- Content analysis
Attack Types
BEC/Fraud
Callback Phishing
Credential Phishing
Extortion
Malware/Ransomware
Reconnaissance
Spam
Tactics and Techniques
Encryption
Evasion
Exploit
Free email provider
Free file host
Free subdomain host
HTML smuggling
Image as content
Impersonation: Brand
Impersonation: Employee
Impersonation: VIP
IPFS
ISO
LNK
Lookalike domain
Macros
OneNote
Open redirect
Out of band pivot
PDF
Punycode
QR code
Scripting
Social engineering
Spoofing
Detection Methods
Archive analysis
Content analysis
Computer Vision
Exif analysis
File analysis
Header analysis
HTML analysis
Javascript analysis
Macro analysis
Natural Language Understanding
Optical Character Recognition
OLE analysis
PDF analysis
QR code analysis
Sender analysis
Threat intelligence
URL analysis
URL screenshot
Whois
XML analysis
YARA
Detection Method: Content analysis
Content analysis looks at the language and structure of a message to identify signs of phishing, social engineering, and other malicious intent. Instead of scanning for keywords, this method uses natural language understanding (NLU) to detect meaning, intent, and tone across the message.
Content analysis helps detect:
- BEC attempts with urgent messages from executive impersonators
- Credential phishing disguised as login or document notifications
- Callback scams posing as account renewals or fake support
- Extortion threats or blackmail messages
- Financial or personal data requests in suspicious contexts
- Fake job offers targeting employees
- Invoice fraud, payroll fraud, and more
For example, a phishing email may impersonate a CFO asking for a wire transfer. Content analysis can flag the urgent tone, financial context, and impersonation attempt.
Blog Posts
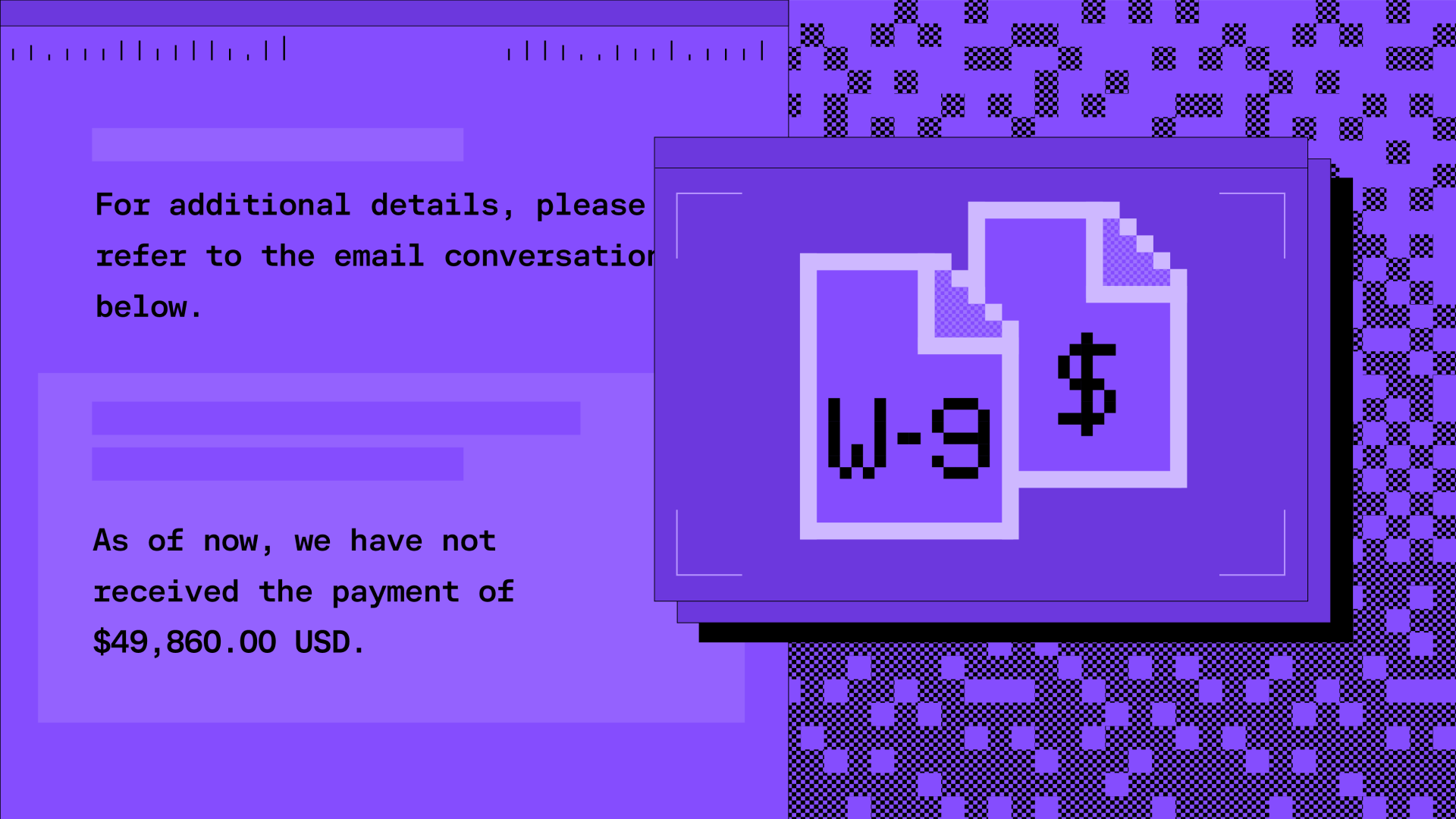
Hiding a $50,000 BEC financial fraud in a fake email thread · Blog · Sublime Security

Callback phishing via invoice abuse and distribution list relays · Blog · Sublime Security
Hidden credential phishing within EML attachments · Blog · Sublime Security
Living Off the Land: Credential Phishing via Docusign abuse · Blog · Sublime Security
Living Off the Land: Callback Phishing via Docusign comment · Blog · Sublime Security

Adversarial ML: Extortion via LLM Manipulation Tactics · Blog · Sublime Security
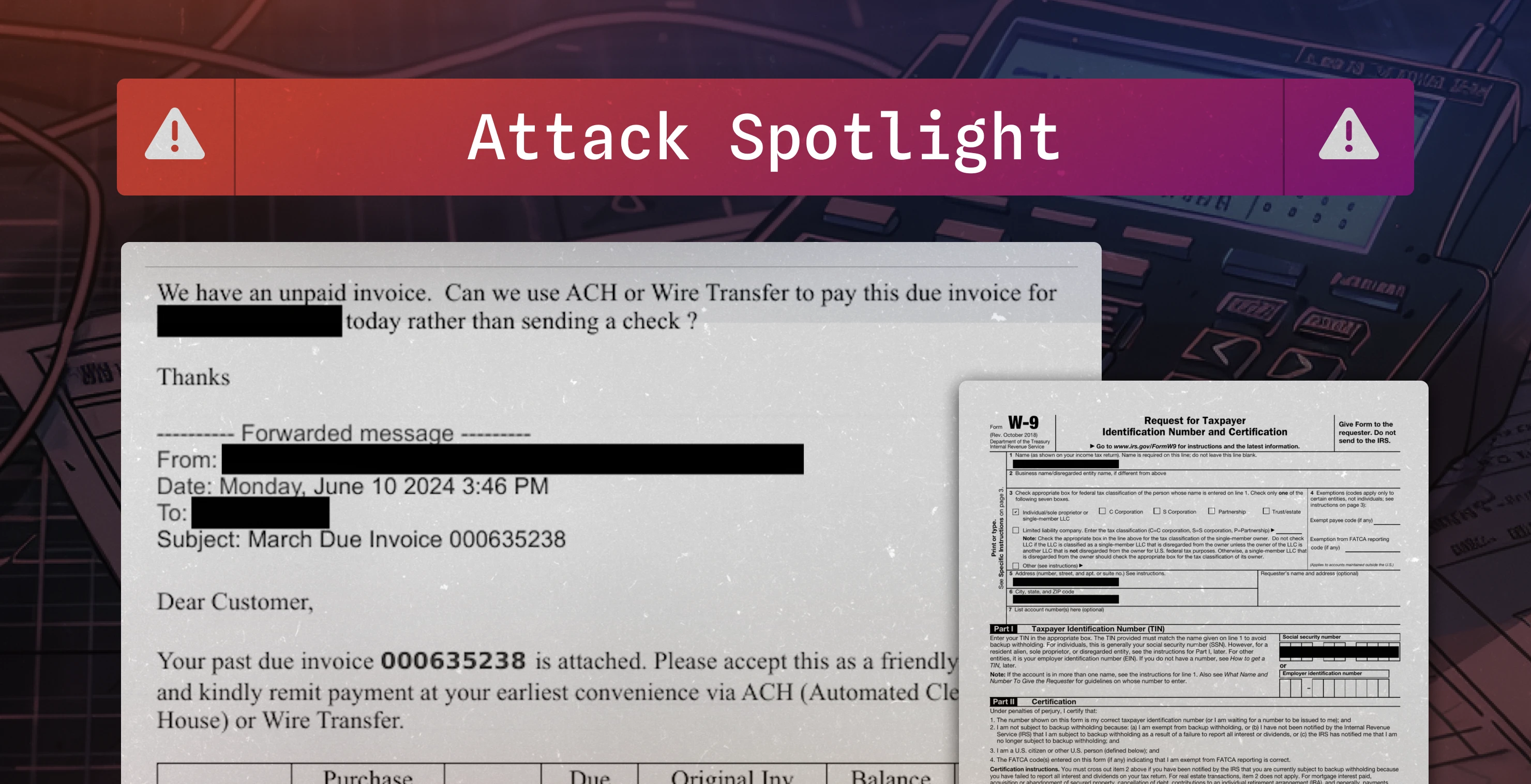
Fake invoice used to conduct $16,800 BEC attempt · Blog · Sublime Security

QR Code Phishing: Decoding Hidden Threats · Blog · Sublime Security

Call Me Maybe? The Rise of Callback Phishing Emails · Blog · Sublime Security
Detecting QakBot: WSF attachments, OneNote files, and generic attack surface reduction · Blog · Sublime Security
Attack Types (7):
Tactics & Techniques (26):
Free file host
Social engineering
PDF
Free subdomain host
Impersonation: Brand
Out of band pivot
Impersonation: VIP
Image as content
Free email provider
Evasion
QR code
Open redirect
Encryption
Scripting
Spoofing
Lookalike domain
Impersonation: Employee
Exploit
Macros
Credential Phishing
HTML injection
HTML smuggling
OneNote
LNK
IPFS
ISO
Page 1 of 25