- Social engineering
Attack Types
BEC/Fraud
Callback Phishing
Credential Phishing
Extortion
Malware/Ransomware
Reconnaissance
Spam
Tactics and Techniques
Encryption
Evasion
Exploit
Free email provider
Free file host
Free subdomain host
HTML smuggling
Image as content
Impersonation: Brand
Impersonation: Employee
Impersonation: VIP
IPFS
ISO
LNK
Lookalike domain
Macros
OneNote
Open redirect
Out of band pivot
PDF
Punycode
QR code
Scripting
Social engineering
Spoofing
Detection Methods
Archive analysis
Content analysis
Computer Vision
Exif analysis
File analysis
Header analysis
HTML analysis
Javascript analysis
Macro analysis
Natural Language Understanding
Optical Character Recognition
OLE analysis
PDF analysis
QR code analysis
Sender analysis
Threat intelligence
URL analysis
URL screenshot
Whois
XML analysis
YARA
Tactic or Technique: Social engineering
Social engineering targets people instead of systems. Attackers use persuasion, pressure, or emotional cues to get you to act quickly and bypass security tools without realizing it.
Messages often create urgency, mimic authority figures, or feel familiar enough to lower your guard. An attacker might pose as your manager asking for a quick favor, reference a recent company event, or claim your account is about to be locked. These tricks are designed to feel legitimate and get you to respond without verifying the request.
Common approaches include pretexting, where attackers invent a believable scenario; baiting, where they offer something enticing; or quid pro quo, where they offer help in exchange for access. Even a single successful interaction can lead to broader compromise, including data theft, ransomware, or a full network breach.
Blog Posts

Credential phishing Charles Schwab account holders with 2FA bypass · Blog · Sublime Security
Hiding a $50,000 BEC financial fraud in a fake email thread · Blog · Sublime Security

Callback phishing via invoice abuse and distribution list relays · Blog · Sublime Security
Talking phish over turkey · Blog · Sublime Security
Hidden credential phishing within EML attachments · Blog · Sublime Security
Living Off the Land: Credential Phishing via Docusign abuse · Blog · Sublime Security
Living Off the Land: Callback Phishing via Docusign comment · Blog · Sublime Security

Adversarial ML: Extortion via LLM Manipulation Tactics · Blog · Sublime Security
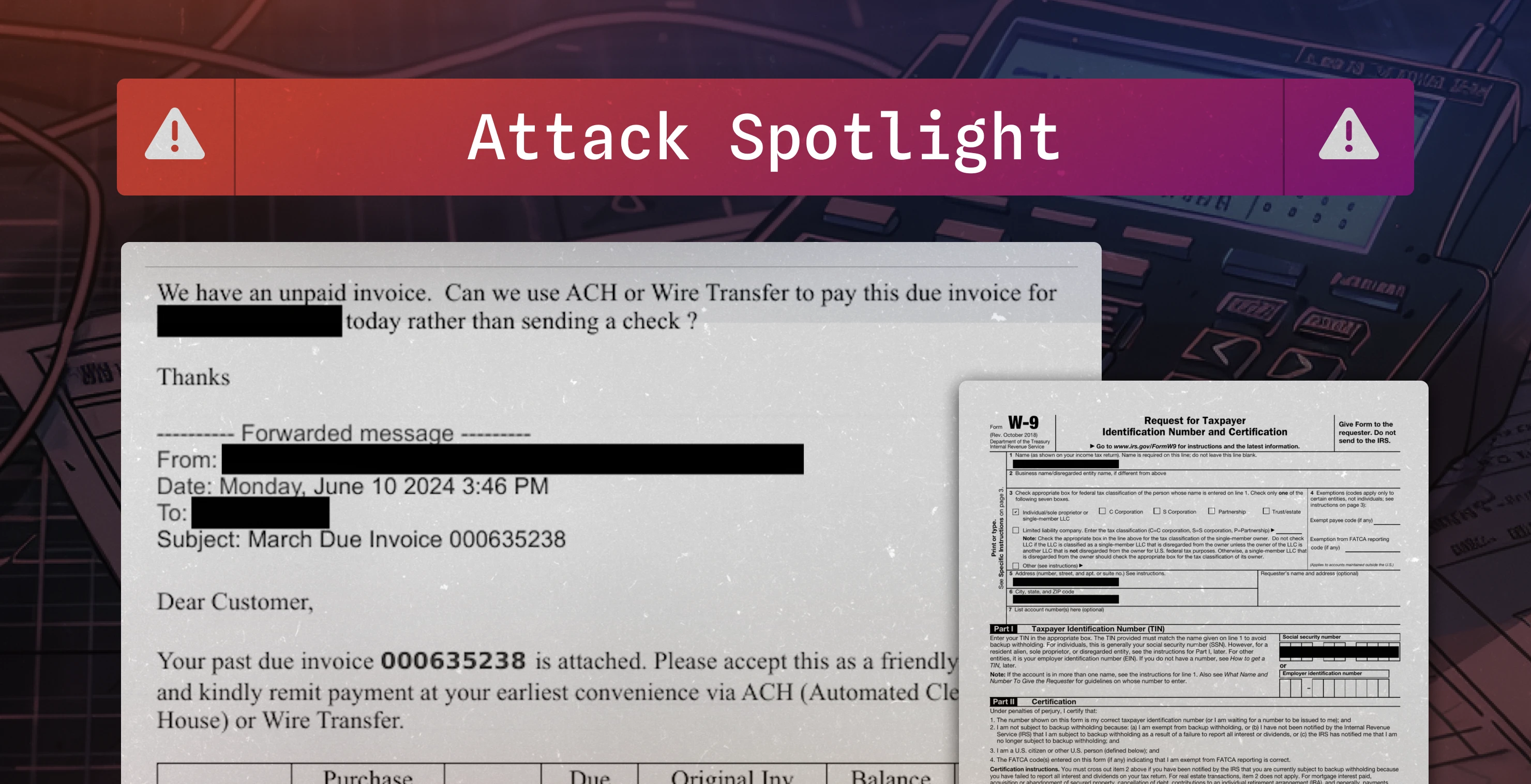
Fake invoice used to conduct $16,800 BEC attempt · Blog · Sublime Security

Gotta Catch 'Em All: Detecting PikaBot Delivery Techniques · Blog · Sublime Security
Detection Methods (20):
Natural Language Understanding
Sender analysis
Content analysis
URL analysis
File analysis
Optical Character Recognition
Exif analysis
Header analysis
Computer Vision
Whois
HTML analysis
YARA
Archive analysis
URL screenshot
Threat intelligence
QR code analysis
Macro analysis
Javascript analysis
OLE analysis
XML analysis
Page 1 of 25