In our first Sublime Email Threat Research Report, our Machine Learning and Detection teams analyzed anonymized customer telemetry under strict adherence to our internal Data Privacy Framework. The findings highlight significant growth in QR code phishing, OAuth phishing, and the need for a layered, adaptive detection strategy.
Key takeaways
Email threats continue to evolve rapidly, with threat actors demonstrating increased sophistication in both novel attack vectors and evasion techniques. What we found:
- QR code phishing increased 40-60% compared to Q4 2024, accounting for 2.5% of all phishing attempts. Along with this increase in attack volume, the variety of evasion techniques has also increased.
- Living Off Trusted Sites (LOTS) attacks leveraging trusted cloud services now account for ~8% of attacks. These include enterprise services (Microsoft 365, Google Workspace, DocuSign), as well as consumer services (Venmo, PayPal).
- Attacks using malicious SVG files as an attack vector have increased significantly. Our data shows a 47000% increase in SVG, attachment-based attacks in Q1 2025, accounting for 1% of all phishing attempts.
- There’s been a significant increase in BEC/fraud campaigns with evidence of AI-created content. GenAI is helping bad actors create, automate, and refine targeted attack campaigns faster than ever.
Trends
Emerging trends make it clear organizations need a layered, adaptive detection strategy that blends AI, machine learning, behavioral analysis, and threat intelligence complemented with other defense-in-depth controls to effectively counter the full spectrum of email threats.
Threat uniqueness and customization
On average, 90% of malicious emails detected were customized (as defined in the report) to their target in some way, representing a 12% increase from our observations in Q1 2024. This is the clearest signal yet that mass, template-driven phishing is dying. Attackers are leveraging automation, AI, and reconnaissance to craft bespoke attacks that bypass static defenses. The old “block once, protect forever” model is collapsing.
Emerging attack vectors
Breakthrough threats like QR codes, SVGs, and LOTS attacks represent a significant evolution from traditional single-vector attacks, requiring security teams to implement strategies that can detect and respond to complex attack chains.
Continued evolution of BEC and social engineering
BEC and related social engineering attacks continue to represent the highest financial cybercrime risk to most organizations, with clear industry-specific targeting and patterns emerging.
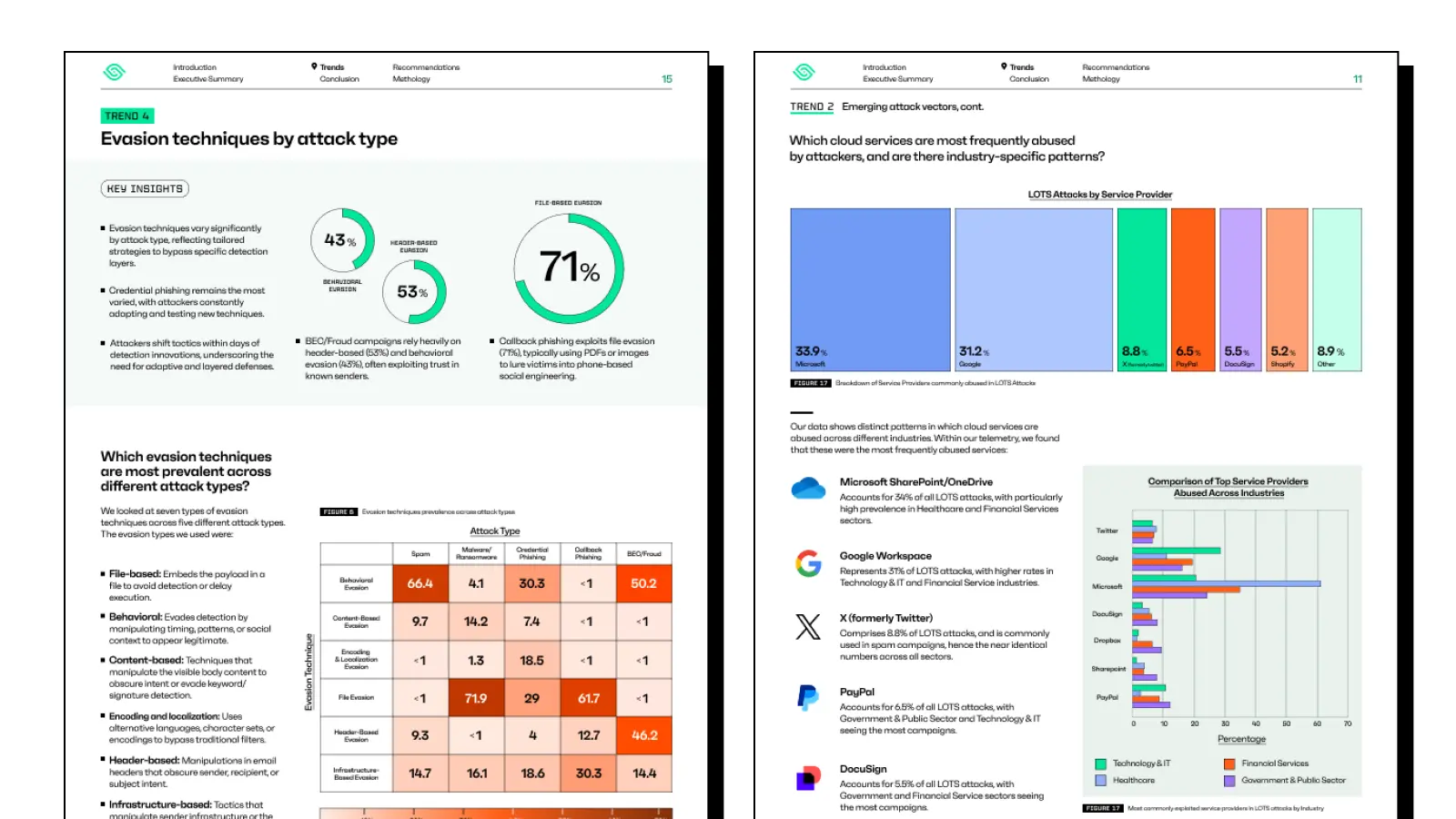
Evasion techniques by attack type
Evasion techniques vary significantly by attack type, reflecting tailored strategies to bypass specific detection layers. Attackers are not just changing payloads, they’re changing how they hide their delivery. For example, 71% of callback phishing exploits attachment-based evasion, typically using PDFs or images to lure victims into phone-based social engineering.
Evasion stacking
The complexity of email-based attacks continues to increase as threat actors combine multiple evasion techniques in a single campaign. This "evasion stacking" significantly reduces traditional detection rates and it has been observed across all major attack types.
The path forward
As attackers continue to evolve their techniques at an accelerating pace, security practitioners must embrace adaptive, intelligence-driven approaches that can respond quickly to emerging threats and anticipate future developments.
Sublime is an adaptive email security platform built for the way attackers operate today. Rather than waiting on signature updates or model refreshes, Sublime continuously analyzes detection signals from your environment, generates new coverage in near real time, and automatically validates it against historical data – without waiting on manual retraining.
Want to dive deeper? Read the full Sublime Email Threat Research Report (Q1 2025) to explore the data and insights shaping the future of email security.
Get the latest
Sublime releases, detections, blogs, events, and more directly to your inbox.



.avif)
