Agentic email security where AI works for you, not around you
Prevent more threats, respond faster, and spend less time on email security.










.svg)



.svg)


Traditional email security detection models fall short
How Sublime detects modern email attacks
Sublime layers multiple detection methods for explainable, actionable decisions on every message.
.svg)


%20(1).avif)
Sublime in numbers
80%
Faster user report investigation

.svg)
30%
Fewer false positives than other API email security solutions evaluated

.svg)
70%+
lower email security spend, achieved through tool consolidation

.svg)
20x
Attacks automatically detected and prevented
.svg)
.svg)
70%
Reduction in false positives using Sublime
.svg)
.svg)
5x
Efficiency gain — Cut weekly email security management time from 10 hours to under 2

.svg)
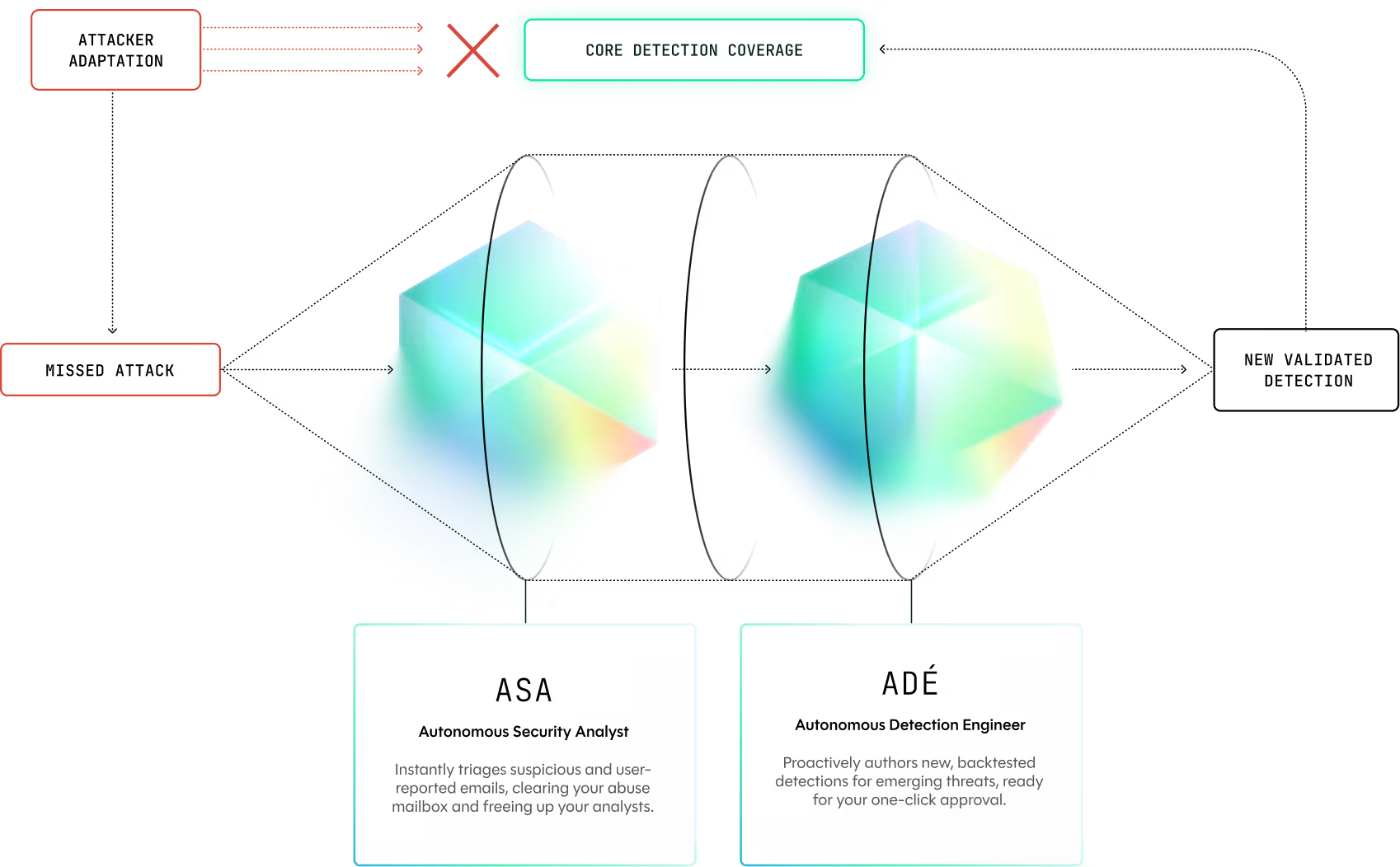
Meet your AI security agents
Sublime's agents automate critical workflows to make your entire defense more responsive and effective.
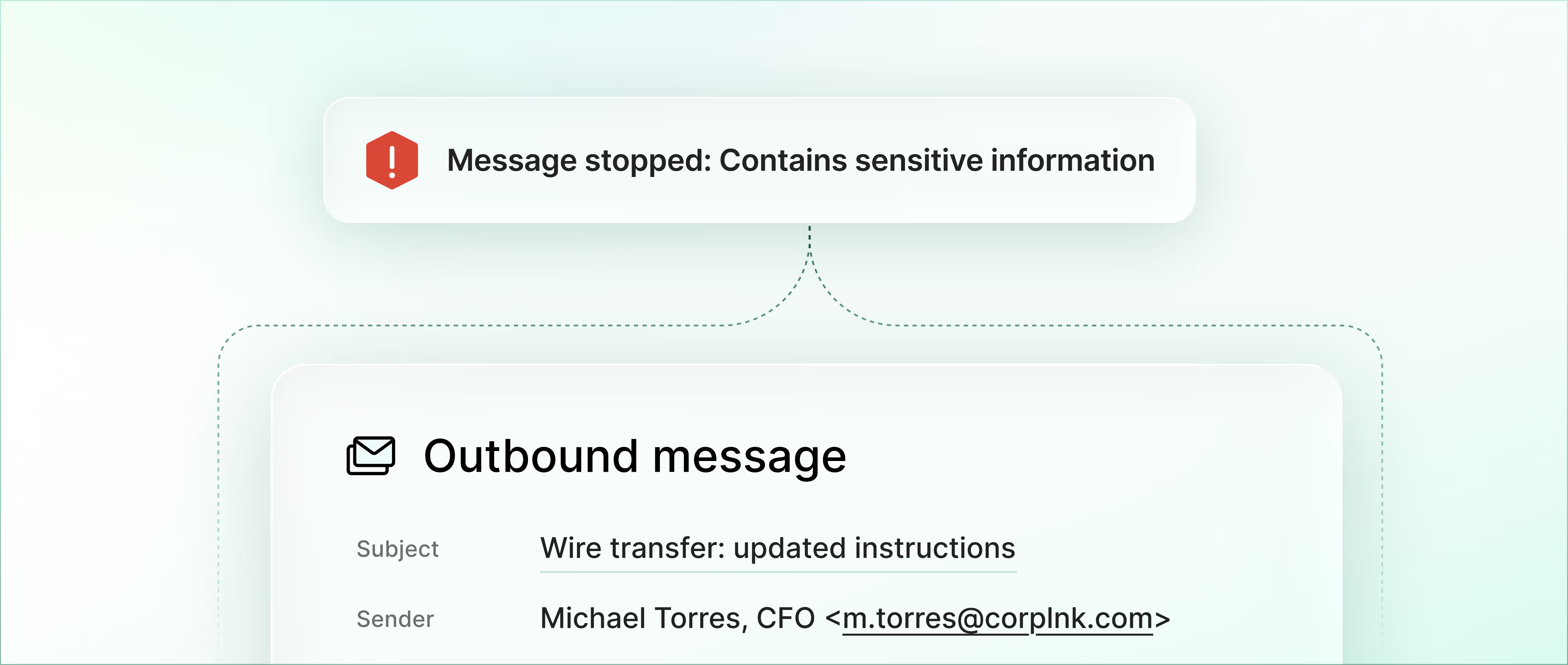
Extend your defense to outbound and internal email
The same detection engine that powers inbound protection catches sensitive data before it leaves your environment. Org-specific policies enforce compliance requirements and block data exfiltration in real time.

Integrate with your stack
Sublime connects to the tools you already run. Open, API-native, and built to fit your workflow.
Deploy your way
Microsoft 365 or Google Workspace via API. Multi-tenant SaaS, single-tenant cloud, or self-hosted. No MX record changes.
Threat intel and identity
Ingest threat feeds, YARA signatures, and indicators of compromise (IOCs). Automate provisioning with your IdP.
Export and orchestrate
Send enriched telemetry to your SIEM and trigger playbooks in your SOAR.
In a space filled with black-box AI solutions, working with a transparent and open platform that gives you everything you need to detect and prevent email attacks is gold dust.
Ready to see Sublime in action?
See how Sublime stops more attacks with less work.
Frequently asked questions
Is Sublime “a lot of work” to run day-to-day? Do we need detection engineers?
No. Sublime is autonomous by default, so teams get value without writing or maintaining detections. Advanced teams can go deeper (custom detections, threat hunting, tuning), but it’s optional.
Can we understand why something was flagged (vs. black-box verdicts)?
Yes. Every verdict includes reasoning and detection logic, so you can validate decisions, resolve false positives, and take action without waiting on a vendor.
Does Sublime support SSO and access controls like RBAC?
Yes. Sublime supports enterprise authentication and access controls, so you can safely grant access to the right teams.
Who can see message content in the platform?
Sublime includes access controls and auditing to balance investigation needs with privacy. You can scope who can view message content and review access via audit logs.
What retention and data export options do we have?
Retention is configurable. You can also export data for downstream use cases (for example, routing telemetry into your SIEM or SOAR).
Do you support link click tracking?
Yes. Sublime supports link click tracking, so you can see when users click links in emails and use that signal to prioritize investigation and response.
Can Sublime augment our current email security tools?
Yes. Sublime is designed to layer into your existing email security stack, so you don’t have to rip and replace what you have today. Keep Microsoft/Google native controls (and even an incumbent SEG) in place while adding autonomous triage/remediation and transparent, organization-specific detection. Sublime integrates via API (no MX record changes) and can export telemetry to your SIEM/SOAR to fit your workflows.
Now is the time
See how Sublime delivers autonomous protection by default, with control on demand.
.avif)






