Agentic email security that stops more attacks with less work
Explore the platform tailored to your organization.
Stop more attacks with fewer false positives
Block the advanced threats that bypass legacy SEGs and centralized AI.
Adaptive detection engine
Sublime’s Distributed Detection Model (DDM) adapts with every message your organization sends and receives, creating coverage that’s tailored to your organization.
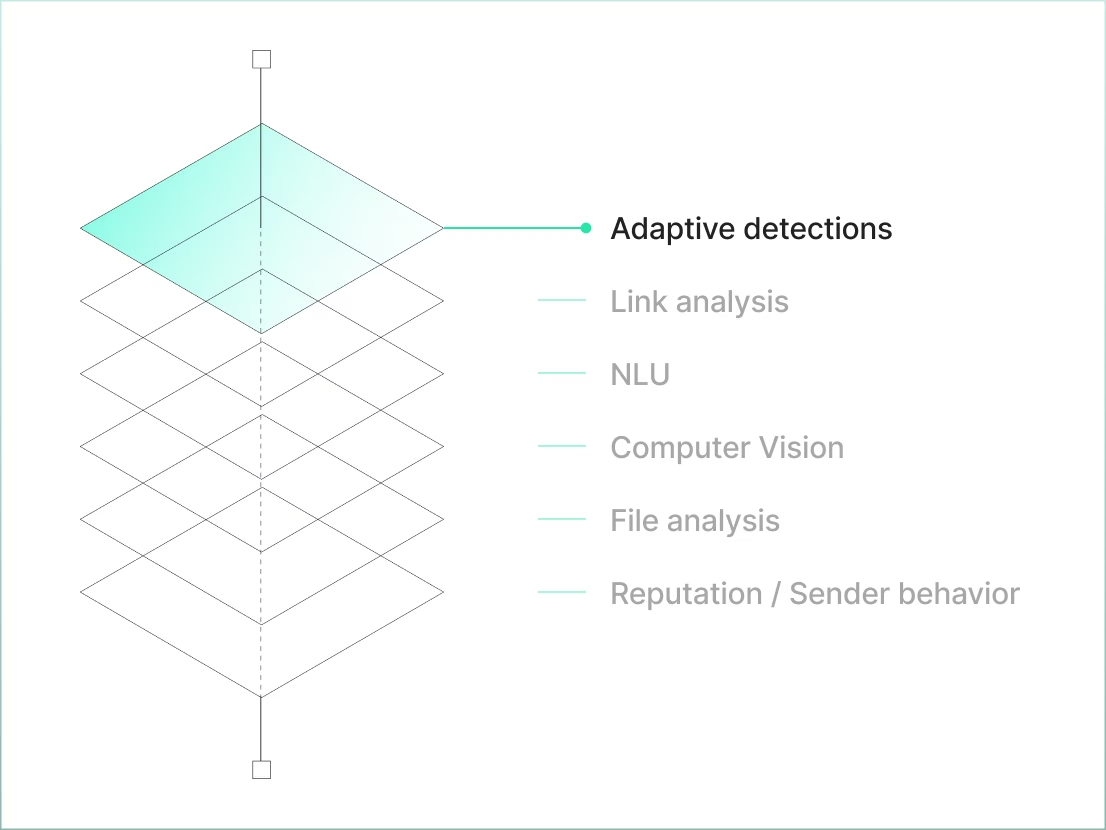
Cutting-edge analysis
Detections unmask hidden attacks with machine learning-powered enrichments including natural language understanding (NLU), computer vision, file explosion, dynamic link analysis, and more.
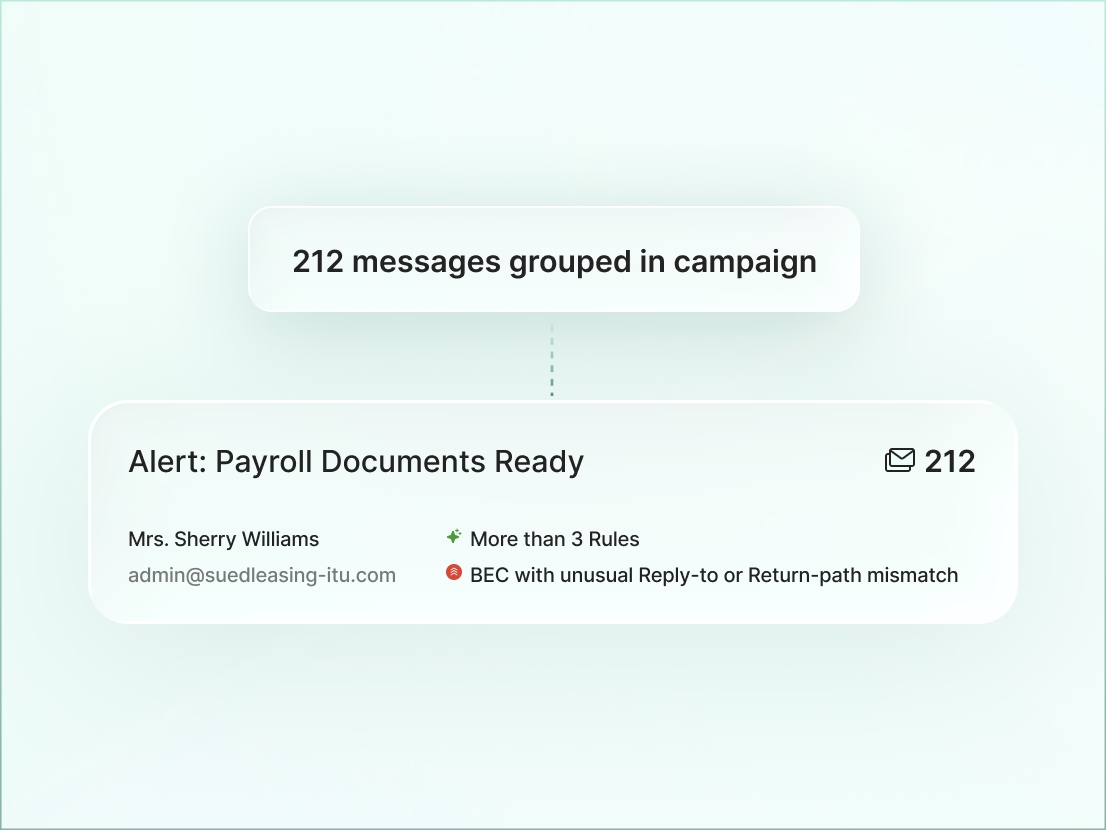
Campaign grouping
Sublime automatically groups related messages so analysts can investigate once and remediate across all affected mailboxes.

Threat hunting
Hunt for threats through historical email data using Sublime’s detection language to uncover latent threats and identify campaign patterns quickly. Instantly turn a hunt into detection coverage to stop future attacks.
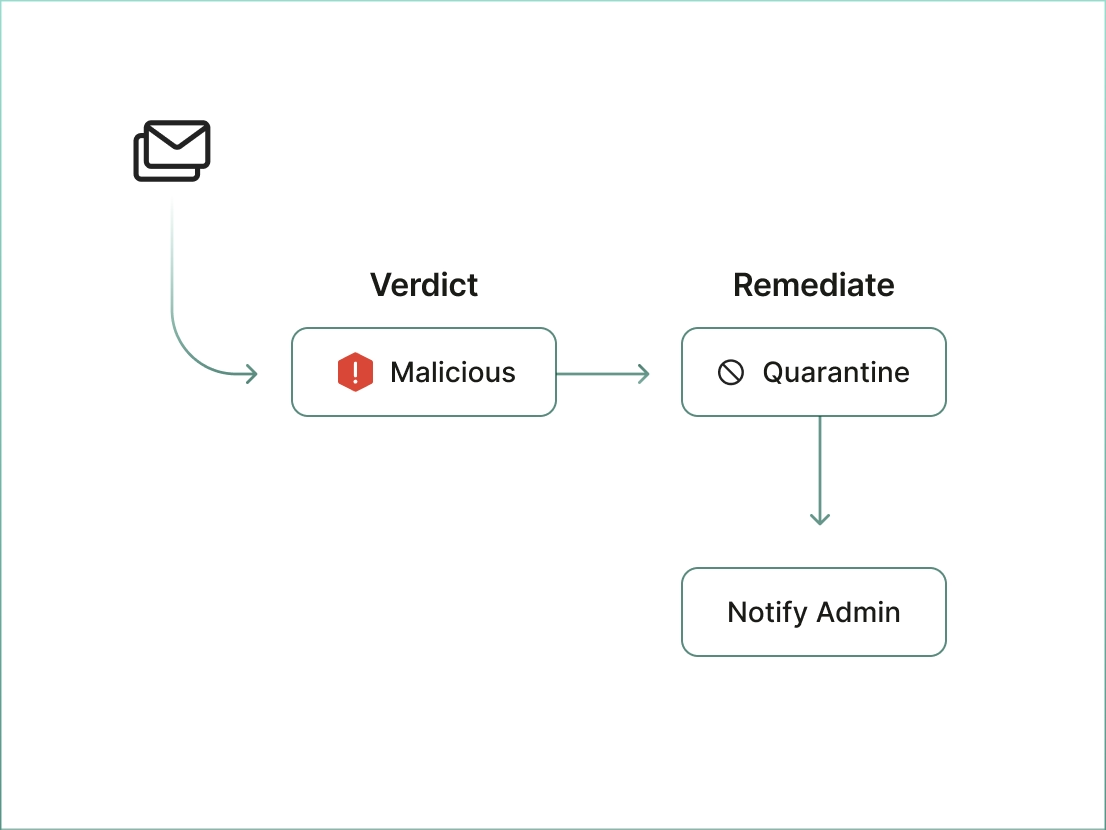
Precision remeditation
Automatically quarantine, delete, or warn users the moment a threat is detected, with a clear explanation of why, without disrupting legitimate business workflows.
Before Sublime, we were spending close to two hours a day managing email security. Now it’s just two hours a week, and we have even stronger protection.
Automate triage and response
Turn your manual review from a backlog to an automated defense loop.
ASA
Let our AI agent triage user-reported and suspicious emails for you. ASA clears your queue and provides explainable verdicts with investigation logs.
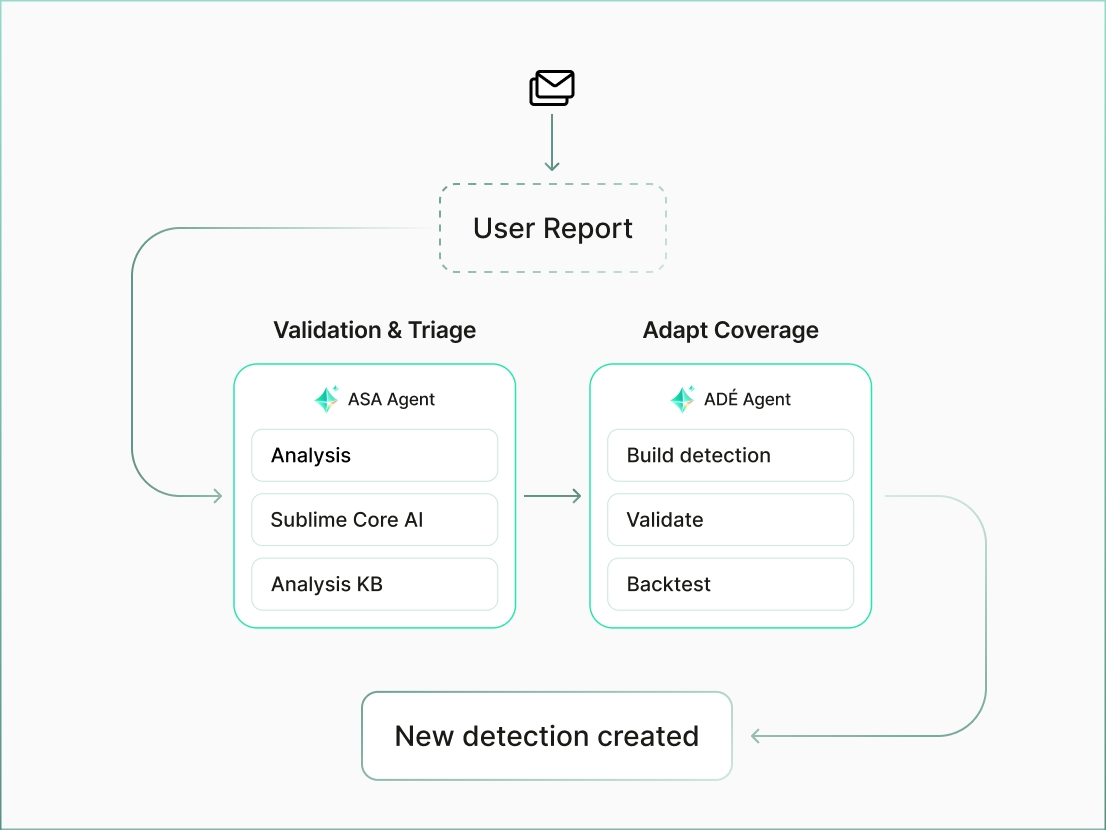
User reports & org-wide sharing
Empower users to report suspicious emails. When a threat is confirmed, protection is applied organization-wide, protecting every mailbox.
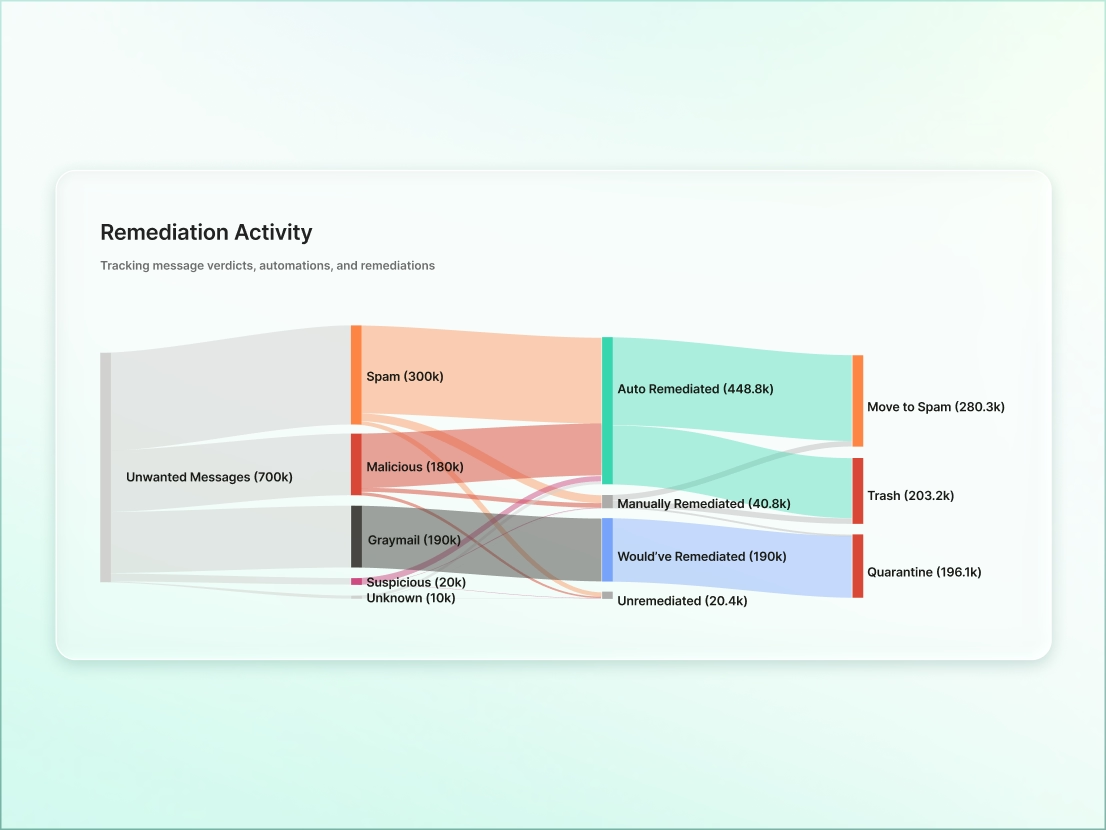
Spam & graymail control
Automatically filter promotional noise and bulk emails so your SOC stays focused on real threats.
Evolve defenses automatically
Turn novel attacks into permanent protections in hours, not months.
![Alert message showing a novel threat identified in an email with subject '[EXTERNAL] Cloud Vendor Audits...', sender 'i.e5454san@cap.bbiq.jp', recipient user@tyrellcorp.com, and ASA verdict marked as Malicious.](https://cdn.prod.website-files.com/68c8fbfee793a44f197e0dc3/69dfd054443009047b96d466_4311b31625a718df16a43f5dc75a950f_AD%C3%89.avif)
ADÉ
ADÉ creates and backtests org-specific coverage, then proposes it for deployment. Review and approve in a click.
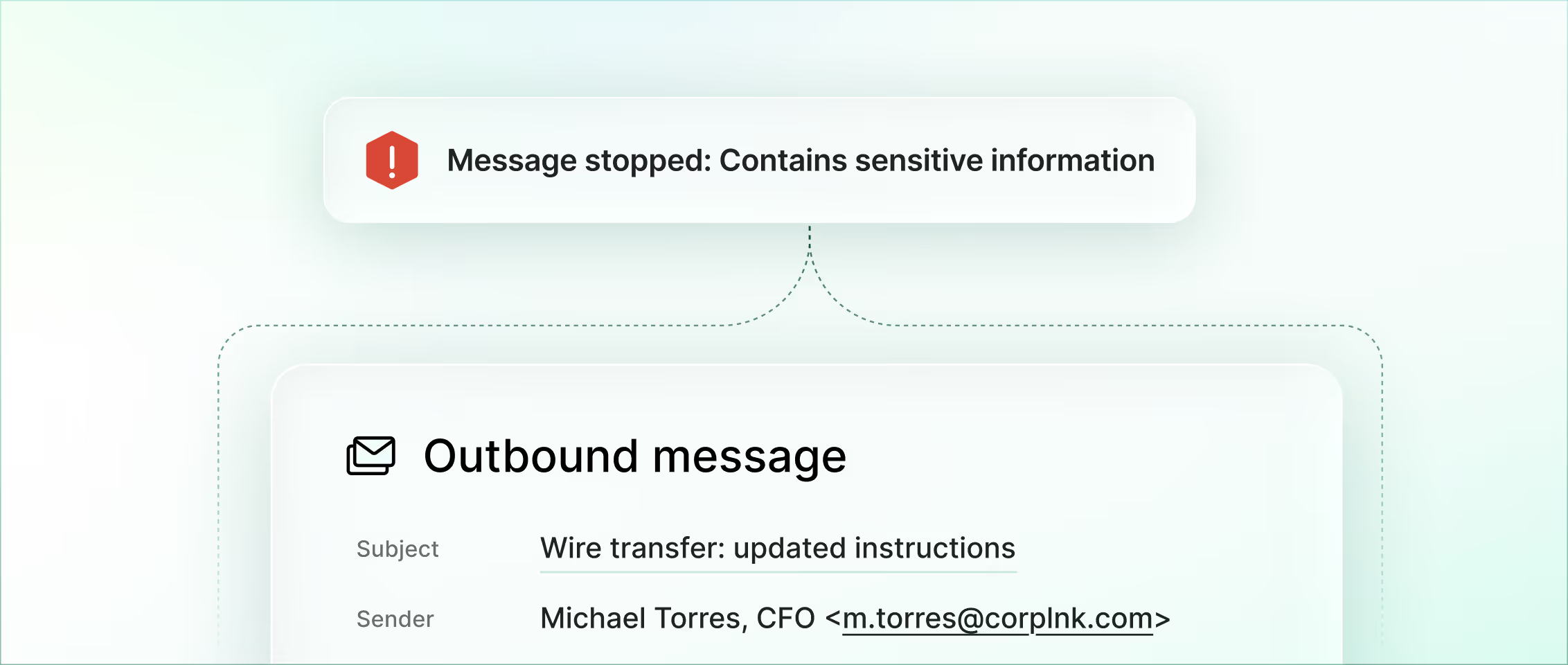
Email Data Loss Prevention
Prevent sensitive data exfiltration with Email Data Loss Prevention (DLP) using the same adaptive detection engine that powers your inbound defense.
Deploy your way
API-native integration with Microsoft 365 or Google Workspace. Choose multi-tenant SaaS, single-tenant private cloud, or fully self-hosted.
SIEM and SOAR exports
Send enriched data to your existing ops dashboard via webhooks and S3.

Threat intel integrations
Ingest external threat feeds (YARA, IOCs) and export your own indicators back to your Threat Intelligence Platform (TIP).
SSO and provisioning
Automate provisioning and simplify access with your Identity Provider (IdP).
Now is the time
See how Sublime delivers autonomous protection by default, with control on demand.
.avif)



