- Malware/Ransomware
Attack Types
BEC/Fraud
Callback Phishing
Credential Phishing
Extortion
Malware/Ransomware
Reconnaissance
Spam
Tactics and Techniques
Encryption
Evasion
Exploit
Free email provider
Free file host
Free subdomain host
HTML smuggling
ICS Phishing
Image as content
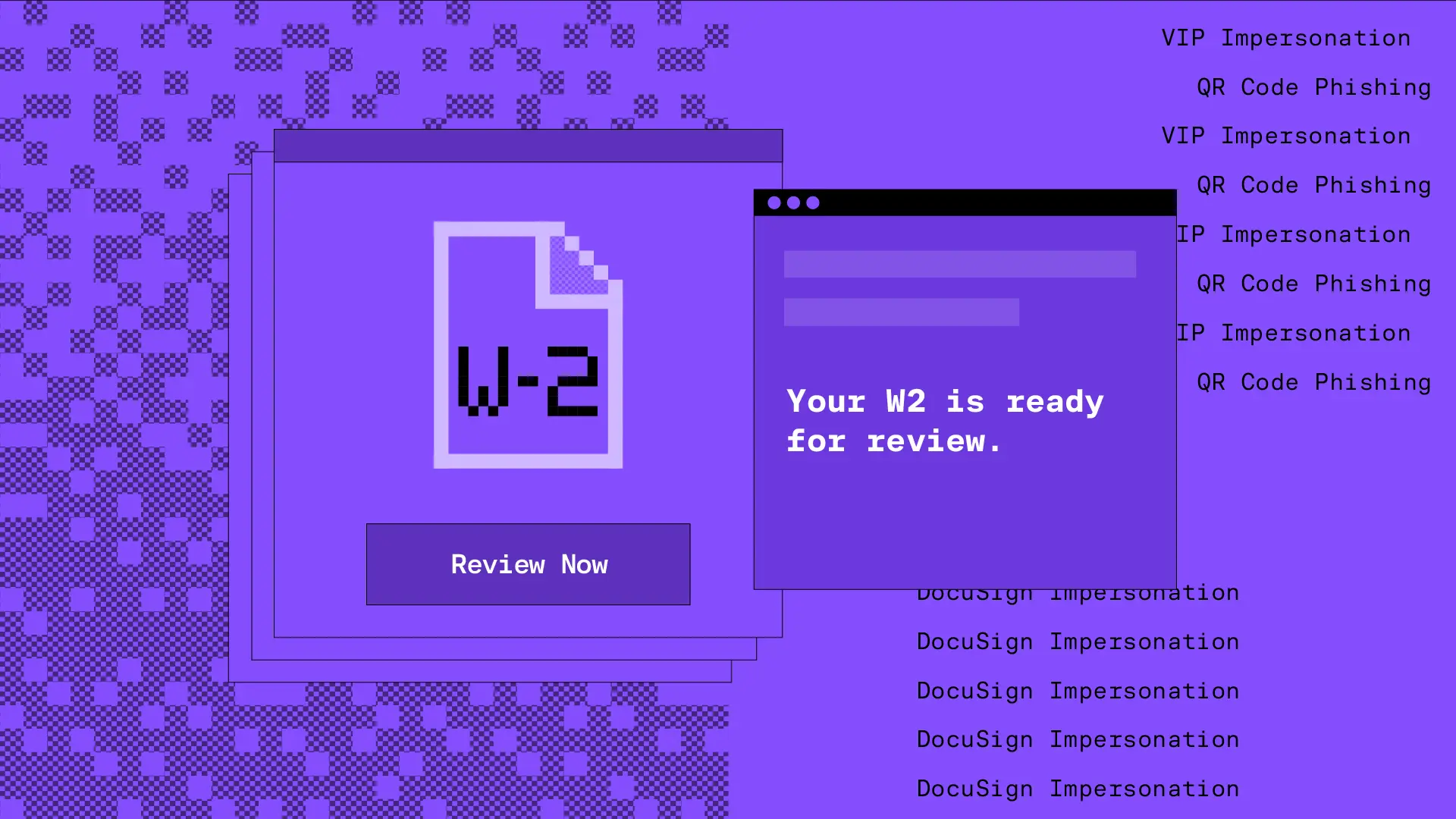
Impersonation: Brand
Impersonation: Employee
Impersonation: VIP
IPFS
ISO
LNK
Lookalike domain
Macros
OneNote
Open redirect
Out of band pivot
PDF
Punycode
QR code
Scripting
Social engineering
Spoofing
Detection Methods
Archive analysis
Content analysis
Computer Vision
Exif analysis
File analysis
Header analysis
HTML analysis
Javascript analysis
Macro analysis
Natural Language Understanding
Optical Character Recognition
OLE analysis
PDF analysis
QR code analysis
Sender analysis
Threat intelligence
URL analysis
URL screenshot
Whois
XML analysis
YARA
Attack Type: Malware/Ransomware
Malware and Ransomware attacks are designed to infect your system through things like fake invoices, password-protected attachments, or files disguised as routine business documents. Once opened, they quietly install malicious software that can steal data, encrypt files, or open the door for more serious threats.
You might see things like macro-enabled Office documents, HTML attachments, or ZIP files that require a password. These are tricks to get around email filters and convince you to interact. Once the malware runs, it can connect to attacker-controlled servers, spread across your network, and even bring in more payloads.
Ransomware is especially damaging. It locks up your files and demands a payment—usually in cryptocurrency—to get them back. Some attackers also steal data and threaten to leak it if the ransom isn’t paid, a tactic known as double extortion. The impact can be severe, including downtime, lost data, financial loss, and reputational damage.
Blog Posts
Tax season email attacks: AdWind RATs and Tycoon 2FA phishing kits · Blog · Sublime Security

Detecting malicious AnonymousFox email messages sent from compromised sites · Blog · Sublime Security

Abusing Discord to deliver Agent Tesla malware · Blog · Sublime Security

Scripting Vector Grifts: SVG phishing with smuggled JS and adversary in the middle tactics · Blog · Sublime Security

Gotta Catch 'Em All: Detecting PikaBot Delivery Techniques · Blog · Sublime Security

QR Code Phishing: Decoding Hidden Threats · Blog · Sublime Security
Detecting QakBot: WSF attachments, OneNote files, and generic attack surface reduction · Blog · Sublime Security
Tactics & Techniques (27):
Impersonation: Email address
Social engineering
Evasion
Impersonation: Domain
Image as content
Open redirect
HTML smuggling
Impersonation: Brand
Scripting
PDF
QR code
Encryption
ICS Phishing
Free file host
Exploit
Free subdomain host
Lookalike domain
Macros
Impersonation: Employee
Free email provider
IPFS
Out of band pivot
LNK
OneNote
Spoofing
Punycode
ISO
Detection Methods (20):
Sender analysis
Header analysis
URL analysis
Content analysis
HTML analysis
File analysis
Archive analysis
Computer Vision
Natural Language Understanding
XML analysis
QR code analysis
Exif analysis
YARA
Optical Character Recognition
Threat intelligence
Javascript analysis
Whois
Macro analysis
OLE analysis
URL screenshot
Page 1 of 16