Don’t compromise on BEC and fraud protection
Organizations lose billions to BEC and fraud attacks every year. Sublime's AI-powered BEC coverage can detect and prevent these deceptive attacks.

BEC/fraud in a nutshell
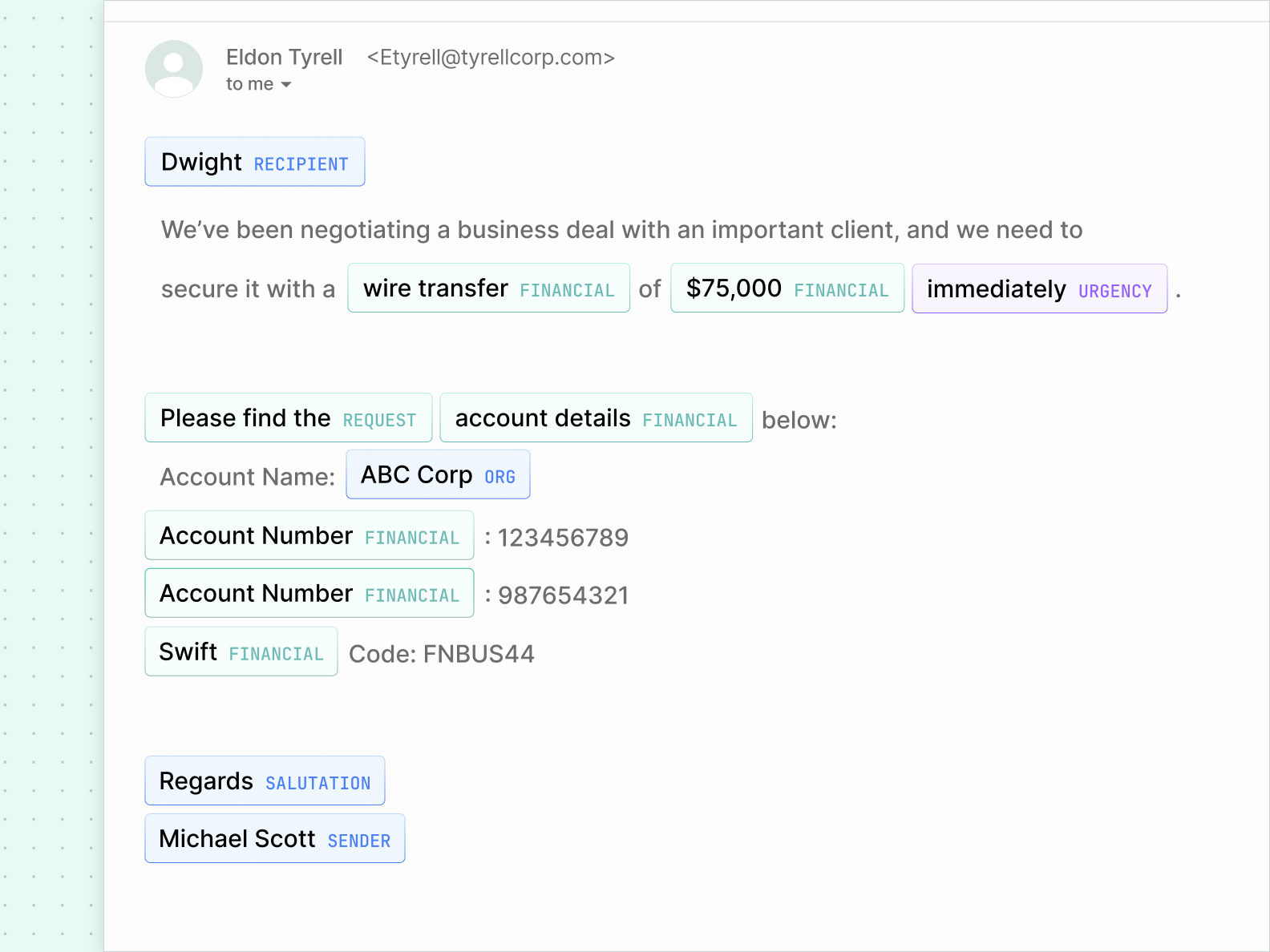
Business email compromise (BEC) and fraud attacks rely on deception, impersonation, and social engineering to trick targets into sharing sensitive information or transferring funds.
These attacks can bypass traditional security tools because the emails often seem harmless, with initial messages often used to collect information for a complex operation.
Fake invoices, manufactured threads, urgent wire transfers, payment updates, and more are used to start a conversation that can lead to wire fraud, compliance violations, and damage to an organization's reputation.
Sublime's platform was the only one that consistently identified the sophisticated social-engineering attacks that others missed. It passed every scenario we built.
What makes BEC/fraud attacks so effective
BEC attacks play the long game. There isn't a link to click or a file to download, just a conversation that leads to a socially engineered fraud.

GenAI
With LLMs, attackers can create, deliver, and iterate on attacks at a speed and scale beyond traditional security.

Impersonation
BEC attacks will often impersonate trusted people or institutions, leveraging trust to start the attack.

Manipulation
Attackers will use coercion, urgency, and other methods of manipulation to provoke engagement.

Multiple stages
BEC attacks can start with recon and artifact gathering, helping adversaries build out fake threads and narratives.
Tools for keeping BEC/fraud out of inboxes
BEC and fraud attacks can be difficult for security platforms to detect and prevent, but Sublime uses a layered combination of AI, machine learning, and org-specific detections to catch these threats.
Sublime's BEC protection uses Natural Language Understanding (NLU) to understand the intent of a message. By comparing the intent with the data and metadata of an email, Sublime can develop a picture of fraud from hundreds of small signals.
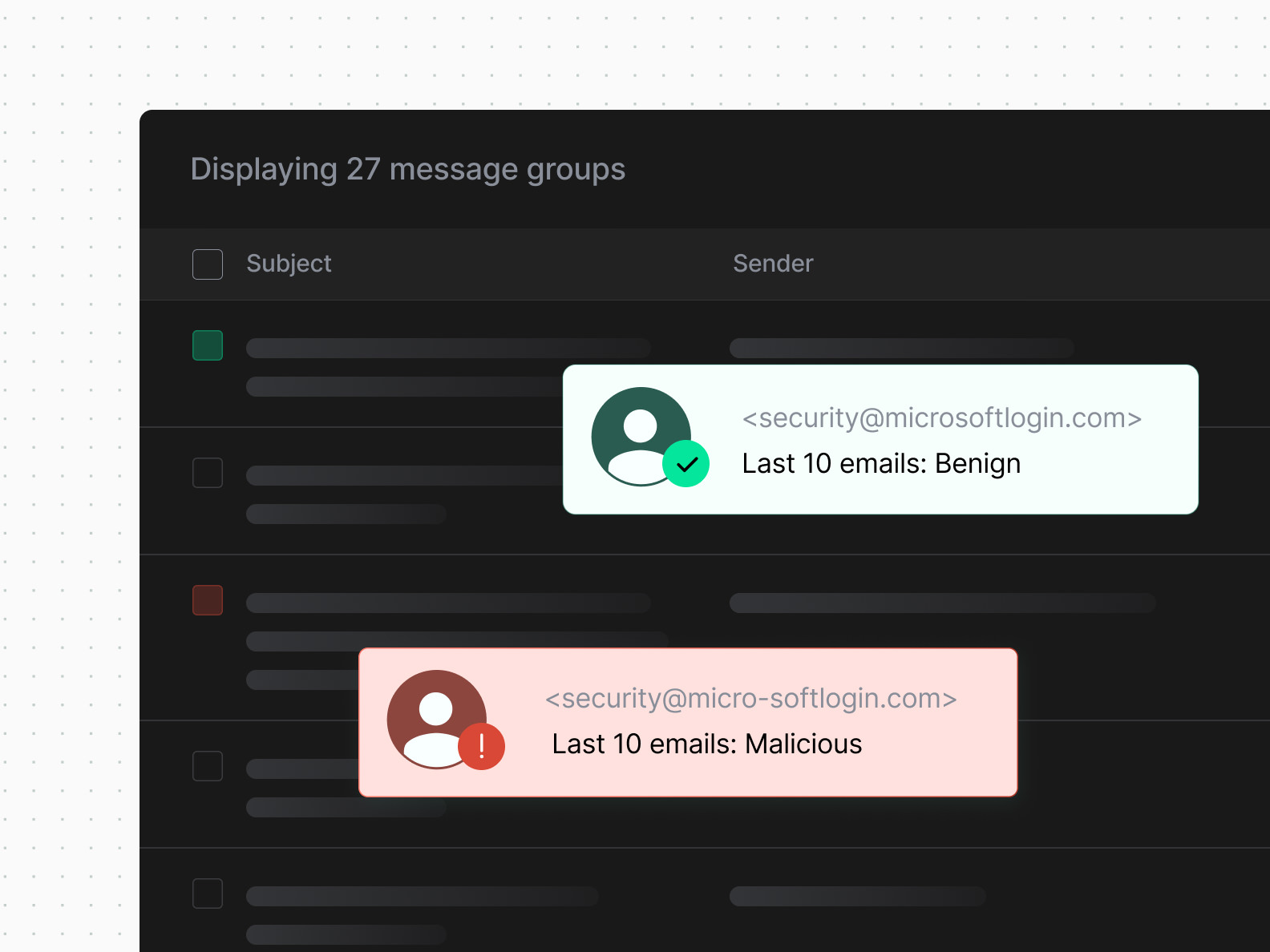
Sublime's business email compromise detection leverages a variety of org-specific signals, such as known VIPs, that can be used in comparative analysis against sender data. This includes domain lookalike identification, misspelling-based evasion detection via Levenshtein distance, and more.
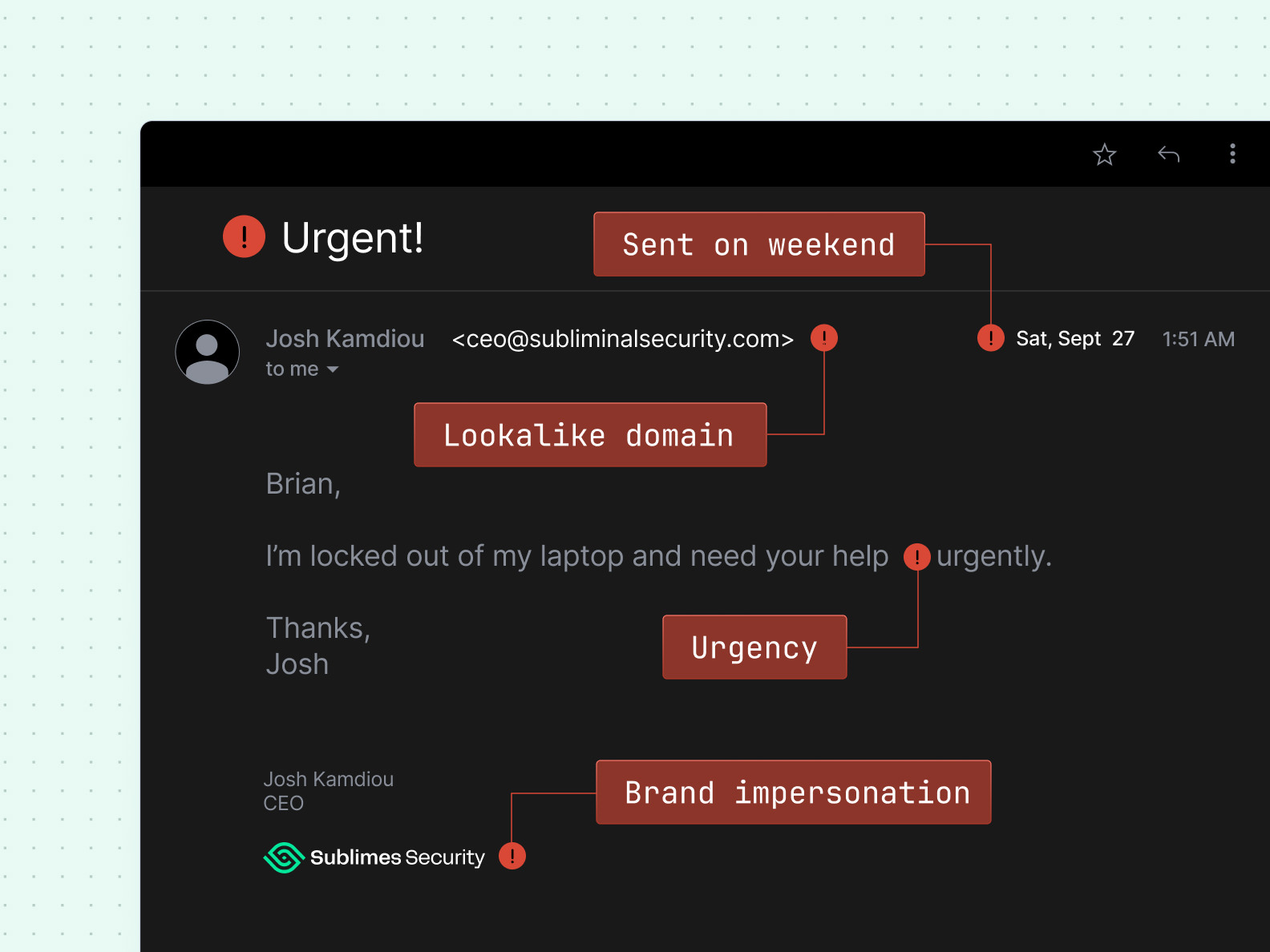
Sublime's BEC protection uses sender behavior, WHOIS registration data, and more to determine the trustworthiness of a message.
Sublime analyzes DKIM, DMARC, and SPF status of an email to clearly indicate if a sender has been spoofed rather than compromised.

Advanced BEC protection for your organization
See how Sublime's comprehensive business email compromise software can safeguard your business from BEC and fraud attacks.
Latest on BEC/fraud attacks
The latest news, research, and attack spotlights about BEC/fraud attacks.
Frequently asked questions
What is business email compromise (BEC)?
Business email compromise (BEC) is email-based fraud where attackers impersonate a trusted (or simply non-malicious) person or organization to trick someone into a high-impact action: sending money, changing payment details, or sharing sensitive data. BEC often relies on social engineering (credibility, urgency, etc.), not malware, so the email can evade security.
How do business email compromise attacks work?
Most BEC follows a pattern. Attackers research workflows, compromise or impersonate a sender, and send a message designed to bypass controls. The technical setup varies (lookalike domains, display-name spoofing, thread hijacking, or full account takeover), but the goal is the same: trigger or redirect a payment, capture credentials, or extract sensitive information.
What are common examples of BEC attacks?
Common BEC tactics include invoice fraud (“new bank account”), executive impersonation requesting a wire, payroll direct-deposit changes, gift card requests, and HR data grabs (W-2s, employee lists). Another frequent pattern is a compromised vendor mailbox used to change payment instructions within an existing thread. Thread hijacking is especially effective because they inherit real context, trusted participants, and timing.
Why are BEC attacks difficult to detect?
BEC is tough because it often has no malicious link or attachment, uses real names and business context, and exploits authority and urgency. Spoofing and compromised legitimate accounts reduce obvious identity tells. Many defenses still prioritize technical indicators (URLs, attachments), while BEC succeeds through social engineering and workflow gaps.
How can organizations prevent business email compromise?
Use layered controls: - Identity: enforce MFA, monitor sign-ins, harden sessions, and monitor mailbox rules and forwarding. - Anti-spoofing: SPF, DKIM, DMARC; external sender labeling; lookalike-domain detection. - Process: out-of-band verification for bank changes; dual approvals; vendor master controls; no-exceptions rules. - People: train finance, HR, exec assistants, and IT help desk on link-free BEC scenarios.
What is the difference between phishing and business email compromise?
Phishing is a broad set of tactics to steal credentials or deliver malware, often at scale. BEC is a fraud category that targets business workflows (payments, payroll, data requests) and is often targeted and context-rich. BEC may use phishing to gain access, but many BEC emails succeed without any link or attachment.
Can AI-generated emails increase the risk of BEC attacks?
Yes. AI helps attackers write polished, role-specific messages, localize language, and respond fast in realistic back-and-forth. That increases success rates for social engineering. Strong process controls (verification for payment changes, dual approvals) still block many attempts, even when the email reads as legitimate.
What should you do if your organization experiences a BEC attack?
Move quickly: 1. Contact the bank to recall, freeze, or trace funds. 2. Escalate to security/IT, finance, legal, and leadership. 3. Secure accounts: reset credentials, revoke sessions, review MFA, and check mailbox rules and forwarding. 4. Preserve evidence: keep emails and headers. 5. Scope impact: who was accessed, what conversations were exposed. 6. Notify affected vendors or customers via verified channels. 7. Engage incident response and, when appropriate, law enforcement. 8. Fix the gap: tighten verification and monitoring so it does not recur.
Now is the time
See how Sublime delivers autonomous protection by default, with control on demand.
.avif)