Attack Types
BEC/Fraud
Callback Phishing
Credential Phishing
Extortion
Malware/Ransomware
Reconnaissance
Spam
Tactics and Techniques
Encryption
Evasion
Exploit
Free email provider
Free file host
Free subdomain host
HTML smuggling
Image as content
Impersonation: Brand
Impersonation: Employee
Impersonation: VIP
IPFS
ISO
LNK
Lookalike domain
Macros
OneNote
Open redirect
Out of band pivot
PDF
Punycode
QR code
Scripting
Social engineering
Spoofing
Detection Methods
Archive analysis
Content analysis
Computer Vision
Exif analysis
File analysis
Header analysis
HTML analysis
Javascript analysis
Macro analysis
Natural Language Understanding
Optical Character Recognition
OLE analysis
PDF analysis
QR code analysis
Sender analysis
Threat intelligence
URL analysis
URL screenshot
Whois
XML analysis
YARA
Attack Type: BEC/Fraud
Business Email Compromise (BEC) and fraud attacks rely on deception and social engineering. Instead of using links or attachments, attackers impersonate trusted figures like coworkers, executives, or vendors to trick you into sharing sensitive information or transferring funds. These attacks can bypass traditional security tools because the emails often seem harmless.
Expect fake invoices, urgent wire transfer requests, or a vendor asking you to update payment details. The first email is usually brief—just enough to start a conversation. The attacker might spoof a display name, reply to an old thread, or ask you to continue the conversation via personal email or phone. That is often the giveaway.
Even though these attacks may appear low-effort, the impact can be significant. They can lead to wire fraud, compliance violations, and damage to the organization's reputation. Organizations lose billions to BEC attacks each year.
Blog Posts
Hiding a $50,000 BEC financial fraud in a fake email thread · Blog · Sublime Security

Callback phishing via invoice abuse and distribution list relays · Blog · Sublime Security

B2B freight-forwarding scams on the rise to evade financial fraud crackdowns · Blog · Sublime Security

Detecting malicious AnonymousFox email messages sent from compromised sites · Blog · Sublime Security
Combating GenAI Email Attacks with BERT LLM · Blog · Sublime Security

Payroll Fraud via LLM-Generated Emails · Blog · Sublime Security
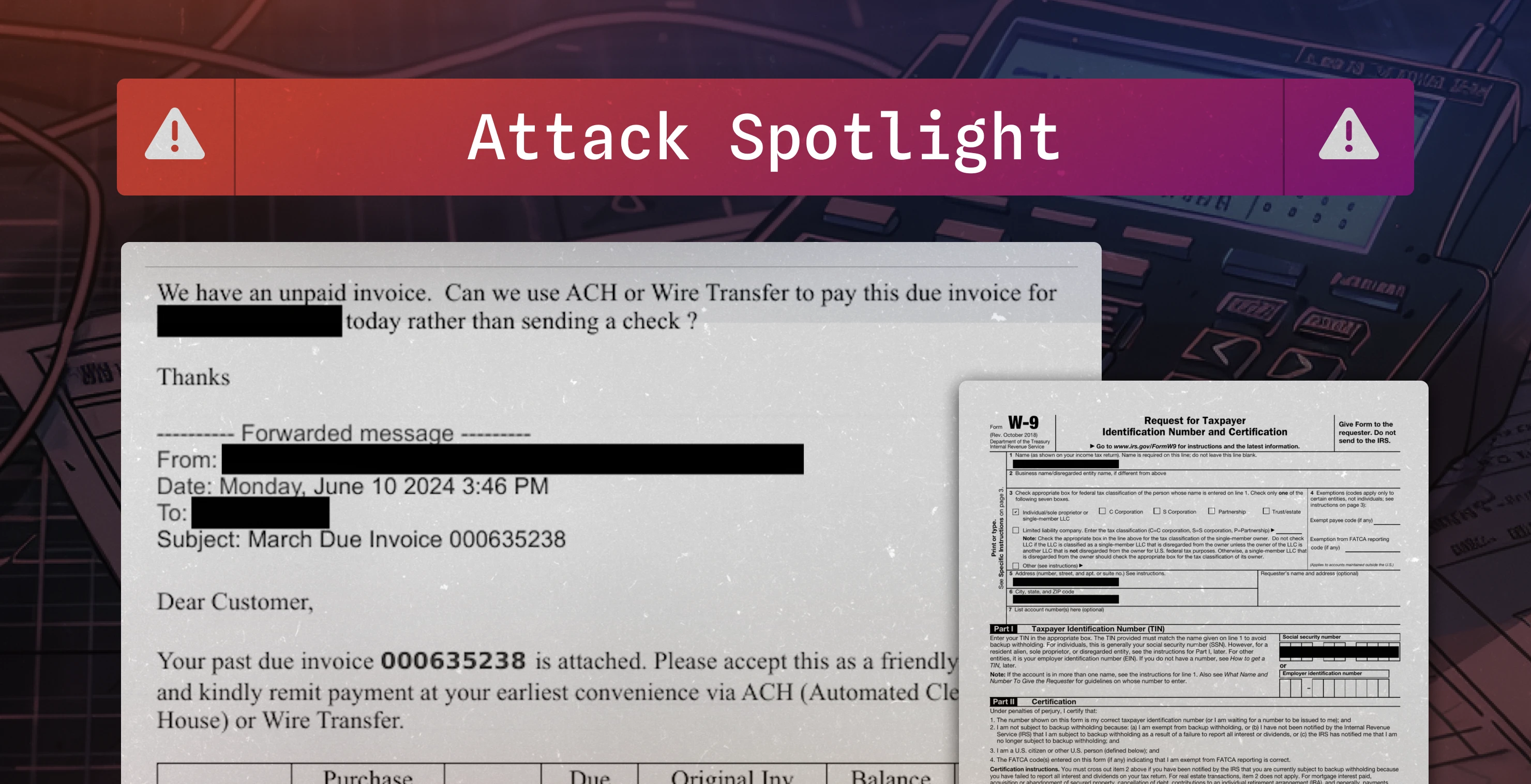
Fake invoice used to conduct $16,800 BEC attempt · Blog · Sublime Security
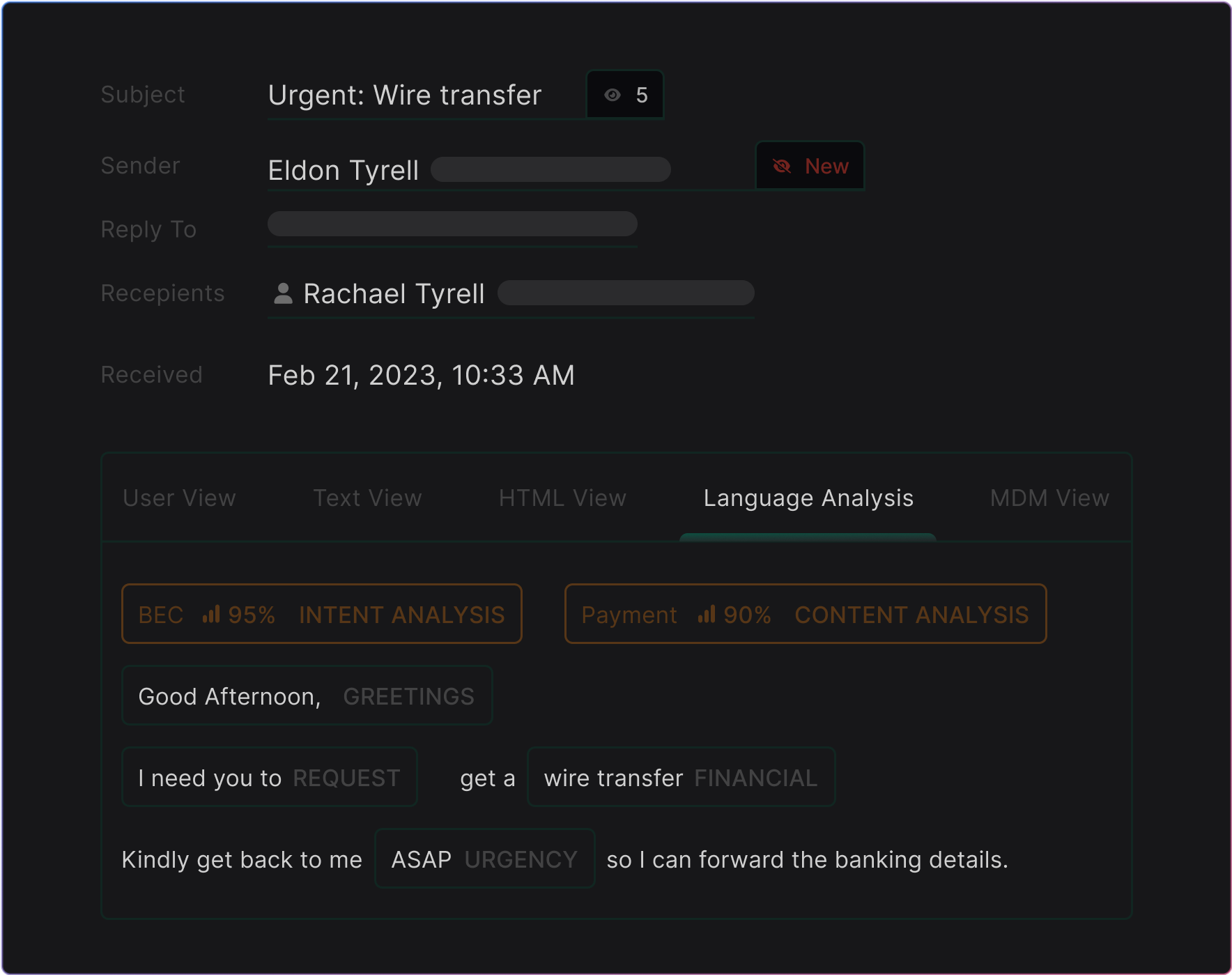
Unmasking BEC attacks using Natural Language Understanding + MQL · Blog · Sublime Security
Tactics & Techniques (19):
Detection Methods (16):
Page 1 of 9