Attack Types
BEC/Fraud
Callback Phishing
Credential Phishing
Extortion
Malware/Ransomware
Reconnaissance
Spam
Tactics and Techniques
Encryption
Evasion
Exploit
Free email provider
Free file host
Free subdomain host
HTML smuggling
Image as content
Impersonation: Brand
Impersonation: Employee
Impersonation: VIP
IPFS
ISO
LNK
Lookalike domain
Macros
OneNote
Open redirect
Out of band pivot
PDF
Punycode
QR code
Scripting
Social engineering
Spoofing
Detection Methods
Archive analysis
Content analysis
Computer Vision
Exif analysis
File analysis
Header analysis
HTML analysis
Javascript analysis
Macro analysis
Natural Language Understanding
Optical Character Recognition
OLE analysis
PDF analysis
QR code analysis
Sender analysis
Threat intelligence
URL analysis
URL screenshot
Whois
XML analysis
YARA
Tactic or Technique: PDF
Attackers use PDF files to deliver malicious content in a format that most people see as safe. These files often appear to be invoices, contracts, or notifications and can include embedded JavaScript, links, or QR codes that lead to phishing sites or malware downloads.
One common example is a fake DocuSign PDF that asks you to scan a QR code or click a link to view a document. The moment you interact, you're taken to a phishing site designed to steal your credentials or deliver malware.
Because PDFs are trusted and can difficult to inspect, they give attackers a way to hide dangerous content behind a familiar format. That trust, combined with limited scanning by some security tools, gives malicious PDFs a clear path into inboxes and environments.
Blog Posts
Tax season email attacks: AdWind RATs and Tycoon 2FA phishing kits · Blog · Sublime Security

Callback phishing via invoice abuse and distribution list relays · Blog · Sublime Security
Talking phish over turkey · Blog · Sublime Security

Abusing Discord to deliver Agent Tesla malware · Blog · Sublime Security
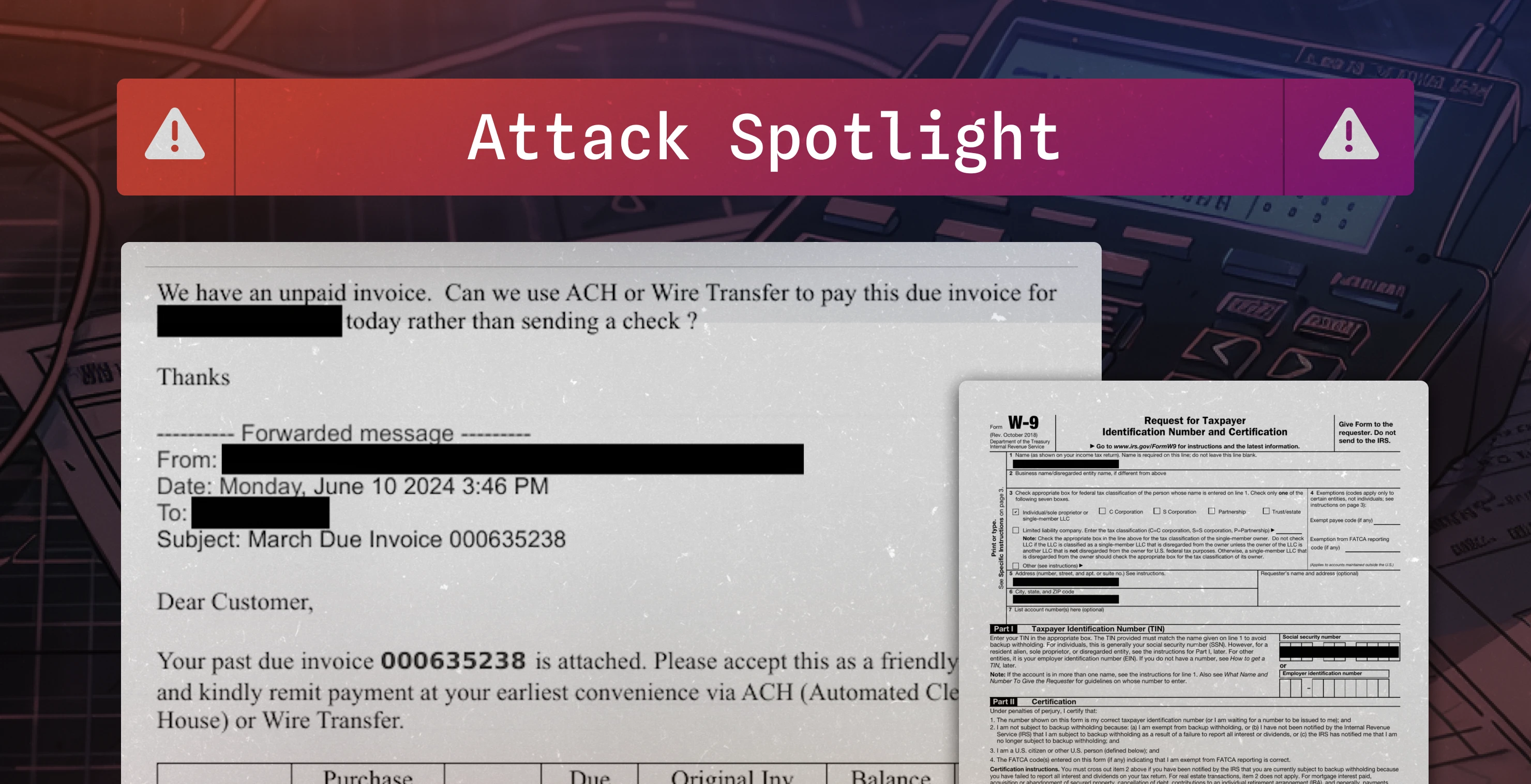
Fake invoice used to conduct $16,800 BEC attempt · Blog · Sublime Security

Gotta Catch 'Em All: Detecting PikaBot Delivery Techniques · Blog · Sublime Security

Call Me Maybe? The Rise of Callback Phishing Emails · Blog · Sublime Security
Detecting QakBot: WSF attachments, OneNote files, and generic attack surface reduction · Blog · Sublime Security
Detection Methods (16):
Page 1 of 4