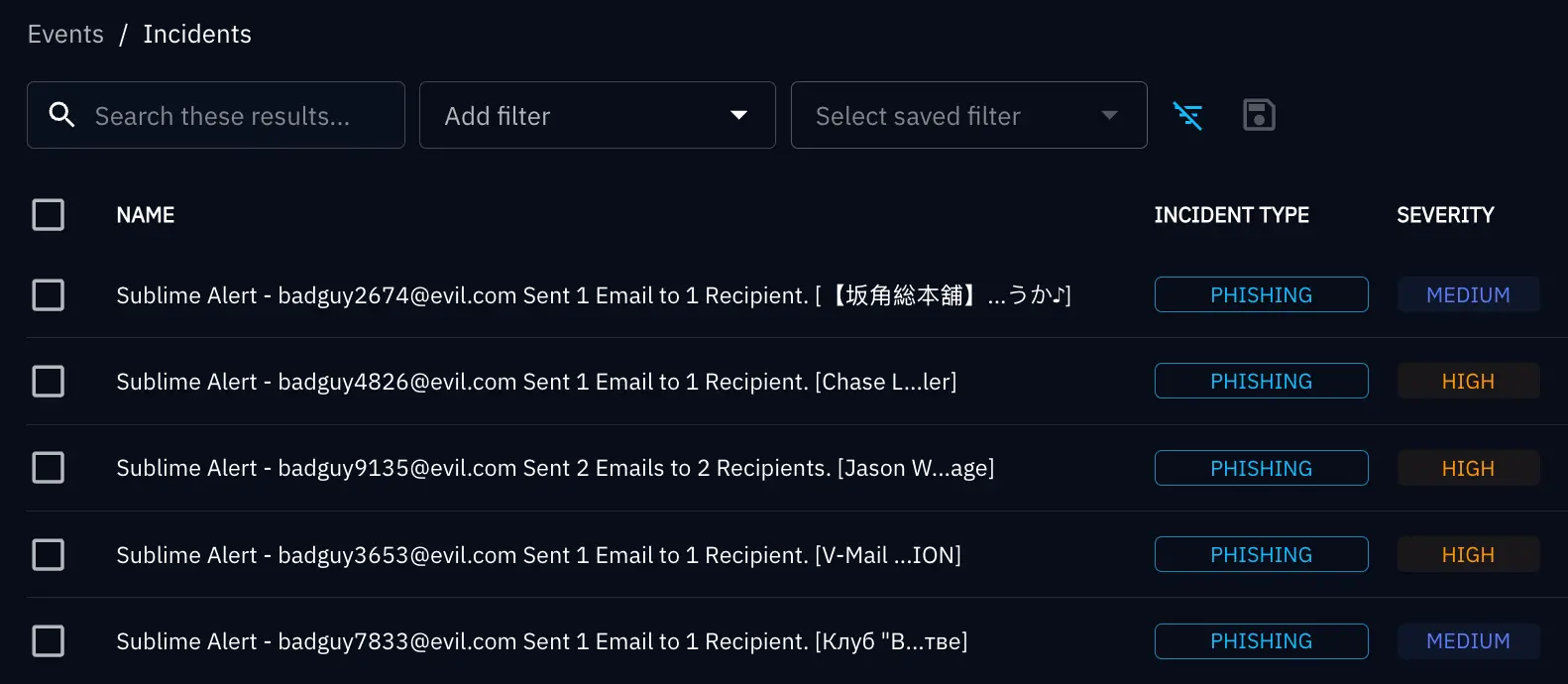
Sublime detects and prevents email threats, and in some cases, those malicious messages can be used to tell a much bigger story. To see the bigger picture, though, security practitioners need to be able to answer questions like: Are those malicious emails part of an ongoing campaign targeting multiple entry points? Are there similarities to attacks disclosed by other companies? Are attachments similar to attacks detected via other delivery methods?
For security teams, the challenge isn’t just detecting malicious messages – it’s understanding how those threats connect to activity across the rest of the environment. With Sublime and OpenCTI working together, security teams gain what matters most: clarity, context, and control over the threats targeting their organization.
This is why we’re excited to announce the Sublime connector for OpenCTI. This new connector feeds your email threat intelligence directly into your centralized, OpenCTI-based platform where it correlates with your existing security telemetry, such as network logs, endpoint data, SIEM alerts, and threat feeds. This reveals the full scope of attacks targeting your organization.
The power of unified intelligence
The Sublime + OpenCTI integration delivers the capabilities security teams need to move from isolated detections to unified intelligence:
- Centralized email intelligence: Sublime detections are automatically ingested into OpenCTI, enriching your threat intelligence platform with high-fidelity email threat data.
- Automated indicator sharing: Indicators of compromise (IOCs) like URLs, domains, IP addresses, email addresses, and attachment hashes are exported in STIX2 format and immediately ingested for correlation.
- Cross-platform correlation: Email-based threats can be analyzed alongside endpoint telemetry, network logs, SIEM alerts, and external threat feeds, enabling deeper investigation and faster response.
- Expanded threat visibility: Security teams gain a unified view of campaigns spanning multiple attack vectors – not just email.
Transforming email signals into actionable intelligence
The integration between Sublime Security and OpenCTI bridges the gap between email threat detection and broader security operations.
Comprehensive threat enrichment: Sublime → OpenCTI
Sublime continuously detects and analyzes malicious email activity, extracting rich indicators and metadata. These detections are automatically ingested into OpenCTI, where they are enriched and correlated with other intelligence sources: open source feeds, commercial intelligence, and internal telemetry.
This creates a complete, contextualized view of threats targeting your organization, without requiring manual data stitching.
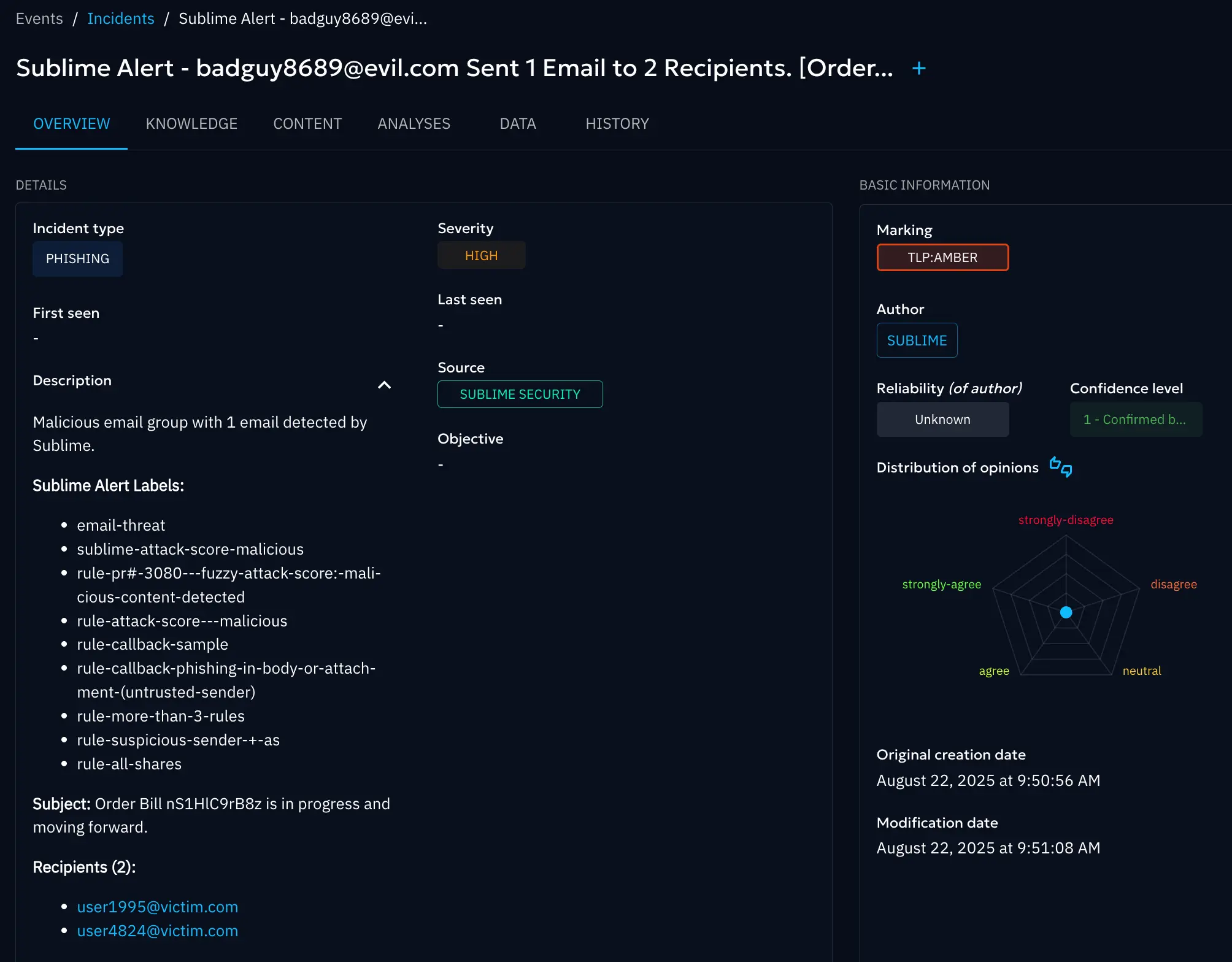
Unified threat investigation: OpenCTI correlation engine
Once ingested, Sublime-derived indicators can be pivoted across your entire security stack. Analysts can quickly answer critical questions:
- Are these emails part of a larger campaign?
- Do these indicators appear in endpoint or network telemetry?
- Are there overlaps with known adversary infrastructure or disclosed attacks?
By connecting email threats to broader attack activity, teams can move from isolated alerts to full campaign understanding.
Operationalizing email intelligence: OpenCTI → security stack
With all threat intelligence centralized in OpenCTI, organizations can operationalize insights across their environment to feed detections into SIEMs, SOAR platforms, EDR tools, and other security controls.
This enables faster detection, stronger response, and reduced manual effort across the SOC.
About OpenCTI
OpenCTI is an open-source threat intelligence platform that centralizes and organizes security intelligence from multiple sources. It's used by thousands of organizations worldwide and supports the STIX2 industry standard for threat intelligence.
Security teams use OpenCTI to:
- Centralize threat data from dozens of sources (threat feeds, security tools, internal detections).
- Hunt for threats across their entire environment using enriched intelligence.
- Track campaigns over time to understand attacker patterns and trends.
- Share intelligence with partner organizations, industry groups, or internal teams.
- Integrate with security tools like SIEMs, SOARs, firewalls, and EDR platforms.
Connect Sublime to OpenCTI
Email threats rarely stop at the inbox. Attackers will use email as the entry point, then move laterally, exfiltrate data, or deploy ransomware across your infrastructure. By connecting Sublime to OpenCTI (or one of the many SOARs we integrate with), you get the ability to easily correlate your email detections with firewall logs, check if a malicious attachment hash appears in your EDR telemetry, and more.
Sublime + OpenCTI gives you the full security picture so attackers have nowhere to hide. Start using the Sublime connector for OpenCTI today, or book a live demo to see it in action.
Get the latest
Sublime releases, detections, blogs, events, and more directly to your inbox.



.avif)
