When evaluating new security solutions, organizations often face a choice between options that have black box AI models that can adapt to new threats, or rule-based systems that offer transparency and control. At Sublime, we believe the best solution lies in the combination of the two.
Attack Score
We’re excited to announce the release of Sublime’s Attack Score, an AI-backed feature designed to analyze potential threats. Sublime’s Attack Score:
- provides a clear and final verdict
- explains and summarizes the attack
- saves manual investigation time
The Sublime Approach
At Sublime, there are many different inputs in our approach to Detection and product development here at Sublime to address the shortcomings of a purely black box approach. Some of which include:
- Message Query Language: A powerful query language, Message Query Language (MQL), allows for precise real-time detection and flexible hunting across email data.
- Artificial intelligence: AI provides key foundational capabilities like Natural Language Understanding and Computer Vision, all transparently exposed through MQL.
- Open-source detections: Community-driven threat intelligence driven by open-source detections enables organizations to benefit from the wider security community's collective knowledge and expertise.
- Community-driven development: Our user community is regularly engaged to gather feedback, insights, and real-world use cases to improve the platform and continuously address evolving security needs.
- Tuneable environments: Every organization has unique email behavior, so users need the ability to customize and fine-tune their threat detection and response workflows to match their specific needs and risk tolerance.
Thoughtful Approach to Machine Learning Integration
So, how can we ensure these core values remain in place when building Attack Score?
- First, we make machine learning adaptable. In the constantly evolving landscape of email threats, it's critical that we can continuously learn and evolve to stay ahead of emerging attacks.
- Second, we make machine learning explainable. We understand that trust is essential when it comes to security solutions.
- Finally, we make machine learning usable. We recognize that a security solution is only effective if it seamlessly integrates into existing workflows and empowers analysts with actionable insights.
Under the Hood: How Attack Score Works
Attack Score leverages machine learning to analyze hundreds of signals extracted from various parts of an email to surface common attack patterns and unusual activity. These signals are derived from:
- Headers
- Attachment metadata
- Link analysis
- Past sender behavior
- Organization-specific context
- Content understanding
- Authentication checks
To provide a comprehensive assessment of each email, Attack Score leverages enrichment capabilities such as:
- Sender behavior profiles
- Natural Language Understanding
- Computer Vision
- WHOIS
- Domain reputation
- Attachment analysis
Privacy-Preserving Feature Engineering
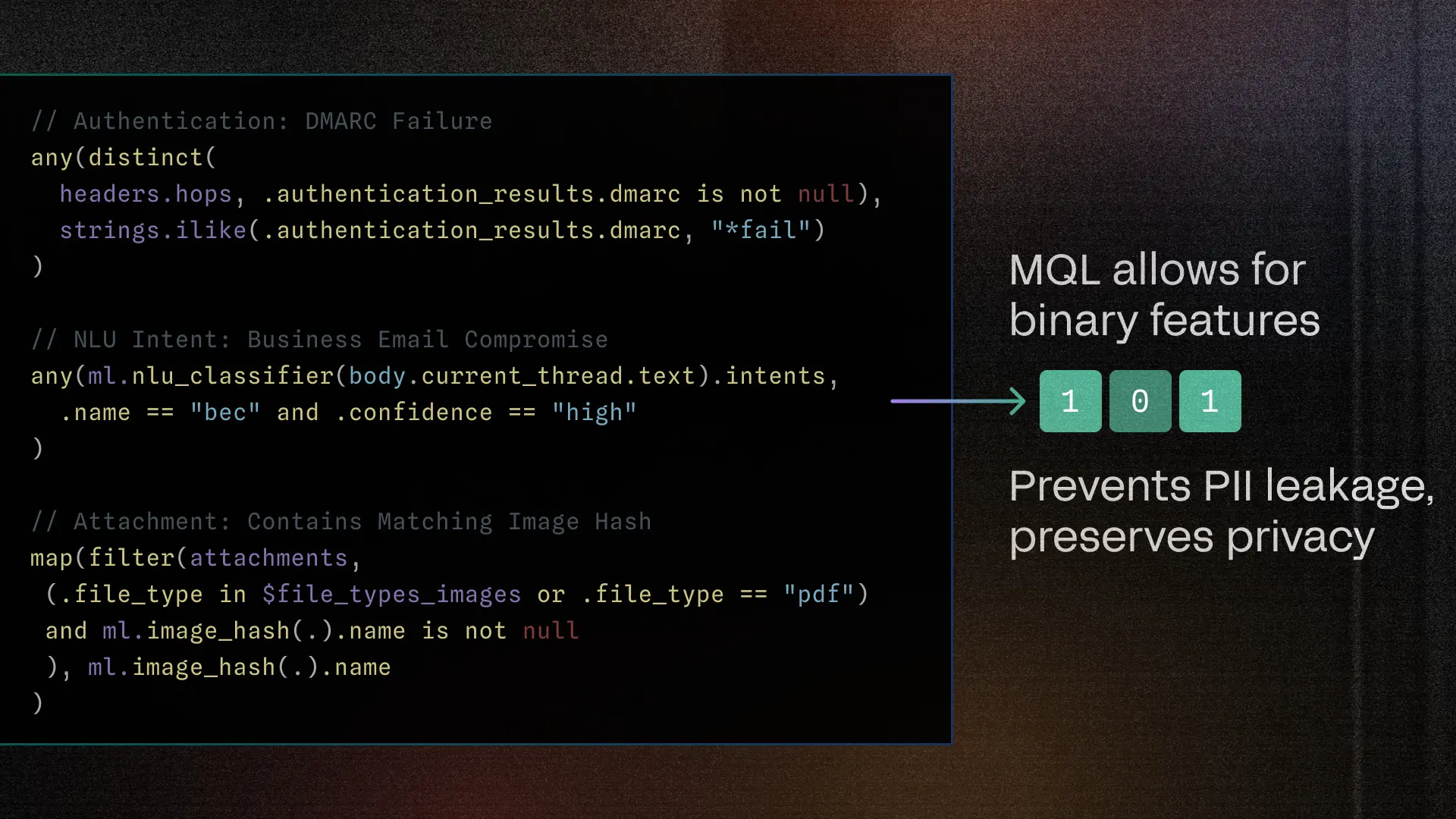
Data privacy is a core tenant in the Sublime platform, so all features used in Attack Score are binary and thus stripped of any personally identifiable information (PII) related to an organization. This approach allows Attack Score to analyze email content effectively without compromising privacy.
Efficient and Explainable Model Architecture
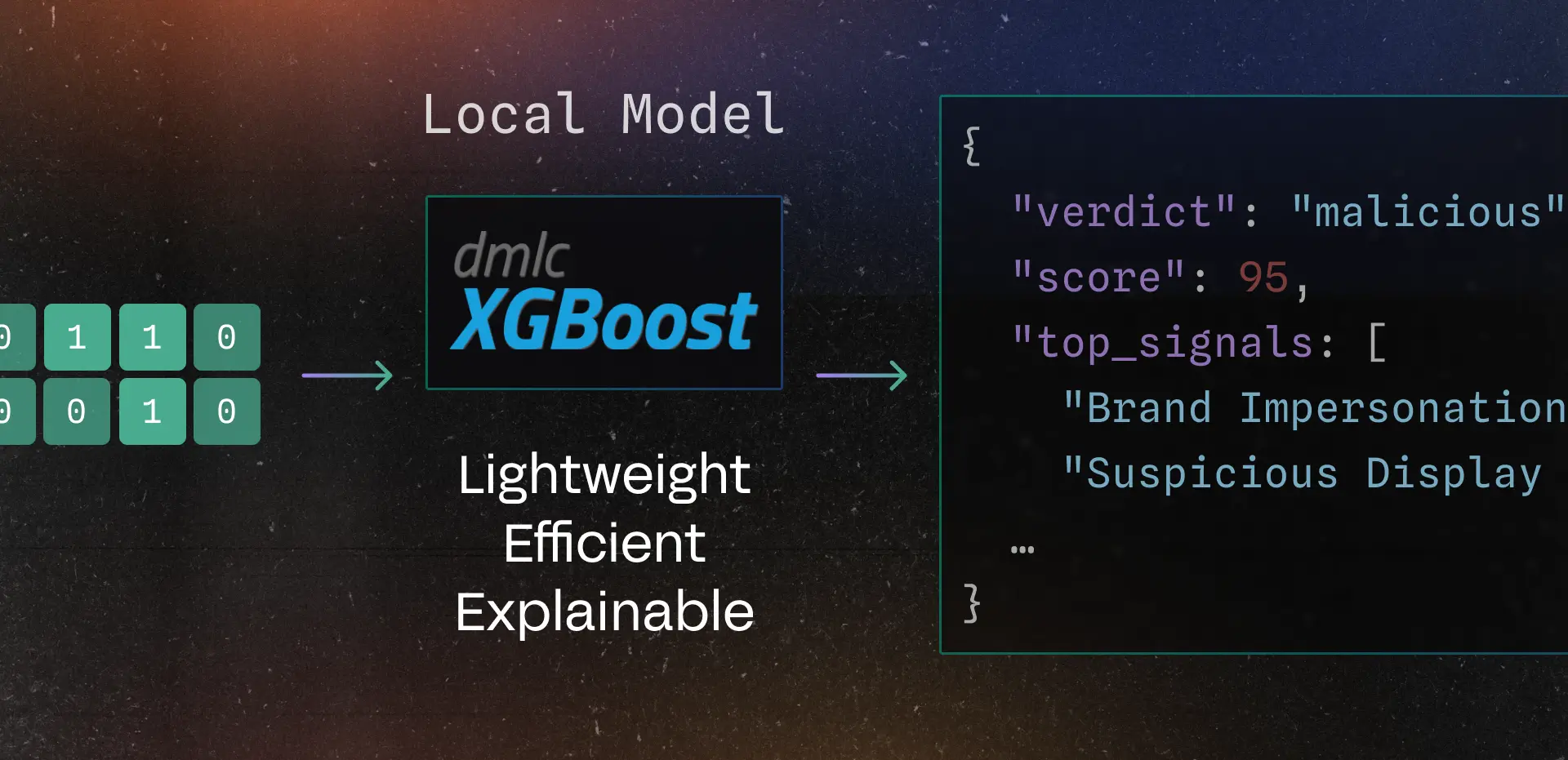
Attack Score employs an XGBoost model for its primary inference engine. XGBoost is a highly efficient, interpretable machine learning algorithm that requires limited computing resources while maintaining a high detection rate. This model architecture allows us to ensure the model inference occurs locally instead of shipping your data to a cloud-based model.
Attack Score traverses the model's decision path, capturing the signals contributing to the verdict. The outcome is a clear, explainable reasoning behind each verdict, with natural language descriptions of each top signal. This transparency and explainability ensures you can trust and understand predictions, instilling confidence in your decision-making process.
Continuous Model Updates
The Attack Score model is continuously updated to incorporate new data shared by customers and newly developed signals. This ensures that Attack Score stays ahead of nascent threats.
Attack Score Output
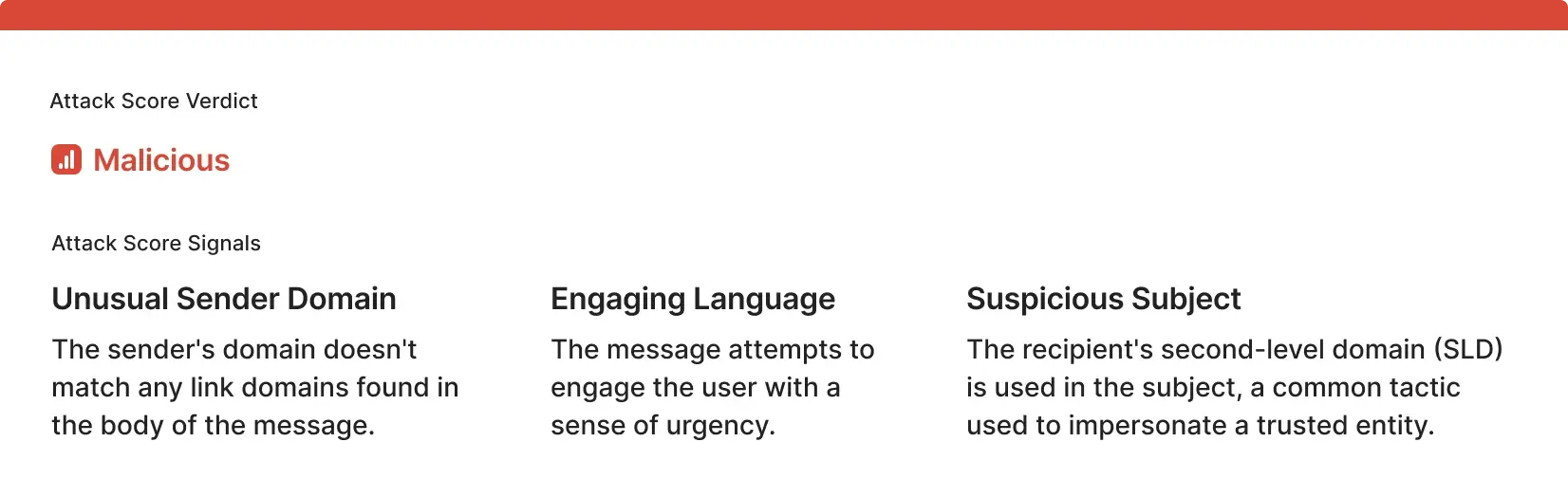
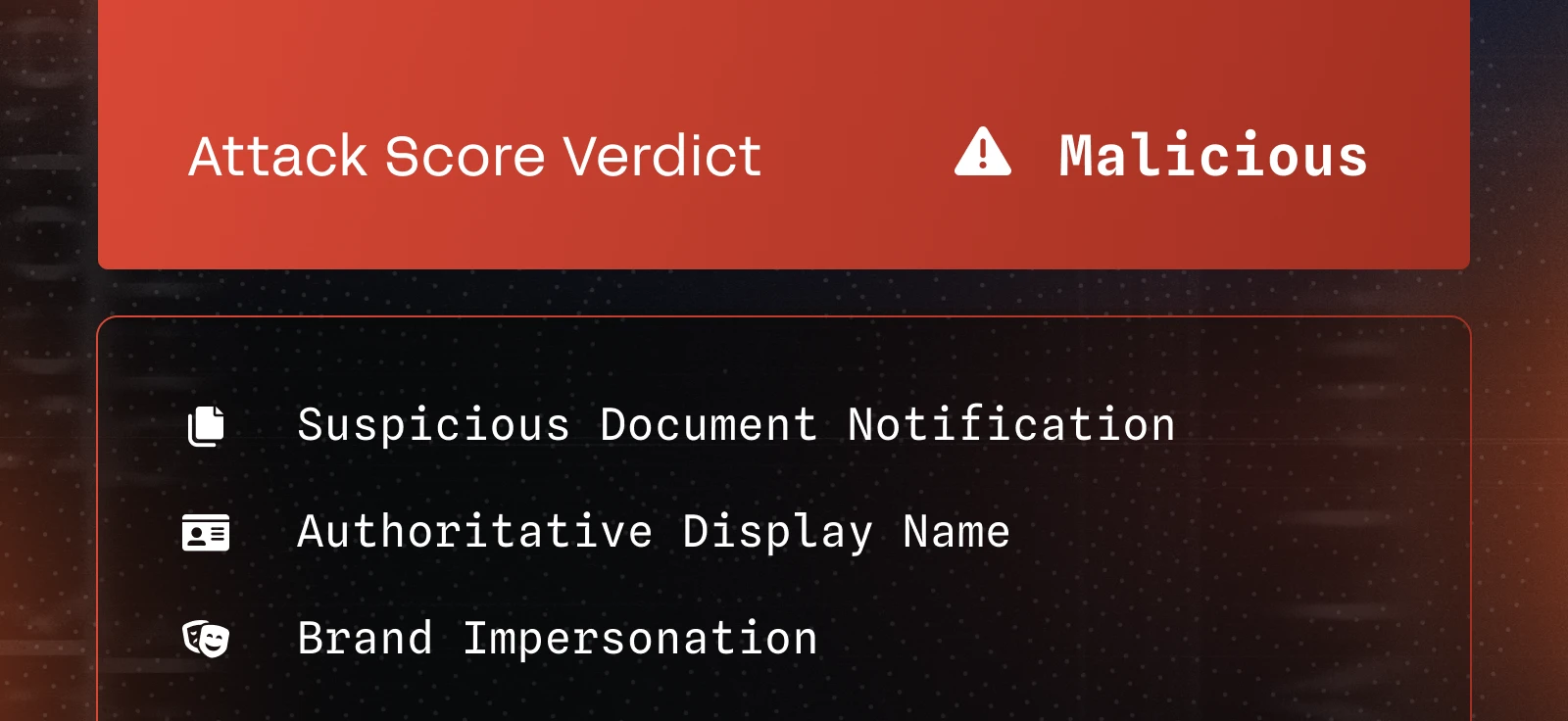
The result of this analysis is a two-part output for each email:
- Verdict: An assessment of the likelihood of a given message being an attack:
Maliciousverdicts signal a threat with high confidence. These messages contain commonly observed attack patterns.Suspiciousverdicts contain patterns indicative of potential threats but are inconclusive.Unknownverdicts are similar to "suspicious" but may also contain common benign behaviors.Likely Benignverdicts contain patterns commonly associated with benign email.
- Top Signals: A summary of the most important characteristics contributing to the verdict, providing context and transparency through explainable ML.
Machine Learning without the Black Box
Machine learning should be introduced to solve security problems only if it can be done in an interpretable and transparent manner. Security teams shouldn’t be left in the dark about how decisions are made by black-box AI – this just creates more work. Attack Score strives to meet this commitment by combining the power of machine learning with the interpretability and transparency that security teams need to make informed decisions quickly.
Get the latest
Sublime releases, detections, blogs, events, and more directly to your inbox.



.avif)
