Email security for financial services
Sublime adapts to new fraud tactics in hours and makes every detection explainable, so your team stays in control of high-stakes workflows like wires, payment approvals, and account changes.









.svg)



.svg)


Why traditional email security fails financial institutions
Static detection decays fast
Legacy gateways rely on known-bad indicators. Attackers generate new infrastructure and fresh campaign variants faster than these systems update.

Centralized models generalize
First-gen AI solutions use a single centralized model trained across all customers. This model plays it safe – catching obvious threats but missing targeted attacks unique to your firm.

Black-box verdicts block action
When a legacy tool gets it wrong, your team has no way to understand why. You file a ticket, wait days or weeks for the vendor to investigate.

Financial workflows amplify risk
The emails financial institutions handle look similar to the emails attackers forge. Traditional security tools cannot reliably distinguish a legitimate transaction from a fraudulent one.

How Sublime protects financial institutions
Protect every message with adaptive, org-specific detection and automation that spots fraud early, explains the “why,” and helps your team respond in minutes - not days
Multiple signal detection
Sublime reasons through intent, behavior, and content using techniques like natural language understanding, computer vision, and live link navigation. That means you can catch novel and fast-changing attacks that never show up on blocklists.
Distributed Detection Model (DDM)
Coverage adapts to your environment. Detections account for your vendors, communication patterns, and business workflows, so you get precision without forcing a one-size-fits-all model to guess.
Explainable, tunable decisions
See the reasoning behind every flagged message. Resolve false positives quickly and tune exceptions for legitimate financial workflows without waiting on a vendor.
Fast adaptation + workflow-aware automation
ADÉ deploys new coverage when threats emerge. ASA triages user-reported emails instantly. Together, they reduce both risk and operational burden.
Explore how Sublime integrates with your existing email and security infrastructure.
Common email threats targeting financial institutions
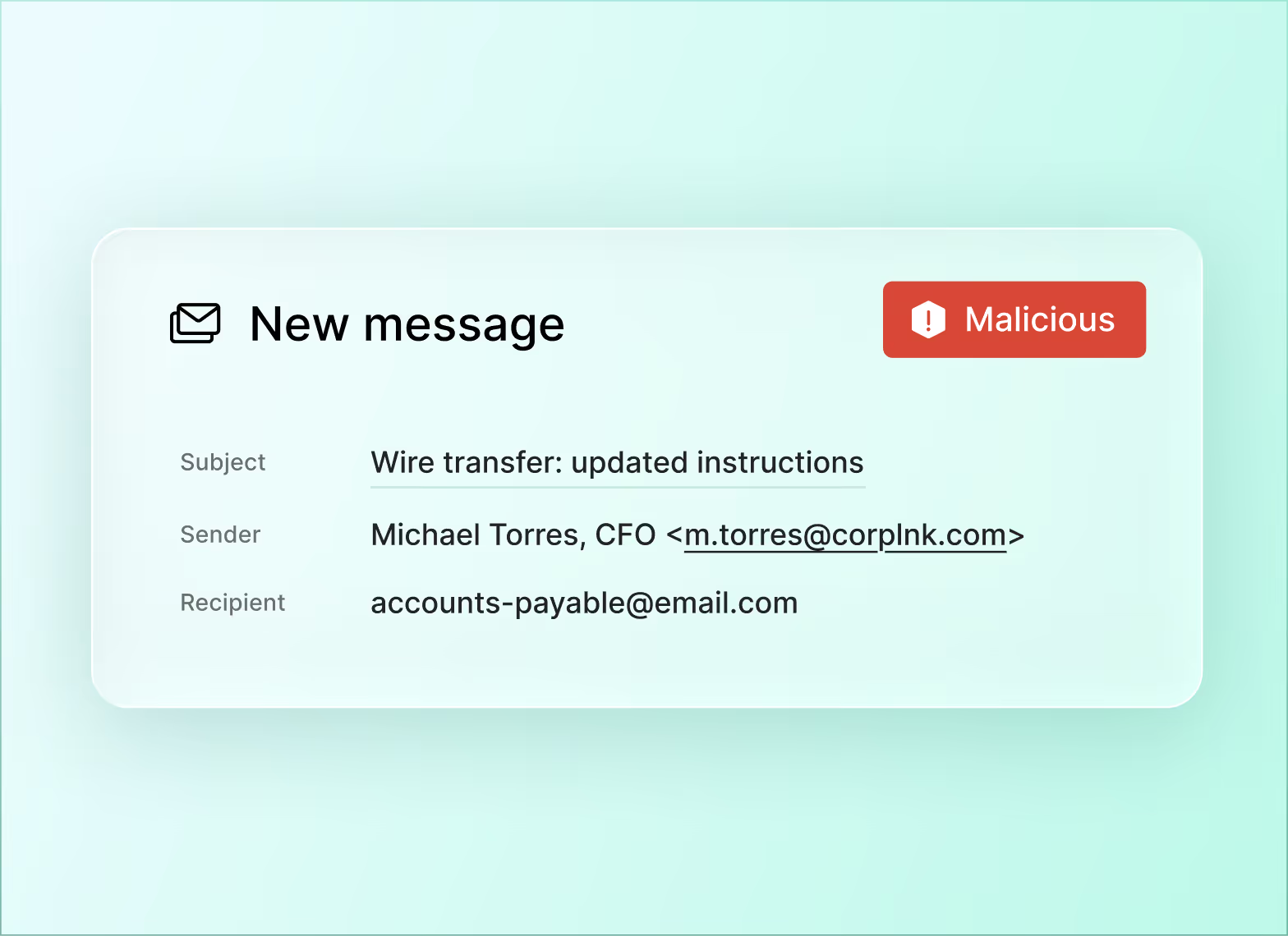
Business email compromise (BEC)
BEC exploits trust in financial workflows, using impersonation to trick employees into sending money or sharing sensitive information. A spoofed approval request can move hundreds of thousands of dollars. Financial services teams are targets because payment approvals and vendor change requests are routine.
Credential phishing
Sophisticated phishing campaigns use fake login pages, branded document-sharing notifications, and multi-step redirect chains to harvest employee credentials. With generative AI, attackers outpace defenses that rely on known-bad indicators.
Vendor impersonation
Attackers spoof or compromise trusted third-party vendors to send fraudulent invoices, payment updates, or document requests. They blend seamlessly into legitimate transaction flows, making them difficult to detect.
Account takeover
Compromised internal accounts are weaponized to send phishing emails, exfiltrate data, or initiate unauthorized transactions from within a trusted domain. They bypass authentication checks and domain-based protections entirely.
Why financial security teams choose Sublime
Sublime delivers precise, explainable protection for high-stakes financial workflows - without slowing down business or sacrificing control.
Protects workflows, not just inboxes
Minimize workflow-breaking false positives on routine payment, account-change, and vendor communications, while stopping targeted fraud.
.svg)
Built for regulated environments
Transparent, auditable detections support SEC, FINRA, NYDFS, and similar frameworks. Self-hosted deployment options give full control over email data residency.
.svg)
.avif)
Fast time-to-protection
Close the gap between new campaigns and effective coverage without waiting weeks for vendor updates.
.svg)
.avif)
Reduce operational load
Automate large parts of investigation and triage so analysts can focus on true incidents instead of ticket queues and alert noise.
.svg)
Sublime in numbers
80%
Faster user report investigation

70%
Reduction in false positives using Sublime
.svg)
5x
Efficiency gain — Cut weekly email security management time from 10 hours to under 2

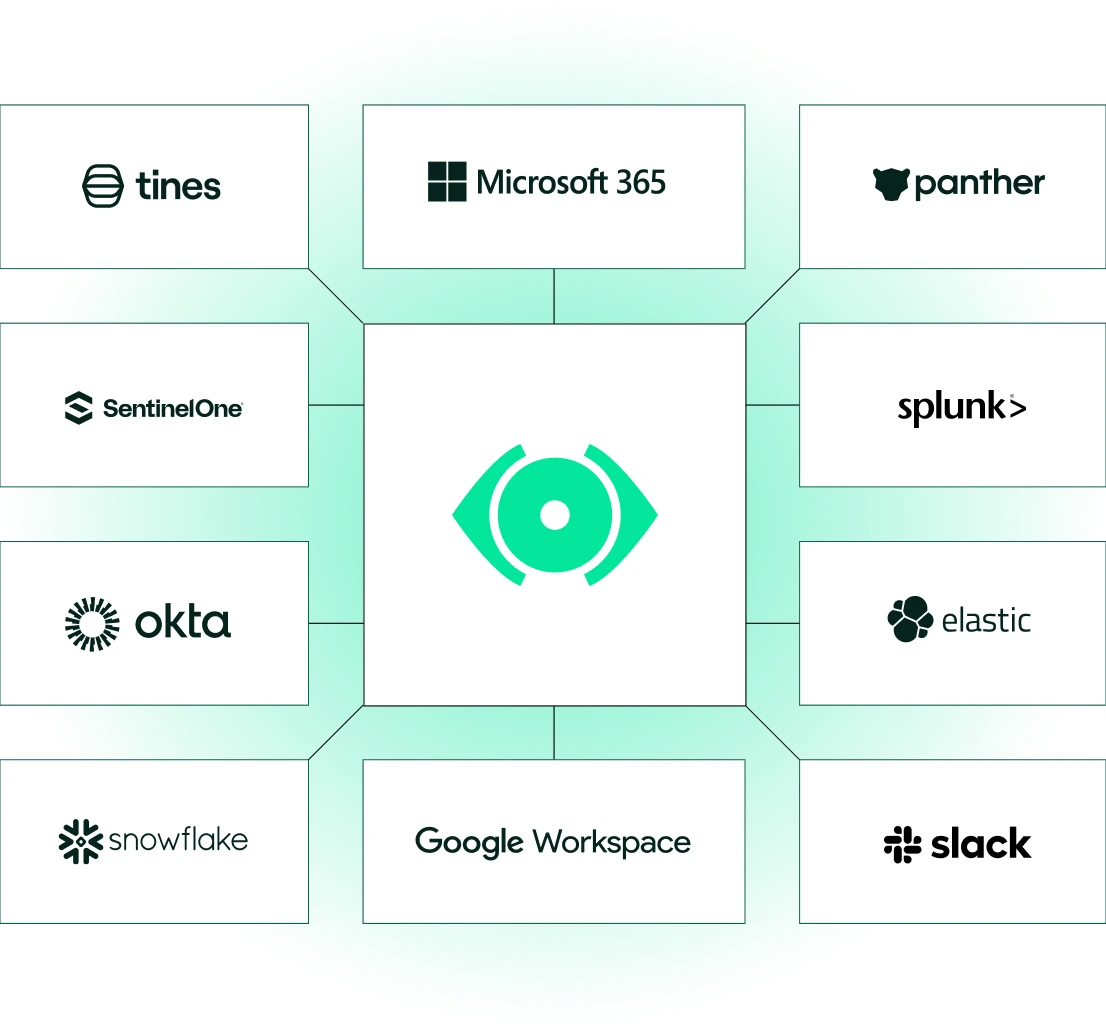
Fits your stack
Sublime connects to the tools you already run. Open, API-native, and built to fit your workflow.
Microsoft 365 and Google Workspace integration
Connect in minutes via API. No MX record changes, no disruption to mail flow.
Flexible deployment
Cloud SaaS, single-tenant SaaS, or self-hosted. API or inline protection.
SIEM and SOAR integration
Export events to your SIEM, trigger SOAR playbooks, and push alerts to Slack, so your team works from the tools they already use.
What our customers are saying
Email security FAQs for financial institutions
What should financial institutions look for in an email security platform?
Look for adaptive detection that goes beyond known-bad indicators, coverage for BEC, credential phishing, and vendor compromise, transparent decision-making so your team can act on results, flexible deployment options for regulated environments, and integration with your existing SIEM and SOAR tools. The platform should reduce investigation time from hours to seconds, not add another dashboard to check.
How do modern email security platforms integrate with existing security stacks?
Modern email security platforms connect to Microsoft 365 or Google Workspace via API – no MX record changes required. Events export to your SIEM for centralized visibility, and integrations with SOAR platforms enable automated response playbooks. Sublime also pushes alerts to Slack and other tools your team already uses.
How can financial organizations reduce investigation time for phishing incidents?
Automation is the key lever. ASA (Autonomous Security Analyst) triages user-reported messages instantly – investigating, classifying, and remediating without analyst involvement. Built-in threat hunting enables your team to search across your email environment, scope incidents, and identify compromised accounts from a single interface.
Why do phishing and impersonation attacks often bypass traditional email security gateways?
Traditional gateways rely on known-bad indicators like blocklists and signature databases. Modern attacks use fresh infrastructure, compromised trusted accounts, and AI-generated content that carries no prior reputation. Socially engineered attacks – BEC, vendor impersonation, hijacked threads – contain no malicious payload at all, just persuasive language. Gateways are not designed to detect intent. Sublime uses natural language understanding, computer vision, and behavioral signals to reason through intent and context, catching what reputation-based tools miss.
Who is Sublime designed for within financial security teams?
Sublime serves the full spectrum of financial security teams. SOC analysts and detection engineers benefit from transparent detection logic and the ability to customize coverage. Security leaders gain visibility into what is being caught, who is at risk, and what is being handled automatically. For lean teams, Sublime works autonomously from day one with no configuration required.
Now is the time
See how Sublime delivers autonomous protection by default, with control on demand.
.avif)

.svg)







