- URL analysis
Attack Types
BEC/Fraud
Callback Phishing
Credential Phishing
Extortion
Malware/Ransomware
Reconnaissance
Spam
Tactics and Techniques
Encryption
Evasion
Exploit
Free email provider
Free file host
Free subdomain host
HTML smuggling
Image as content
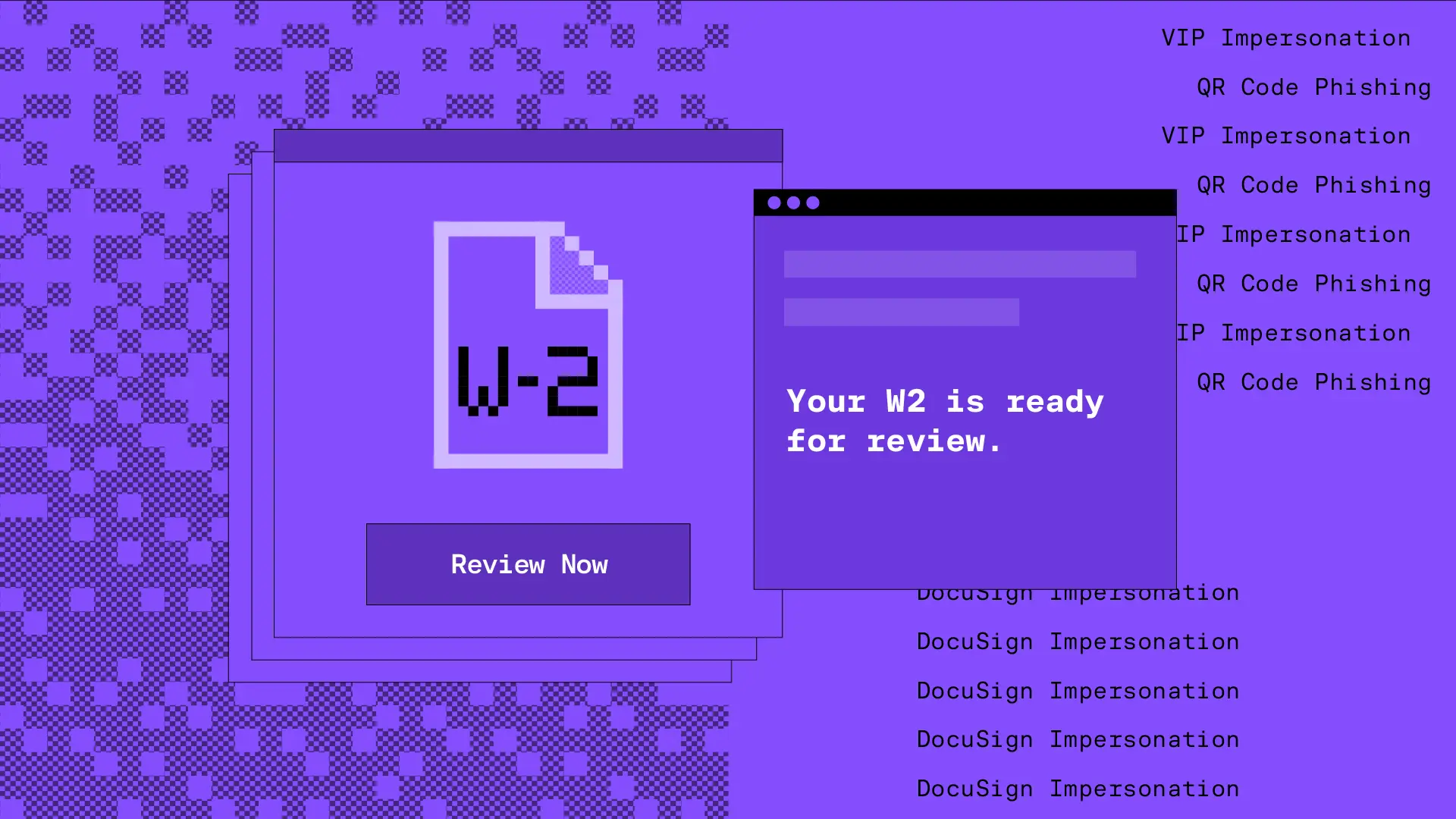
Impersonation: Brand
Impersonation: Employee
Impersonation: VIP
IPFS
ISO
LNK
Lookalike domain
Macros
OneNote
Open redirect
Out of band pivot
PDF
Punycode
QR code
Scripting
Social engineering
Spoofing
Detection Methods
Archive analysis
Content analysis
Computer Vision
Exif analysis
File analysis
Header analysis
HTML analysis
Javascript analysis
Macro analysis
Natural Language Understanding
Optical Character Recognition
OLE analysis
PDF analysis
QR code analysis
Sender analysis
Threat intelligence
URL analysis
URL screenshot
Whois
XML analysis
YARA
Detection Method: URL analysis
URL analysis scans links in emails, attachments, or embedded content to find malicious destinations aimed at stealing your credentials, delivering malware, or launching other types of attacks. This method looks at key factors like the structure of the URL, redirection paths, domain reputation, and what the link shows when clicked.
URL analysis can help you detect:
- Phishing sites pretending to be trusted login pages
- Malicious domains hidden through URL shorteners or redirects
- Login forms on suspicious or newly registered domains
- Brand impersonation using slight domain tweaks (typosquatting or homograph attacks)
- Suspicious URLs with weird characters or unusual patterns
For example, attackers often use redirect chains to hide their final destination from security scanners. With URL analysis, we can follow these redirects to reveal the true destination and assess the potential threat.
Blog Posts
Tax season email attacks: AdWind RATs and Tycoon 2FA phishing kits · Blog · Sublime Security
Hiding a $50,000 BEC financial fraud in a fake email thread · Blog · Sublime Security
Talking phish over turkey · Blog · Sublime Security
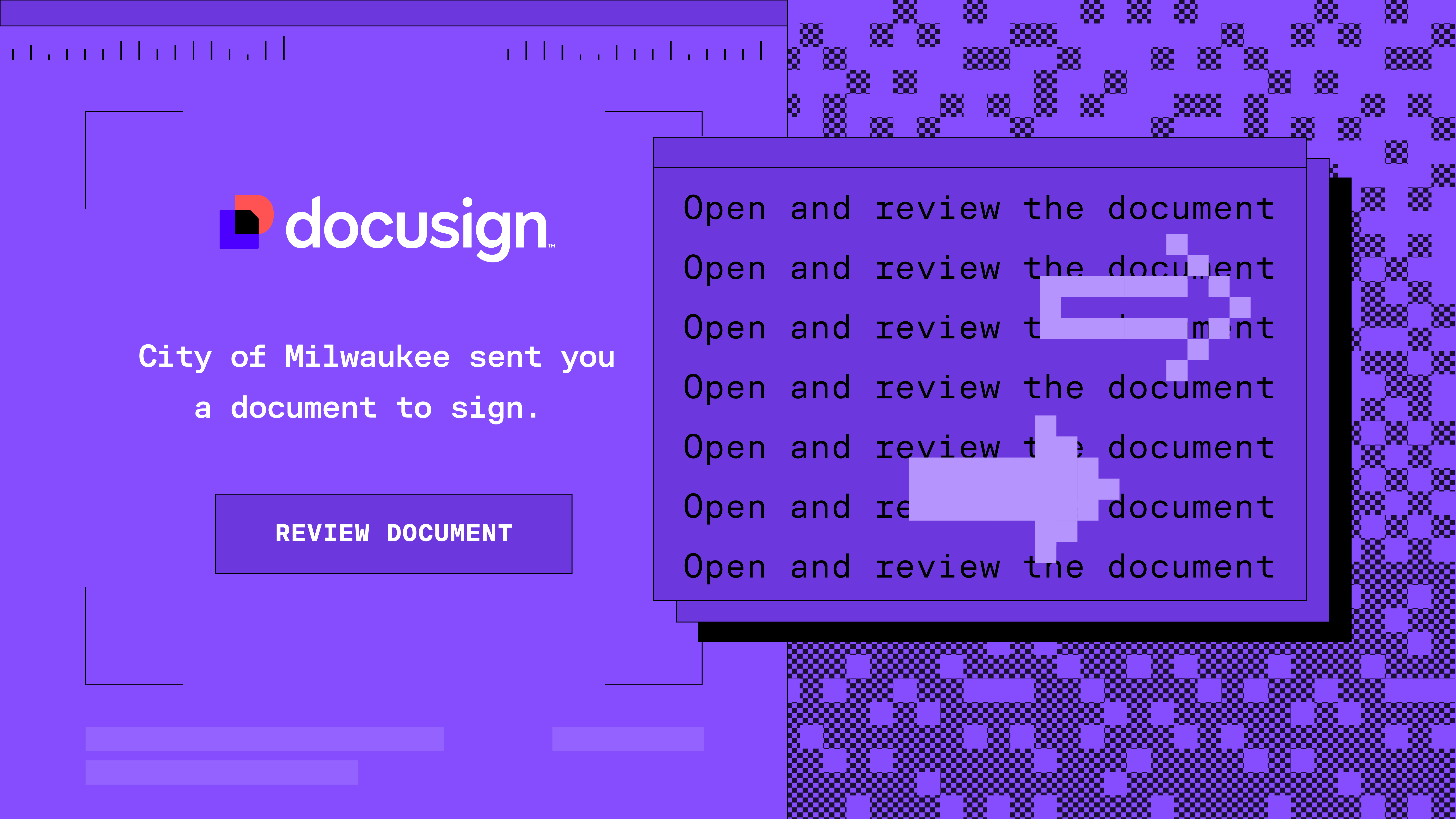
Living Off the Land: Credential Phishing via Docusign abuse · Blog · Sublime Security
Living Off the Land: Callback Phishing via Docusign comment · Blog · Sublime Security

Abusing Discord to deliver Agent Tesla malware · Blog · Sublime Security

Gotta Catch 'Em All: Detecting PikaBot Delivery Techniques · Blog · Sublime Security

QR Code Phishing: Decoding Hidden Threats · Blog · Sublime Security
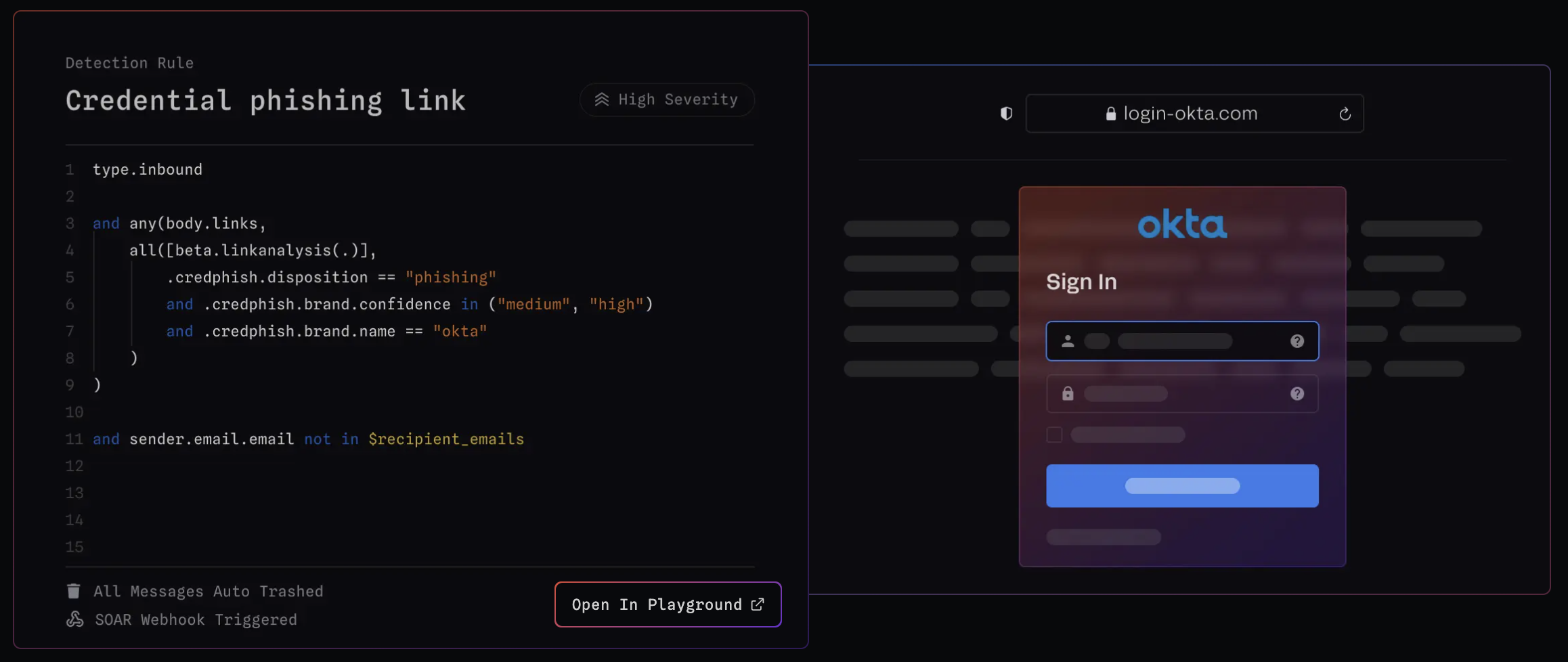
Detecting Credential Phishing using Deep Learning + MQL · Blog · Sublime Security
Tactics & Techniques (25):
Free file host
Social engineering
PDF
Free subdomain host
Impersonation: Brand
Evasion
Image as content
Free email provider
Open redirect
QR code
Encryption
OneNote
Scripting
Lookalike domain
Spoofing
Impersonation: Employee
Credential Phishing
Out of band pivot
IPFS
HTML smuggling
Impersonation: VIP
Exploit
HTML injection
LNK
Punycode
Page 1 of 21