Sublime’s Attack Spotlight series is designed to keep you informed of the email threat landscape by showing you real, in-the-wild attack samples, describing adversary tactics and techniques, and explaining how they’re detected. These attacks can be prevented with a free Sublime account.
EMAIL PROVIDER: Google Workspace
ATTACK TYPE: Callback Phishing
The attack
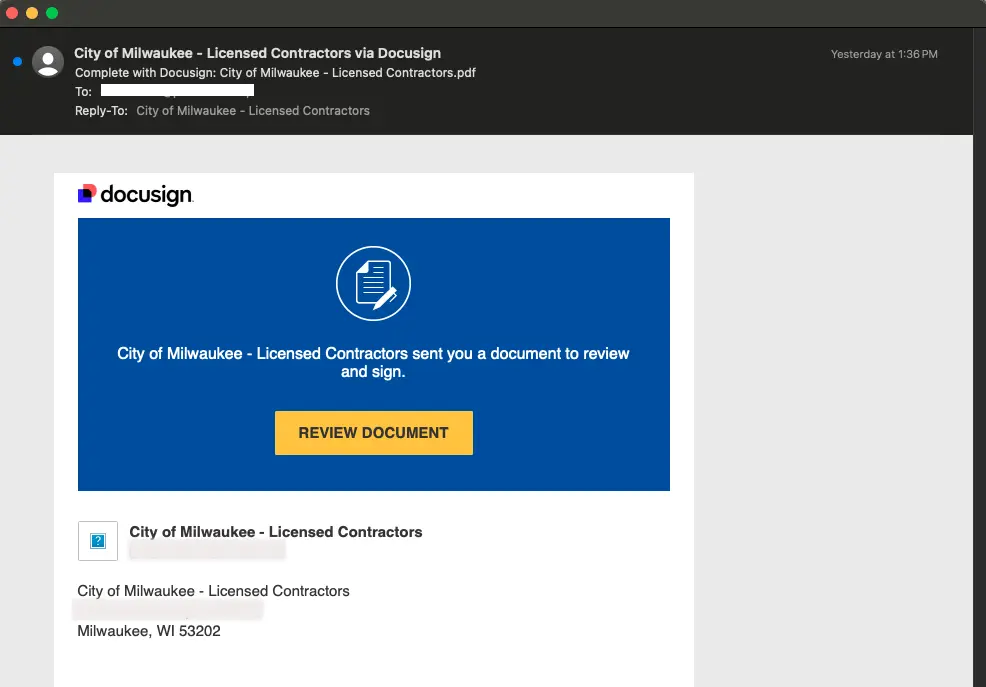
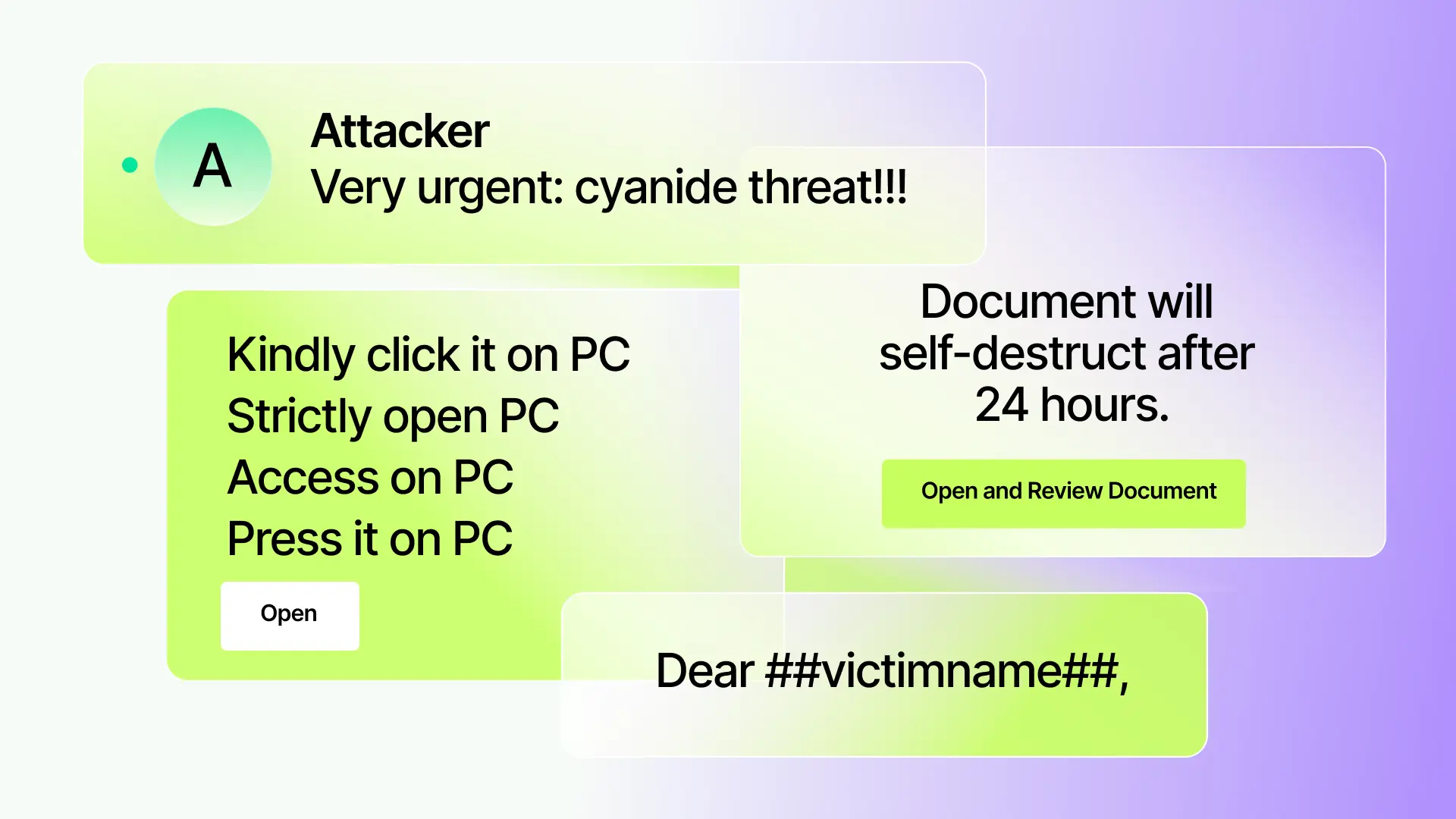
This recent callback phishing attempt in a Docusign comment reflects a growing trend of Living Off the Land (LOTL) attacks that abuse legitimate business services in order to evade detection. Docusign is one of many trusted business services we're seeing exploited. A few unique attack characteristics:
- The messages are legitimately from DocuSign – the sender is
docusign[.]netand it passes all sender authentication. The use of a high-trust sender domain from a commonly used business service blends in with other emails the recipient would expect to receive. - PayPal brand impersonation adds another layer of deception to build trust with the recipient.
- Financial transaction information in an e-signature service comment is unusual, but adds additional urgency for the recipient to make the call to the listed phone number.

Attack variants
We've seen numerous variants of these attacks with different intents, to include credential phishing. Even within industries the techniques differ. For example, in government/municipalities, we've observed fake licensing documents impersonating a city entity.
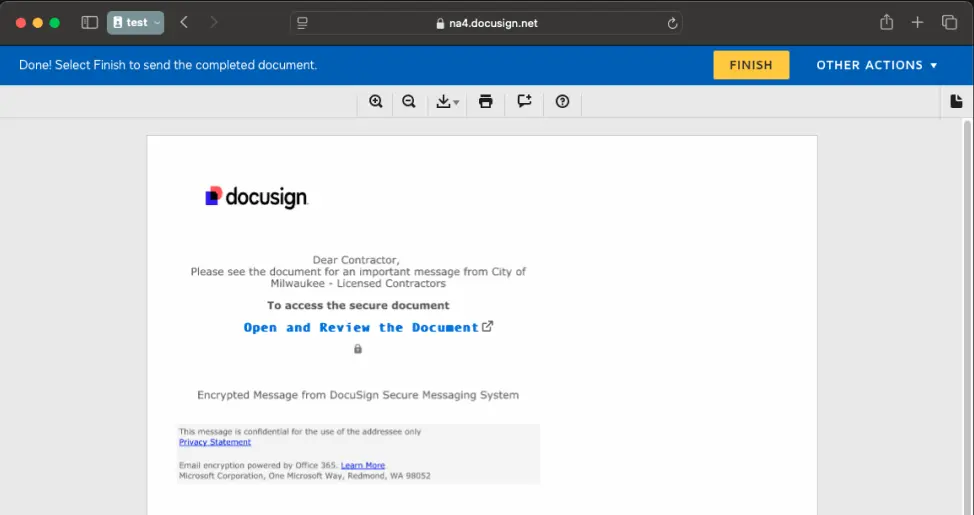
These variants require detection engines to have the capabilities to pick up the various signals that differ from industry to industry. At Sublime, we rely on a defense-in-depth approach, applying layers of detection logic to identify various anomalies in a message. We’ll do a deep dive on LOTL attacks in an upcoming blog post.
Detection signals
Sublime’s AI-powered detection engine prevented these attacks. See the top signals from our Core Feed Rules for Docusign service abuse and callback phishing via Docusign comments:
- Brand impersonation: Message contains references to brands commonly associated with callback phishing scams.
- Engaging callback phishing language: Language in the message appears to engage the user to call the sender, often to install malware or steal sensitive data.
- Suspicious reply-to: The sender
Reply-touses freemail or top-level domain (TLD) commonly abused in attacks.
Sublime prevents callback phishing, service abuse, and other email based threats. Deploy a free instance today.
Learn about other recent attack types that Sublime prevents:
Get the latest
Sublime releases, detections, blogs, events, and more directly to your inbox.


.avif)
