Sublime’s Attack Spotlight series is designed to keep you informed of the email threat landscape by showing you real, in-the-wild attack samples, describing adversary tactics and techniques, and explaining how they’re detected.
EMAIL PROVIDER: Google Workspace
ATTACK TYPE: Malware/Ransomware
The Attack
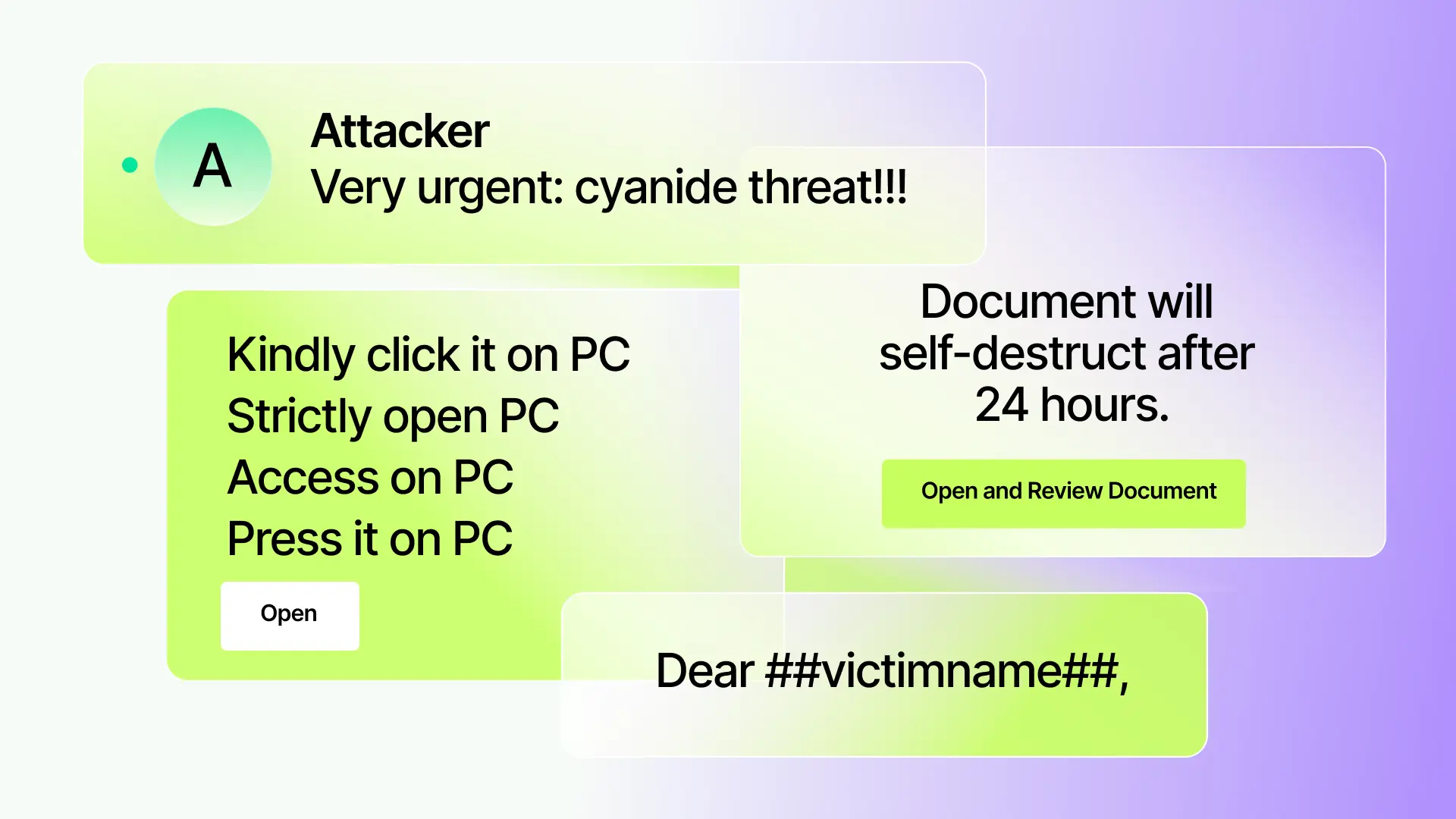
Attempts to deliver malware by sending a fake purchase order message. Attack characteristics:
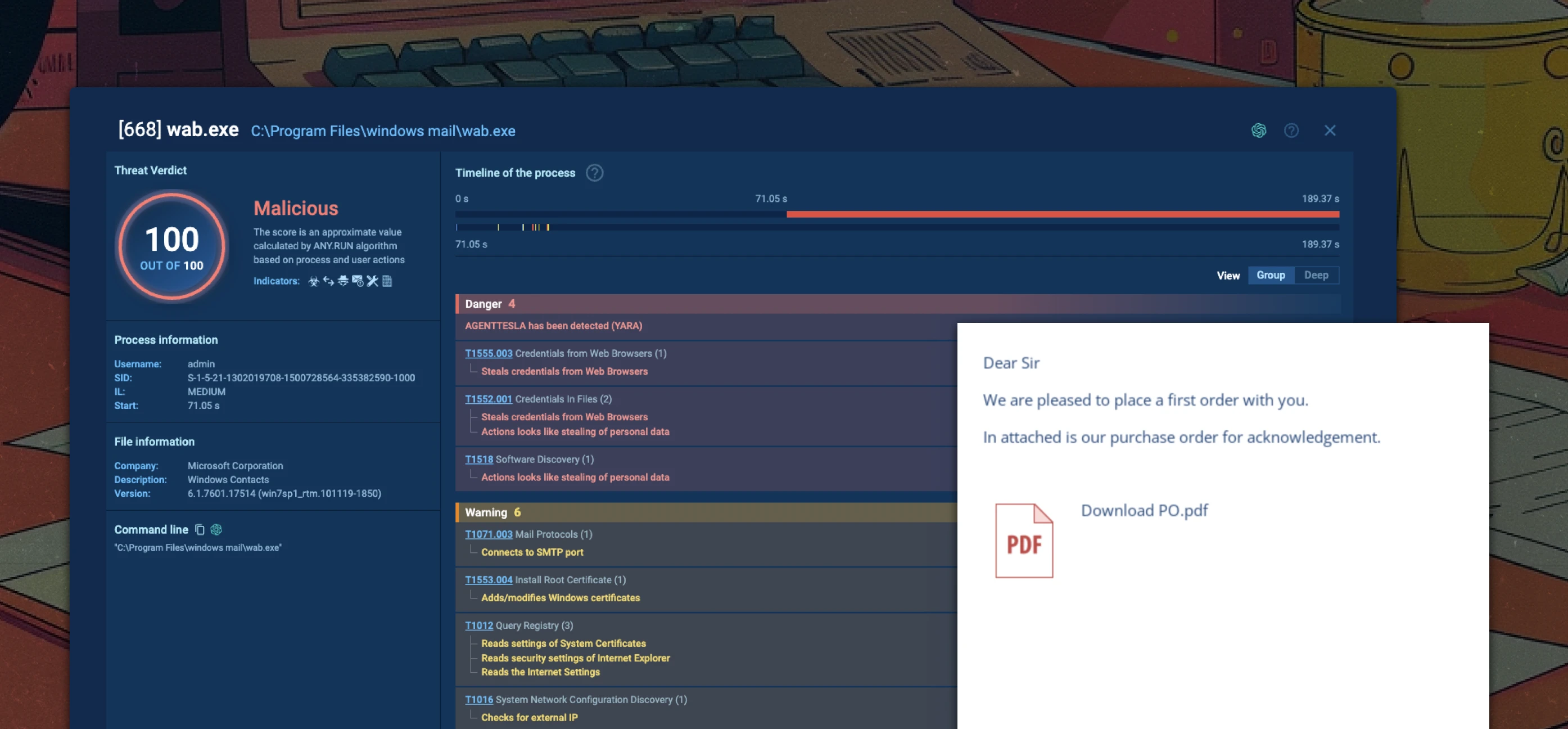
- Embeds a fake PDF logo to bolster legitimacy
- The fake logo and “Download PO.PDF” are hyperlinked to cdn[.]discordapp[.]com
- When the link is clicked, a VBE file is downloaded from Discord's CDN, which downloads and executes AgentTesla
Agent Tesla is a .Net-based Remote Access Trojan (RAT) and data stealer for gaining initial access that is often used for Malware-as-a-Service (MaaS). In this criminal business model, threat actors known as initial access brokers (IAB) outsource their specialized skills for exploiting corporate networks to affiliate criminal groups. As first-stage malware, Agent Tesla provides remote access to a compromised system that is then used to download more sophisticated second-stage tools, including ransomware.
Source
Detection signals
Sublime detected and prevented this attack using the following top signals:
- Free file hosting service: The malware is hosted on Discord’s file sharing server. By using high reputation infrastructure, the link is less likely to be deeply inspected.
- Link to auto-download of a suspicious file type: The link auto-downloads a VBE file, which is often used to deliver malware.
- Mismatched sender and reply-to: The message’s from address doesn’t match the reply-to. We typically observe this when the adversary has compromised an account to send the initial message, but may lose access, so they redirect replies to an account they own.
- Unknown sender: The sender has rarely, if ever, communicated with anyone at the targeted organization.
Sublime detects and prevents malware/ransomware delivery and other email based threats. Deploy a free instance today.
Get the latest
Sublime releases, detections, blogs, events, and more directly to your inbox.



.avif)
