- ICS Phishing
Attack Types
BEC/Fraud
Callback Phishing
Credential Phishing
Extortion
Malware/Ransomware
Reconnaissance
Spam
Tactics and Techniques
Encryption
Evasion
Exploit
Free email provider
Free file host
Free subdomain host
HTML smuggling
ICS Phishing
Image as content
Impersonation: Brand
Impersonation: Employee
Impersonation: VIP
IPFS
ISO
LNK
Lookalike domain
Macros
OneNote
Open redirect
Out of band pivot
PDF
Punycode
QR code
Scripting
Social engineering
Spoofing
Detection Methods
Archive analysis
Content analysis
Computer Vision
Exif analysis
File analysis
Header analysis
HTML analysis
Javascript analysis
Macro analysis
Natural Language Understanding
Optical Character Recognition
OLE analysis
PDF analysis
QR code analysis
Sender analysis
Threat intelligence
URL analysis
URL screenshot
Whois
XML analysis
YARA
Tactic or Technique: ICS Phishing
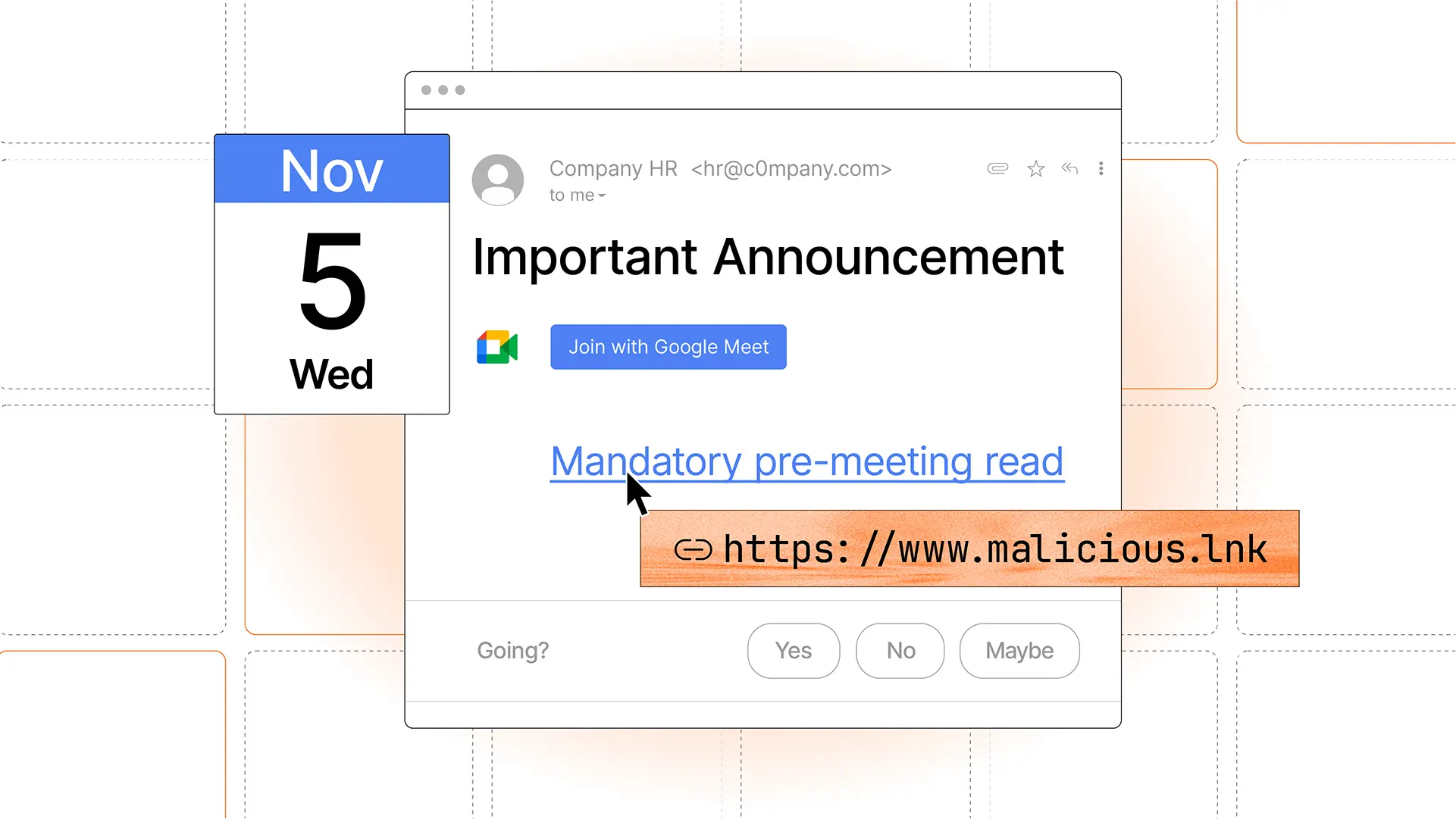
ICS phishing is a deceptive attack technique that uses calendar invite files (.ics) to deliver phishing content in a way that feels routine and trustworthy. These invites often appear as legitimate meeting requests from platforms like Microsoft 365 or Google Workspace, making them easy to accept without suspicion.
What makes this technique especially effective is how calendar systems handle invitations. In many environments, events can be automatically added to a user's calendar, giving attackers a second delivery channel beyond the inbox.
Once on the calendar, these events can contain phishing links, malicious attachments, or urgent instructions. Because calendar entries are persistent and trusted, the attack can continue even after the email is removed, increasing the likelihood of credential theft, malware downloads, or other compromise.
Blog Posts
Attack Types (5):
Detection Methods (10):